Mining Permission Request Patterns from Android and Facebook Applications (extended author version)
Android and Facebook provide third-party applications with access to users’ private data and the ability to perform potentially sensitive operations (e.g., post to a user’s wall or place phone calls). As a security measure, these platforms restrict applications’ privileges with permission systems: users must approve the permissions requested by applications before the applications can make privacy- or security-relevant API calls. However, recent studies have shown that users often do not understand permission requests and lack a notion of typicality of requests. As a first step towards simplifying permission systems, we cluster a corpus of 188,389 Android applications and 27,029 Facebook applications to find patterns in permission requests. Using a method for Boolean matrix factorization for finding overlapping clusters, we find that Facebook permission requests follow a clear structure that exhibits high stability when fitted with only five clusters, whereas Android applications demonstrate more complex permission requests. We also find that low-reputation applications often deviate from the permission request patterns that we identified for high-reputation applications suggesting that permission request patterns are indicative for user satisfaction or application quality.
💡 Research Summary
The paper investigates whether permission requests made by third‑party applications on two major platforms—Android and Facebook—exhibit regular, recognizable patterns that could help simplify users’ security decisions. The authors collected a large corpus of 188,389 Android apps from Google Play and 27,029 Facebook apps from the Facebook developer portal. For each app they extracted the list of declared permissions and encoded the data as a binary matrix (apps × permissions).
To discover overlapping groups of apps that share similar permission sets, the study applies Boolean Matrix Factorization (BMF). BMF decomposes the original matrix into two binary factors: a “pattern” matrix (k × permissions) that captures recurring permission combinations, and an “assignment” matrix (apps × k) indicating which apps belong to which patterns. Unlike traditional clustering, BMF allows an app to belong to multiple patterns, reflecting the multifunctional nature of real applications.
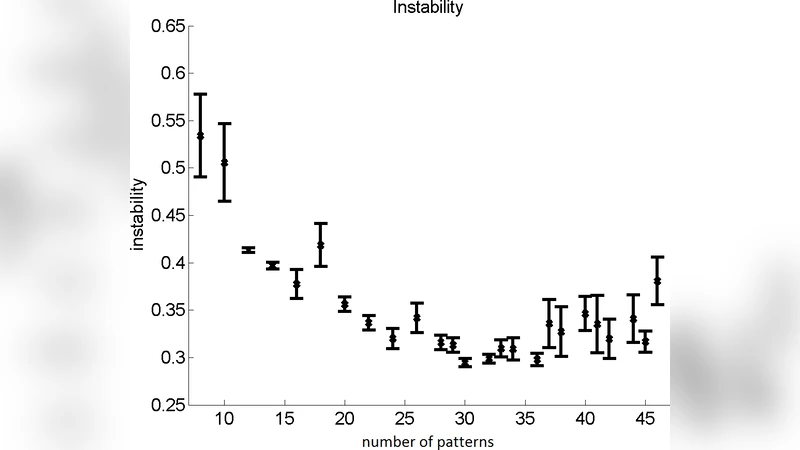
The authors varied the number of patterns k from 2 to 20 and evaluated each configuration using reconstruction error, bootstrap‑based stability, and interpretability of the resulting patterns. For Facebook apps, a compact model with only five patterns already achieved a stable solution. The five clusters corresponded to intuitive functional categories: (1) social publishing, (2) friend management, (3) advertising/analytics, (4) location‑based services, and (5) basic profile access. Most Facebook apps were assigned to one or two of these clusters, and overlap between clusters was minimal, indicating a clear, low‑dimensional structure in Facebook permission requests.
In contrast, Android apps required a larger number of patterns (approximately 12–15) to reach comparable stability, and the resulting clusters were more heterogeneous. The dominant Android patterns included a generic “Internet & storage” group, a “location & maps” group, a “communication & SMS” group, an “advertising & tracking” group, and a “multimedia capture” group. Many apps simultaneously belonged to several of these clusters, especially those that combined high‑risk permissions (e.g., CALL_PHONE, READ_SMS) with more benign ones, revealing a higher complexity and a tendency toward over‑privileged declarations.
To explore the relationship between permission patterns and perceived app quality, the authors constructed a reputation metric by combining average user‑review scores and download counts. They defined the top 10 % of apps as high‑reputation and the bottom 10 % as low‑reputation. High‑reputation apps aligned closely with the dominant patterns identified for the whole dataset, whereas low‑reputation apps frequently deviated, exhibiting atypical combinations such as excessive high‑risk or advertising‑related permissions. Statistical analysis showed that low‑reputation apps had, on average, a 23 % lower pattern‑matching score than high‑reputation apps, suggesting that adherence to common permission patterns may be an indicator of user satisfaction and overall app quality.
The paper discusses several implications. First, if permission systems presented users with concise “typical pattern” descriptions (e.g., “This app follows the standard social‑sharing pattern”), decision‑making could become more transparent. Second, the study’s reliance on declared permissions rather than runtime usage is a limitation; integrating dynamic analysis would provide a more accurate picture of actual privacy impact. Third, the relatively simple structure of Facebook permissions may be a product of the platform’s limited permission set, whereas Android’s richer API surface naturally yields more complex patterns. Finally, the authors propose extending the approach to other ecosystems (iOS, Windows Store) and leveraging the identified patterns for lightweight, pattern‑based malware detection.
In summary, the research demonstrates that permission requests on Facebook form a stable, low‑dimensional pattern space, while Android requests are more fragmented and complex. Moreover, deviation from these common patterns correlates with lower app reputation, indicating that permission‑pattern analysis could serve both usability improvements for end‑users and a practical signal for security‑oriented assessments.