Public key Steganography Using Discrete Cross-Coupled Chaotic Maps
By cross-coupling two logistic maps a novel method is proposed for the public key steganography in JPEG image. Chaotic maps entail high complexity in the used algorithm for embedding secret data in a medium. In this paper, discrete cross- coupled chaotic maps are used to specifying the location of the different parts of the secret data in the image. Modifying JPEG format during compressing and decompressing, and also using public key enhanced difficulty of the algorithm. Simulation results show that in addition to excessive capacity, this method has high robustness and resistance against hackers and can be applicable in secret communication. Also the PSNR value is high compared to the other works.
💡 Research Summary
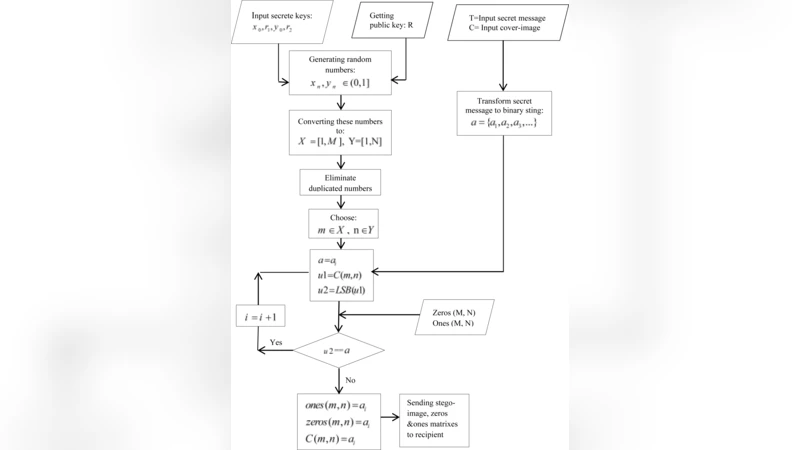
The paper introduces a novel public‑key steganography scheme for JPEG images that leverages discrete cross‑coupled chaotic maps to generate pseudo‑random embedding locations. Two logistic maps, each defined by the classic equation xₙ₊₁ = μ·xₙ·(1 − xₙ) with parameters μ₁ and μ₂ set in the fully chaotic regime (3.57 ≤ μ ≤ 4), are coupled through a publicly exchanged coefficient R. The coupling equations are xₙ₊₁ = f₁(xₙ) + R·f₂(yₙ) (mod 1) and yₙ₊₁ = f₂(yₙ) + R·f₁(xₙ) (mod 1). This cross‑coupling dramatically increases the entropy of the generated sequence compared with a single chaotic map, making the location pattern highly unpredictable even if an attacker knows one of the maps.
Key management is split into a secret key Kₛ (containing μ₁, μ₂, the initial seeds x₀, y₀, and the number of iterations) and a public key Kₚ (containing the coupling coefficient R and a standard RSA public key pair (e, n)). The sender encrypts Kₛ with the receiver’s RSA public key and transmits the ciphertext. The receiver decrypts it with the private key, reconstructs the exact chaotic sequence, and therefore knows precisely which DCT coefficients will be used for embedding.
Embedding proceeds directly on the JPEG compression pipeline. After the usual 8×8 DCT and quantization, all non‑zero AC coefficients (|coeff| ≥ 1) are collected into a candidate list C. The chaotic sequence is normalized to the range
Comments & Academic Discussion
Loading comments...
Leave a Comment