A Class of Non Invertible Matrices in GF (2) for Practical One Way Hash Algorithm
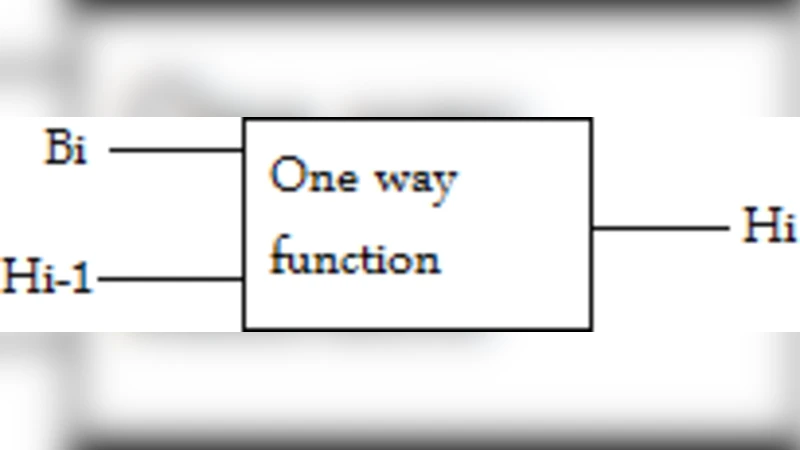
In this paper, we describe non invertible matrix in GF(2)which can be used as multiplication matrix in Hill Cipher technique for one way hash algorithm. The matrices proposed are permutation matrices with exactly one entry 1 in each row and each column and 0 elsewhere. Such matrices represent a permutation of m elements. Since the invention, Hill cipher algorithm was used for symmetric encryption, where the multiplication matrix is the key. The Hill cipher requires the inverse of the matrix to recover the plaintext from cipher text. We propose a class of matrices in GF(2) which are non invertible and easy to generate.
💡 Research Summary
The paper proposes a class of matrices over the binary field GF(2) to be used as the multiplication matrix in a Hill‑cipher‑based one‑way hash algorithm. The authors focus on permutation matrices that contain exactly one “1” in each row and each column, with all other entries equal to zero. Because such matrices represent a permutation of m elements, they can be generated trivially by selecting a random permutation and converting it into matrix form. The authors claim that these matrices are non‑invertible in GF(2) and therefore suitable for a hash function where the inverse operation (required for decryption in the traditional Hill cipher) must be impossible.
The proposed hashing procedure works as follows: the input message is divided into fixed‑size blocks, each block is interpreted as a column vector over GF(2), and the permutation matrix is multiplied by this vector. The resulting vector is then combined (typically by XOR) with the output of previous blocks to produce the final digest. Since the matrix is purportedly non‑invertible, the authors argue that recovering the original message from the digest is computationally infeasible, giving the construction a one‑way property.
While the idea of using a simple linear transformation for hashing is attractive from an implementation standpoint—multiplication over GF(2) reduces to a series of XOR and AND operations and can be performed with minimal hardware resources—the paper contains several critical oversights. First, permutation matrices are inherently invertible: their determinant over GF(2) is 1, and the transpose of a permutation matrix serves as its inverse. Consequently, the claim of non‑invertibility is mathematically inaccurate. Second, a purely linear mapping cannot provide the non‑linearity, diffusion, and collision resistance required of cryptographic hash functions. The transformation merely permutes bit positions without mixing their values, so the avalanche effect is weak and the probability of finding collisions is significantly higher than in established hash standards such as SHA‑2 or SHA‑3.
The security analysis in the paper is limited to a qualitative discussion; no empirical collision tests, avalanche measurements, or statistical assessments of output uniformity are presented. Moreover, because the permutation matrix is fixed (or drawn from a small set) for a given instance of the hash, an attacker could pre‑compute the effect of the permutation and mount pre‑image or chosen‑plaintext attacks with relative ease. The authors suggest that the simplicity of generation (O(m) time) offsets these concerns, but the trade‑off between ease of generation and cryptographic strength is not justified.
In the conclusion, the authors acknowledge that additional non‑linear rounds or mixing functions would be necessary for a practical hash, yet they do not provide a concrete design or performance evaluation for such extensions. As it stands, the proposed construction falls short of meeting the standard security criteria for cryptographic hash functions. Future work would need to (1) correctly address the invertibility issue, (2) incorporate proven non‑linear components (e.g., S‑boxes, modular addition), and (3) conduct thorough experimental validation—including collision resistance, pre‑image resistance, and statistical randomness tests—before the scheme could be considered a viable alternative to existing hash algorithms.
Comments & Academic Discussion
Loading comments...
Leave a Comment