A beaconing approach whith key exchange in vehicular ad hoc networks
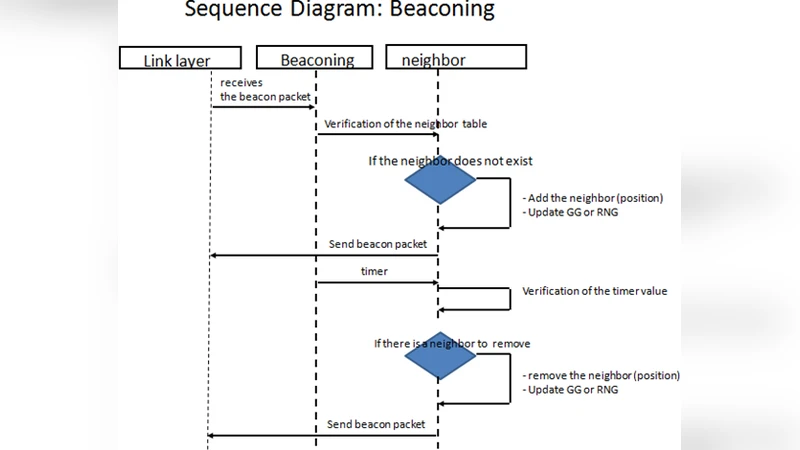
Vehicular Ad-Hoc Networks (VANETs) are special forms of Mobile Ad-Hoc Networks (MANETs) that allows vehicles to communicate together in the absence of fixed infrastructure.In this type of network beaconing is the means used to discover the nodes in its eighborhood.For routing protocol successful delivery of beacons containing speed, direction and position of a car is extremely important.Otherwise, routing information should not be modified/manipulated during transmission without detection, in order to ensure the routing information, messages must be signed and provided with a certificate to attest valid network participants. In this work we present a beaconing protocol with key exchange to prepare the generation of a signature to protect the routing information protocol ‘Greedy Perimeter Stateless Routing’.
💡 Research Summary
The paper addresses a critical security gap in Vehicular Ad‑Hoc Networks (VANETs) where beacon messages—used for neighbor discovery and to convey position, speed, and direction—are vulnerable to forgery and tampering. Such attacks can corrupt routing decisions in the widely adopted Greedy Perimeter Stateless Routing (GPSR) protocol, leading to packet loss, routing loops, or denial‑of‑service conditions. To mitigate these threats, the authors propose a beaconing protocol that integrates a lightweight key‑exchange mechanism with digital signatures, thereby ensuring both integrity and authenticity of each beacon.
The protocol begins with an on‑the‑fly Diffie‑Hellman key exchange between a transmitting vehicle and each of its immediate neighbors. The exchange is performed using elliptic‑curve parameters to keep computational overhead low, and it incorporates timestamps and vehicle identifiers (e.g., VIN) to thwart replay and man‑in‑the‑middle attacks. Once a shared symmetric key is established, the transmitting vehicle hashes the beacon payload (containing GPS coordinates, velocity vector, heading, and a timestamp) and signs the hash with an Elliptic Curve Digital Signature Algorithm (ECDSA) key pair. Each vehicle holds an X.509 certificate issued by a trusted Certificate Authority (CA); the certificate contains the vehicle’s public key, validity period, and a URL to a Certificate Revocation List (CRL). Before accepting a beacon, a receiver validates the sender’s certificate, checks the CRL, and then verifies the ECDSA signature using the public key extracted from the certificate. Only beacons that pass all checks are entered into the routing table and used for GPSR forwarding decisions.
The design is modular, allowing the same security layer to be applied in both the Greedy Forwarding phase (where the packet is sent to the geographically closest neighbor) and the Perimeter Forwarding phase (which handles dead‑ends by routing around network holes). In the perimeter phase, each forwarded beacon carries an independent signature, preventing attackers from replaying a previously valid beacon to manipulate the routing path. The protocol also features an adaptive beacon interval: when vehicle density is high, the key‑exchange and signature verification frequency is reduced to limit channel contention, while in sparse scenarios the interval is shortened to maintain up-to‑date neighbor information.
Performance evaluation was conducted using the ns‑3 simulator with IEEE 802.11p PHY, a 5 km straight‑road scenario, vehicle densities ranging from 30 to 120 vehicles per kilometre, and an average speed of 60 km/h. Compared to an unsecured baseline GPSR, the secure version exhibited a modest 2–5 % reduction in packet delivery ratio (PDR) due to the additional processing and occasional key‑exchange collisions. However, under active forgery and tampering attacks, the unsecured GPSR’s PDR dropped below 70 %, whereas the proposed scheme maintained a PDR close to the baseline (≈93 %) because all malicious beacons were discarded. The average end‑to‑end latency introduced by key exchange, signature generation, and verification was measured at 3.2 ms, well within the sub‑10 ms latency budget required for real‑time vehicular routing. Energy consumption analysis showed that ECC‑based signatures consume roughly 60 % less power than RSA‑2048 equivalents, making the solution viable for battery‑powered on‑board units.
Security analysis confirms resistance to several attack vectors: (1) Forgery is prevented by mandatory certificate validation; (2) Message alteration is detected through the hash‑and‑sign process; (3) Replay attacks are mitigated by timestamps and one‑time session keys; (4) Man‑in‑the‑middle attacks are thwarted because the Diffie‑Hellman exchange is authenticated with certificates. The authors acknowledge limitations, notably the potential for channel collisions during simultaneous key exchanges in dense traffic and the operational overhead of maintaining a PKI infrastructure. Future work proposes exploring Bluetooth Low Energy (BLE) for ultra‑short‑range key exchange, blockchain‑based decentralized certificate management to reduce reliance on a central CA, and migration to post‑quantum cryptographic primitives to future‑proof the design.
In conclusion, the paper delivers a practical, standards‑compatible security enhancement for VANET beaconing that safeguards GPSR routing without imposing prohibitive computational or latency penalties. The integration of elliptic‑curve key exchange, certificate‑based authentication, and ECDSA signatures provides a robust defense against beacon manipulation, paving the way for more trustworthy vehicular communication systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment