Implementation of Privacy-preserving SimRank over Distributed Information Network
Information network analysis has drawn a lot attention in recent years. Among all the aspects of network analysis, similarity measure of nodes has been shown useful in many applications, such as clustering, link prediction and community identification, to name a few. As linkage data in a large network is inherently sparse, it is noted that collecting more data can improve the quality of similarity measure. This gives different parties a motivation to cooperate. In this paper, we address the problem of link-based similarity measure of nodes in an information network distributed over different parties. Concerning the data privacy, we propose a privacy-preserving SimRank protocol based on fully-homomorphic encryption to provide cryptographic protection for the links.
💡 Research Summary
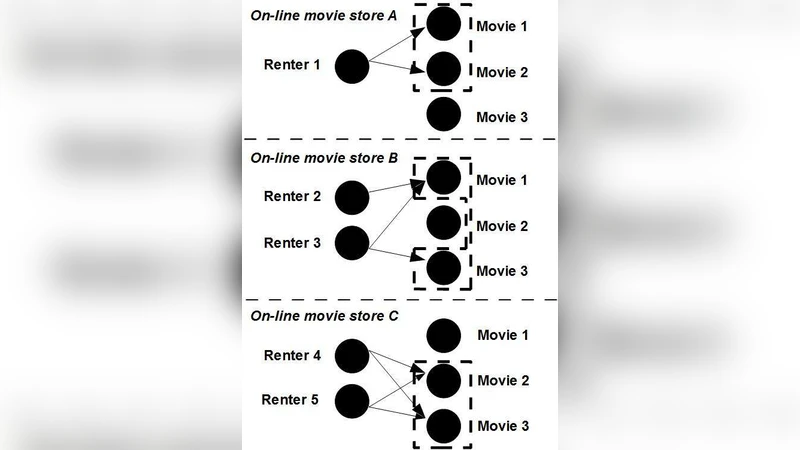
The paper tackles the problem of computing SimRank—a link‑based node similarity measure—over a graph whose edges are distributed among multiple, mutually distrustful parties. Traditional SimRank requires the entire adjacency matrix to be centrally available, which is infeasible when each participant must keep its link data confidential for legal, competitive, or privacy reasons. To reconcile the need for accurate similarity scores with stringent data‑privacy requirements, the authors propose a protocol that leverages Fully Homomorphic Encryption (FHE), specifically the CKKS scheme, to perform all necessary matrix operations on encrypted data.
The system model assumes m parties (P_1,…,P_m) each holding a sub‑graph (G_i=(V_i,E_i)). A trusted initializer generates an FHE key pair ((pk,sk)) and disseminates the public key (pk) to all parties; the secret key never leaves the initializer. Each party encodes its adjacency matrix (A_i) (row‑normalized) as a vector of real numbers, encrypts it with (pk), and sends the ciphertext (\mathsf{Enc}_{pk}(A_i)) to a coordinating server. The server aggregates the encrypted sub‑matrices into a global encrypted adjacency matrix (\mathsf{Enc}(A)). SimRank’s iterative formula
\
Comments & Academic Discussion
Loading comments...
Leave a Comment