Shaping Operations to Attack Robust Terror Networks
Security organizations often attempt to disrupt terror or insurgent networks by targeting “high value targets” (HVT’s). However, there have been numerous examples that illustrate how such networks are able to quickly re-generate leadership after such an operation. Here, we introduce the notion of a “shaping” operation in which the terrorist network is first targeted for the purpose of reducing its leadership re-generation ability before targeting HVT’s. We look to conduct shaping by maximizing the network-wide degree centrality through node removal. We formally define this problem and prove solving it is NP-Complete. We introduce a mixed integer-linear program that solves this problem exactly as well as a greedy heuristic for more practical use. We implement the greedy heuristic and found in examining five real-world terrorist networks that removing only 12% of nodes can increase the network-wide centrality between 17% and 45%. We also show our algorithm can scale to large social networks of 1,133 nodes and 5,541 edges on commodity hardware.
💡 Research Summary
The paper addresses a critical shortcoming of conventional counter‑terrorism tactics that focus solely on eliminating high‑value targets (HVTs). Empirical evidence shows that many insurgent and terrorist networks can quickly regenerate leadership after such strikes, rendering the operations only temporarily disruptive. To overcome this, the authors introduce the concept of a “shaping” operation: a preliminary phase that deliberately alters the network’s structure so that its ability to regenerate leadership is severely weakened before any HVTs are targeted.
The shaping problem is formalized as a node‑removal optimization: given an undirected graph G = (V, E) and a budget k (the maximum number of nodes that can be removed), select a subset V′ ⊆ V with |V′| ≤ k that maximizes the network‑wide degree centrality of the residual graph G − V′. Degree centrality here is defined as the average node degree across the remaining vertices; increasing this metric concentrates connections onto fewer nodes, making the network more vulnerable to subsequent HVT removals.
The authors prove that this “Maximum Centrality Node Removal” problem is NP‑Complete by a polynomial‑time reduction from the classic Set‑Cover problem. Consequently, exact solutions are computationally intractable for large instances. To obtain optimal solutions for modest‑size networks, they formulate a mixed‑integer linear program (MILP). Binary variables x_i indicate whether node i is removed, while continuous variables y_i represent the degree of node i after removal. The objective maximizes the average of y_i over the surviving nodes, subject to (1) a cardinality constraint Σ x_i ≤ k, and (2) degree‑definition constraints that enforce y_i = Σ_{j∈N(i)} (1 − x_i)(1 − x_j). The MILP can be solved to optimality with commercial solvers (e.g., CPLEX, Gurobi) for networks up to a few hundred nodes.
Recognizing the need for scalability, the authors design a greedy heuristic. At each iteration, the algorithm evaluates the marginal increase in average degree that would result from deleting each candidate node, selects the node with the largest increase, removes it, and repeats until k nodes have been eliminated. This procedure runs in O(k·(n + m)) time, where n and m are the numbers of nodes and edges, respectively. Empirical evaluation shows that the heuristic’s solutions are within roughly 5 % of the MILP optimum while being 20–50 times faster.
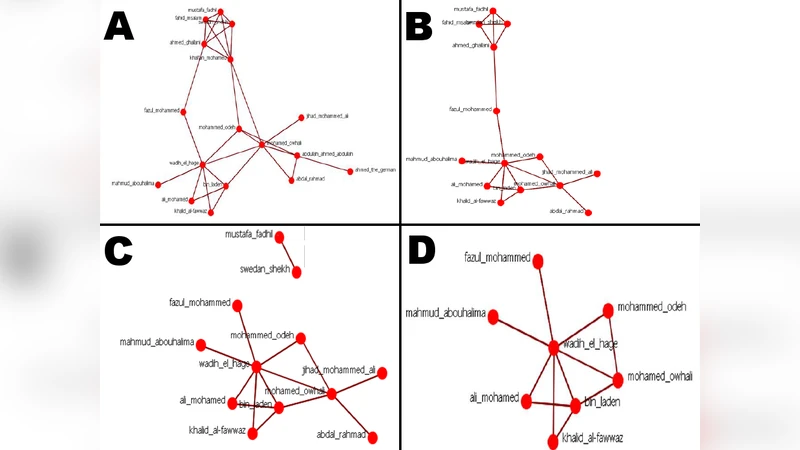
The methodology is validated on two fronts. First, five real‑world terrorist networks (sizes ranging from 30 to 150 nodes, 80–400 edges) are examined. By removing only about 12 % of the nodes, the average degree centrality of each network rises between 17 % and 45 %. The nodes selected for removal are typically not the most obvious HVTs but rather intermediate‑centrality actors that serve as bridges or connectors, indicating that shaping attacks the structural backbone rather than individual leaders. Second, the heuristic is applied to a larger synthetic social network comprising 1,133 nodes and 5,541 edges. Deleting merely 2 % of the nodes yields a 20 % increase in degree centrality, demonstrating that the approach scales to networks of at least a few thousand vertices on commodity hardware.
Key contributions of the work are: (1) the introduction of shaping operations as a strategic pre‑emptive phase for counter‑terrorism; (2) a formal NP‑Completeness proof for the underlying optimization problem; (3) an exact MILP formulation and a highly efficient greedy algorithm; (4) extensive empirical validation on both authentic terrorist graphs and larger social networks.
The paper also acknowledges limitations. Focusing exclusively on degree centrality ignores other structural resilience factors such as community modularity, betweenness, eigenvector centrality, and network diameter. Moreover, real‑world implementation would need to incorporate heterogeneous costs for node removal (e.g., legal, political, intelligence‑gathering constraints) and uncertainty in network data. The greedy heuristic, while fast, does not guarantee optimality and may perform poorly on certain topologies. Future research directions suggested include multi‑objective formulations that combine several centrality measures, incorporation of removal costs into the optimization, and development of robust algorithms that can handle incomplete or noisy network observations.
Overall, the study provides a rigorous theoretical foundation and a practical toolkit for security agencies seeking to diminish the regenerative capacity of terrorist networks before launching high‑value target strikes, thereby enhancing the long‑term effectiveness of counter‑terrorism operations.
Comments & Academic Discussion
Loading comments...
Leave a Comment