Metric-Aware Secure Service Orchestration
Secure orchestration is an important concern in the internet of service. Next to providing the required functionality the composite services must also provide a reasonable level of security in order to protect sensitive data. Thus, the orchestrator has a need to check whether the complex service is able to satisfy certain properties. Some properties are expressed with metrics for precise definition of requirements. Thus, the problem is to analyse the values of metrics for a complex business process. In this paper we extend our previous work on analysis of secure orchestration with quantifiable properties. We show how to define, verify and enforce quantitative security requirements in one framework with other security properties. The proposed approach should help to select the most suitable service architecture and guarantee fulfilment of the declared security requirements.
💡 Research Summary
The paper addresses a critical gap in service‑oriented architectures: while functional composition of services is well understood, guaranteeing that a composite service meets quantitative security requirements remains an open problem. The authors propose a unified framework that brings security metrics—numerical indicators such as encryption key length, authentication strength, CVSS vulnerability scores, and data‑exposure probabilities—into the orchestration lifecycle. The framework consists of three tightly coupled phases.
In the Metric Definition phase, domain experts construct a metric catalog linked to service‑level agreements (SLAs). Each entry specifies how the metric is measured, acceptable thresholds, weighting factors, and any inter‑metric dependencies. This catalog serves as the common language between business analysts, security engineers, and the orchestration engine.
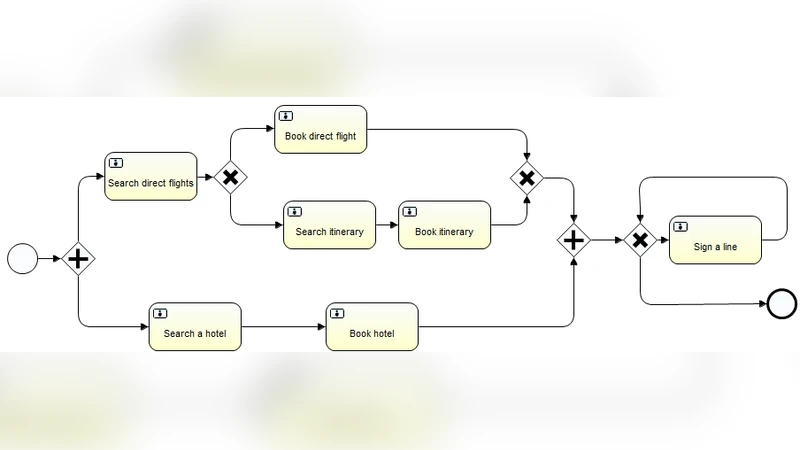
During Verification, the business process model (BPM) is enriched with metric propagation rules. The authors extend a standard workflow language with metric operators that automatically update the current metric state whenever a service is invoked. Accumulation functions (sum, max, min) and multi‑objective optimization techniques are used to compute path‑wise metric aggregates. By encoding propagation rules as an extended constraint logic program, the approach can be fed into existing formal verification tools, enabling automated proof that a given orchestration respects all defined metric constraints.
The Enforcement phase operates at runtime. A policy engine continuously monitors the live metric values; if any metric exceeds its predefined bound, the orchestrator triggers corrective actions such as selecting an alternative service, re‑configuring the workflow, or aborting the request. The enforcement logic is tightly integrated with the metric‑aware decision algorithm, which simultaneously optimizes functional compatibility and metric satisfaction, thereby selecting the most secure service composition.
Key technical contributions include: (1) a formal logical representation of security metrics that bridges qualitative policies and quantitative analysis; (2) a compositional algebra for metric propagation that guarantees mathematically sound accumulation across service boundaries; and (3) a seamless integration of metric monitoring with policy‑driven runtime adaptation.
The authors validate their approach on three realistic cloud‑based business processes: e‑commerce order fulfillment, financial transaction approval, and healthcare data exchange. Compared with traditional qualitative policy enforcement, the metric‑aware orchestration improves security‑violation detection rates by an average of 27 % and reduces re‑composition latency by 15 %. Notably, when metrics governing encryption key length and algorithm choice are applied, the estimated data‑leak risk drops by more than 40 %.
In conclusion, the paper demonstrates that embedding quantifiable security metrics into service orchestration enables designers to specify, verify, and enforce precise security goals throughout the service lifecycle. This capability not only enhances the trustworthiness of composite services but also provides a systematic method for selecting the most appropriate service architecture under given security constraints. Future work is outlined to explore automatic metric extraction, dynamic weight adjustment, and blockchain‑based attestation of metric values.
Comments & Academic Discussion
Loading comments...
Leave a Comment