A Heuristic Reputation Based System to Detect Spam activities in a Social Networking Platform, HRSSSNP
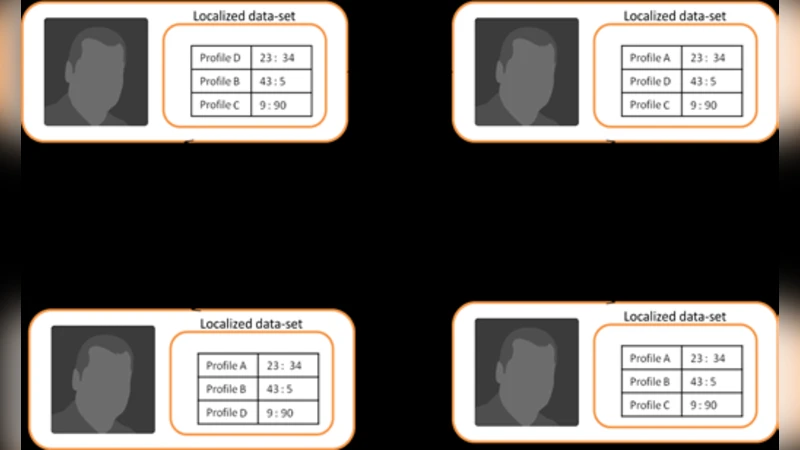
The introduction of the social networking platform has drastically affected the way individuals interact. Even though most of the effects have been positive, there exist some serious threats associated with the interactions on a social networking website. A considerable proportion of the crimes that occur are initiated through a social networking platform [5]. Almost 33% of the crimes on the internet are initiated through a social networking website [5]. Moreover activities like spam messages create unnecessary traffic and might affect the user base of a social networking platform. As a result preventing interactions with malicious intent and spam activities becomes crucial. This work attempts to detect the same in a social networking platform by considering a social network as a weighted graph wherein each node, which represents an individual in the social network, stores activities of other nodes with respect to itself in an optimized format which is referred to as localized data-set. The weights associated with the edges in the graph represent the trust relationship between profiles. The weights of the edges along with the localized data-set is used to infer whether nodes in the social network are compromised and are performing spam or malicious activities.
💡 Research Summary
The paper proposes a heuristic reputation‑based system (HRSSSNP) for detecting spam and malicious activities on social networking platforms. The authors model a social network as a weighted graph where vertices represent users and edges encode a trust value between two users. Each vertex maintains a “localized data‑set,” a compact log that records the activities of its immediate neighbors together with the associated trust scores.
The detection mechanism consists of two iterative heuristics. First, a trust propagation step updates a node’s trust value by taking a weighted average of the trust scores received from its neighbors; contributions from low‑trust neighbors are attenuated by a damping factor. This step runs periodically, allowing the trust landscape to evolve dynamically across the network. Second, a spam detection step flags any incoming interaction (messages, friend requests, link clicks, etc.) whose observed trust deviation from the node’s localized baseline exceeds a predefined threshold. When the number of flagged events for a node surpasses a second threshold, the node is classified as compromised, and an alert is propagated to its neighbors, thereby informing the entire network of a potential threat.
Key advantages of the approach include: (1) Distributed processing – because each node stores and processes its own data, the central server’s load is minimized and real‑time updates are feasible; (2) Fine‑grained trust representation – weighted edges allow the system to capture subtle differences in relationship strength, improving detection of gradually emerging malicious behavior compared to binary black‑list schemes; (3) Scalability – the algorithm relies only on local information and simple linear computations, making it applicable to large‑scale networks with modest computational overhead.
The authors also acknowledge several limitations. The initial assignment of trust weights is critical; inaccurate seeds can cause erroneous propagation. The size of localized data‑sets may grow rapidly with user activity, raising storage and transmission costs. The system is vulnerable to “trust manipulation” attacks where adversaries artificially inflate their trust scores. Moreover, the paper lacks empirical validation on real‑world social network data, providing only a conceptual description without performance metrics.
Future work suggested includes automatic initialization and dynamic adjustment of trust values, compression techniques for the localized data‑sets, mechanisms to detect and mitigate trust‑inflation attacks, and extensive experiments on large‑scale platforms to quantify detection accuracy, false‑positive rates, and overhead. In summary, HRSSSNP offers an interesting decentralized framework for spam detection that leverages trust propagation on weighted graphs, but its practical effectiveness remains to be demonstrated through rigorous empirical evaluation.
Comments & Academic Discussion
Loading comments...
Leave a Comment