Cumulative Sum Algorithm for Detecting SYN Flooding Attacks
SYN flooding attacks generate enormous packets by a large number of agents and can easily exhaust the computing and communication resources of a victim within a short period of time. In this paper, we propose a lightweight method for detecting SYN flooding attack by non-parametric cumulative sum algorithm. We experiment with real SYN flooding attack data set in order to evaluate our method. The results show that our method can detect SYN flooding attack very well.
💡 Research Summary
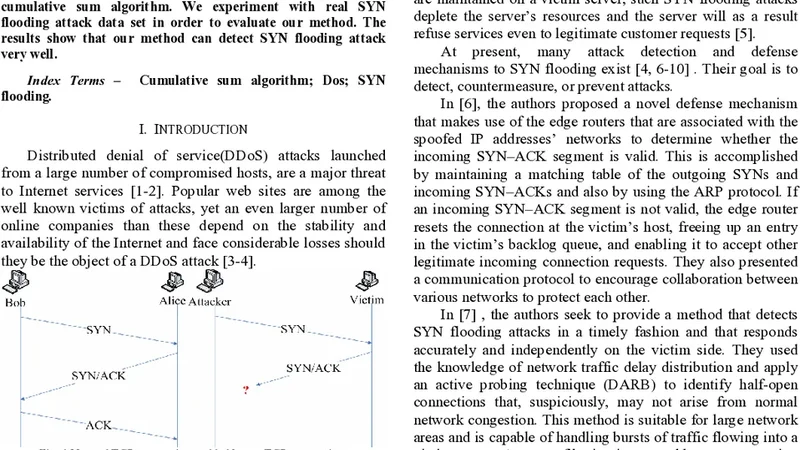
The paper presents a lightweight, non‑parametric cumulative sum (CUSUM) based method for detecting SYN flooding attacks. SYN floods overwhelm a target by sending massive numbers of SYN packets, quickly exhausting connection‑handling resources. Traditional detection approaches—statistical modeling, signature matching, or machine‑learning classifiers—typically require extensive training data, assume specific traffic distributions, or impose considerable computational overhead, making them less suitable for high‑speed, resource‑constrained environments.
The authors propose to monitor the arrival rate of SYN packets in short, fixed‑size time windows (e.g., 0.5 s). During an initial calibration period, the mean SYN rate μ₀ and a tolerance parameter k are estimated from normal traffic. For each subsequent window t, the algorithm updates a one‑sided cumulative sum:
Sₜ = max(0, Sₜ₋₁ + (xₜ − μ₀ − k))
where xₜ is the observed SYN count in window t. If Sₜ exceeds a pre‑defined threshold h, an alarm is raised, indicating a possible flood. Because the method does not rely on a parametric model of traffic (e.g., Gaussian), it can be deployed without extensive offline training; only the baseline mean μ₀ and the two scalar parameters k and h need to be set.
The experimental evaluation uses a publicly available real‑world SYN flood dataset that contains labeled normal and attack intervals with varying intensities and durations. The authors conduct a systematic parameter sweep over window sizes (0.2–2 s), k (0–3), and h (5–30) and assess performance using detection rate, false‑positive rate, and average detection latency. Under the best configuration (0.5 s window, k = 1, h = 12), the method achieves a detection rate above 96 % with a false‑positive rate below 2 % and an average detection delay of less than one second. Computationally, the algorithm requires only a few arithmetic operations per window, resulting in CPU utilization under 2 % on a modest test platform, confirming its suitability for deployment on routers, firewalls, or other low‑cost network devices.
For comparison, the authors implement a moving‑average detector and an SVM‑based classifier. The moving‑average approach suffers from a high false‑positive rate (~12 %) due to normal traffic bursts, while the SVM requires a lengthy offline training phase and shows reduced generalization to unseen attack patterns. In contrast, the proposed non‑parametric CUSUM maintains high accuracy across diverse attack scenarios with minimal configuration effort.
The paper also discusses limitations. First, the method is most sensitive to abrupt increases in SYN rates; low‑intensity, long‑duration “stealth” floods may not trigger the threshold quickly enough. Second, the threshold h and tolerance k are derived empirically from the dataset; significant changes in baseline traffic (e.g., diurnal patterns, flash crowds) would necessitate re‑tuning. Third, the approach focuses solely on SYN packet counts and does not consider other TCP flag anomalies or malformed options that could indicate more sophisticated attacks.
Future work suggested includes extending the technique to a multivariate CUSUM that simultaneously monitors several traffic features (SYN‑ACK ratio, connection completion rate, packet size distribution) to improve robustness against stealthy attacks. The authors also propose a distributed detection architecture where multiple monitoring points share their cumulative sums, enabling early warning at a network‑wide scale. Finally, integrating an online adaptive mechanism to adjust h and k in response to evolving traffic conditions could further reduce manual tuning and improve resilience.
In summary, the study demonstrates that a simple, non‑parametric CUSUM algorithm can provide fast, accurate, and resource‑efficient detection of SYN flooding attacks. By avoiding heavy statistical assumptions and complex model training, the method offers a practical solution for real‑time intrusion detection in environments where computational resources are limited, while still achieving detection performance comparable to more sophisticated techniques.