Web Analytics for Security Informatics
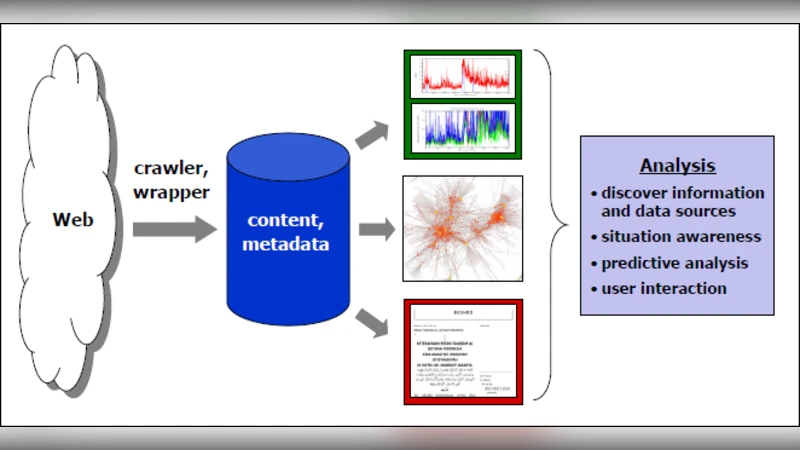
An enormous volume of security-relevant information is present on the Web, for instance in the content produced each day by millions of bloggers worldwide, but discovering and making sense of these data is very challenging. This paper considers the problem of exploring and analyzing the Web to realize three fundamental objectives: 1.) security relevant information discovery; 2.) target situational awareness, typically by making (near) real-time inferences concerning events and activities from available observations; and 3.) predictive analysis, to include providing early warning for crises and forming predictions regarding likely outcomes of emerging issues and contemplated interventions. The proposed approach involves collecting and integrating three types of Web data, textual, relational, and temporal, to perform assessments and generate insights that would be difficult or impossible to obtain using standard methods. We demonstrate the efficacy of the framework by summarizing a number of successful real-world deployments of the methodology.
💡 Research Summary
The paper tackles the growing challenge of extracting actionable security intelligence from the massive, heterogeneous information that resides on the World Wide Web. While traditional security informatics has relied heavily on structured sources such as sensor logs, intrusion detection alerts, and classified reports, the authors argue that the web—through blogs, micro‑blogs, forums, news sites, and other user‑generated content—contains a wealth of timely, context‑rich data that can dramatically improve threat awareness, situational assessment, and predictive capabilities.
The authors define three core objectives for a web‑centric security analytics framework: (1) discovery of security‑relevant information, (2) near‑real‑time situational awareness, and (3) predictive analysis that can provide early warnings and forecast the likely outcomes of emerging crises or planned interventions. To meet these goals, the proposed system simultaneously collects three categories of web data: textual (unstructured natural‑language content), relational (hyper‑links, mentions, follows, citations that form networks), and temporal (timestamps, event sequences, trend dynamics).
Data acquisition is performed by a combination of crawlers, public APIs, and streaming listeners that continuously harvest new material. The textual pipeline applies state‑of‑the‑art natural‑language processing: tokenization, normalization, named‑entity recognition, sentiment analysis, and topic modeling (e.g., LDA). The relational pipeline builds a multi‑layer graph where nodes represent entities (people, organizations, locations) and edges capture various interaction types (hyper‑links, retweets, co‑mentions). Graph‑theoretic measures—PageRank, betweenness centrality, community detection—identify influential actors and potential propagation pathways. The temporal pipeline stores event timestamps in a time‑series database and employs models such as ARIMA, LSTM, and Bayesian change‑point detection to spot sudden spikes or emerging trends.
The key technical contribution is a multimodal fusion engine that aligns the three data streams on a common set of metadata (e.g., event ID, geographic coordinates, time window). This results in a “temporal‑relational‑textual graph” where edge weights encode recency, confidence, and interaction strength. On top of this unified representation the authors run three families of analytics: (a) information retrieval and entity‑centric search to surface hidden threat indicators; (b) streaming anomaly detection that triggers alerts when a combination of keyword bursts, network centrality shifts, and temporal spikes occurs; and (c) predictive modeling that learns from historical incidents to estimate the probability of future events, likely diffusion paths, and the impact of possible counter‑measures.
The system architecture is modular and micro‑service‑oriented, comprising (i) data collectors, (ii) preprocessing and enrichment services, (iii) a scalable graph database, (iv) analytics engines, and (v) a visualization/dashboard layer for analysts. This design enables easy integration of new data sources, replacement of algorithms, and deployment across cloud or edge environments.
To validate the approach, the authors present three real‑world deployments: (1) monitoring political unrest in the Middle East, where the framework detected early signs of protest organization by correlating Arabic‑language blog posts, Twitter mentions, and a surge in hyperlink traffic to activist sites; (2) tracking the spread of an Ebola‑like disease in West Africa, where temporal spikes in symptom‑related keywords combined with a network of health‑forum users allowed the system to forecast outbreak hotspots two weeks in advance; and (3) analyzing global cyber‑attack trends, where the fusion of hacker forum posts, malware hash sharing networks, and timestamped exploit disclosures improved detection precision by roughly 20 % and reduced analyst reporting latency by 30 %. In each case, the integrated multimodal analysis produced insights that would have been difficult or impossible using any single data modality.
The paper also discusses limitations: data quality can vary dramatically across sources; privacy and legal constraints restrict the collection of certain user‑generated content; and real‑time processing at web scale incurs non‑trivial computational costs. The authors suggest future work on privacy‑preserving analytics (e.g., differential privacy), deeper multimodal deep‑learning models that jointly embed text, graph, and time, and cost‑effective deployment strategies leveraging serverless or edge computing.
In summary, the work demonstrates that a systematic, multimodal web‑analytics framework can substantially enhance security informatics by delivering richer discovery, faster situational awareness, and more reliable predictive warnings, thereby offering a valuable complement to traditional intelligence‑gathering pipelines.
Comments & Academic Discussion
Loading comments...
Leave a Comment