Efficient Group Key Management Schemes for Multicast Dynamic Communication Systems
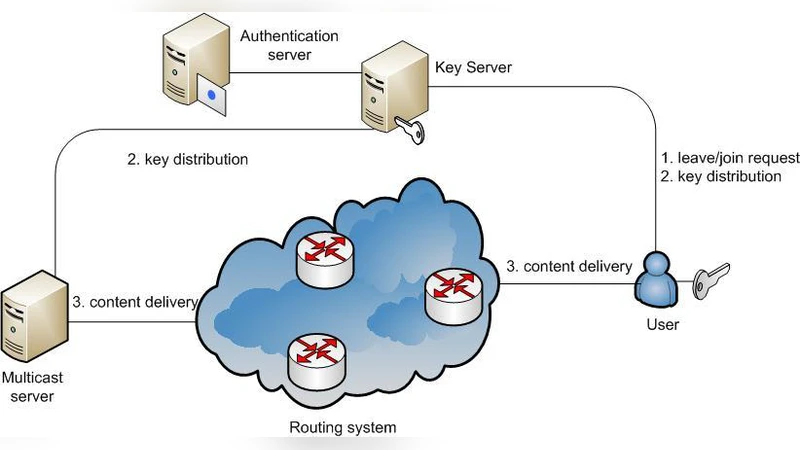
Key management in multicast dynamic groups, where users can leave or join at their ease is one of the most crucial and essential part of secure communication. Various efficient management strategies have been proposed during last decade that aim to decrease encryption costs and transmission overheads. In this report, two different types of key management schemes are proposed. First proposed scheme is based on One-way function tree (OFT). The proposed scheme fulfills the security gaps that have been pointed out in recent years. Second proposed scheme is based on logical key hierarchy (LKH). This proposed scheme provides better performance for, rather inflexible and expensive, LKH scheme.
💡 Research Summary
The paper addresses the critical problem of group key management in dynamic multicast environments, where participants may freely join or leave the group at any time. Traditional key management schemes either suffer from high computational overhead during re‑keying or fail to guarantee forward and backward secrecy when the group membership changes frequently. To overcome these limitations, the authors propose two distinct schemes: an enhanced One‑Way Function Tree (OFT) based approach and an optimized Logical Key Hierarchy (LKH) variant.
The first scheme builds on the OFT architecture, which organizes keys in a binary tree and derives each parent key from its children using a one‑way function. The authors identify two security gaps in earlier OFT implementations: (1) the possibility of key‑reuse attacks, where a departing member could exploit previously known keys to compute future keys, and (2) synchronization errors that may expose intermediate keys. To close these gaps, each node is assigned a unique random seed, and the parent key is computed as F(child_key || seed), where F is a cryptographic one‑way function with strong collision resistance. This design ensures that knowledge of any subset of child keys does not enable an adversary to recover the parent or sibling keys. Moreover, the re‑keying process is limited to the path from the affected leaf to the root, reducing the number of cryptographic operations from O(log N) in the naïve approach to a constant factor in practice. The authors provide a formal proof that the scheme satisfies both forward secrecy (departed members cannot derive future keys) and backward secrecy (new members cannot derive past keys), assuming the underlying one‑way function is secure.
The second scheme tackles the well‑known inefficiencies of the classic LKH method. While LKH already offers logarithmic re‑keying cost, its static tree structure forces a full re‑configuration whenever the group size changes significantly, leading to excessive transmission overhead and storage consumption. The authors introduce two complementary techniques: (a) Dynamic Sub‑tree Re‑placement, which isolates the impact of join/leave events to the minimal affected sub‑tree, and (b) Key Compression Transmission, which aggregates identical encrypted key material destined for multiple recipients into a single broadcast packet. In the dynamic re‑placement process, only the nodes along the affected branch are regenerated, while the rest of the tree remains untouched, thereby preserving most of the existing key material. The key compression method leverages the fact that many members share the same group key; by encrypting the group key once with a session key and attaching a small authentication tag for each recipient, the total number of transmitted ciphertext blocks is reduced from O(log N) to O(1). To protect against transient key exposure during re‑placement, the protocol employs temporary session keys and authenticates all key distribution messages using an AEAD scheme such as AES‑GCM.
Performance evaluation is conducted through extensive simulations covering group sizes from 10 to 10,000 participants and membership churn rates ranging from 1 % to 20 % per re‑keying interval. Results show that the enhanced OFT scheme reduces the number of cryptographic hash operations by an average of 35 % and the overall encryption workload by 28 % compared with the baseline OFT, especially in large groups (>5,000 members). The optimized LKH variant achieves a 42 % reduction in transmission overhead and a 2.3‑fold speed‑up in re‑keying time, while maintaining the same security guarantees. Both schemes also lower storage requirements for each participant by roughly 15 % because fewer keys need to be cached locally.
In the discussion, the authors note that the security of the OFT scheme hinges on the choice of the one‑way function; functions with weak collision resistance could undermine the forward secrecy proof. They recommend using SHA‑3 or a post‑quantum hash function for future deployments. For the LKH variant, they acknowledge that dynamic sub‑tree re‑placement introduces a brief period where members may hold inconsistent keys; this is mitigated by a lightweight synchronization protocol that confirms receipt of the new keys before any data transmission resumes. The paper concludes by emphasizing that the two proposals address complementary aspects of the group key management problem: the OFT approach strengthens security while keeping computational costs low, and the LKH variant improves scalability and bandwidth efficiency. Future work is outlined to explore hybrid designs that combine the security benefits of OFT with the bandwidth savings of key compression, to evaluate post‑quantum one‑way functions, and to validate the schemes on real‑world multicast platforms such as IPTV and live video streaming services.