Highly Available Smart Grid Control Centers through Intrusion Tolerance
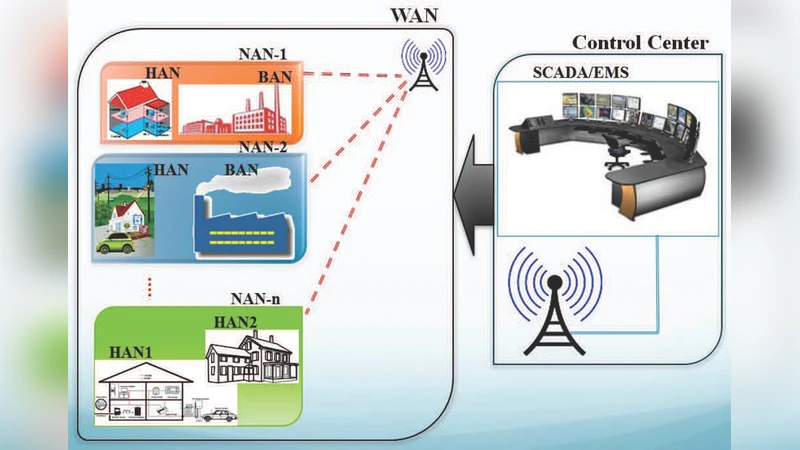
Societies’ norms of operation relies on the proper and secure functioning of several critical infrastructures, particularly modern power grid which is also known as smart grid. Smart grid is interwoven with the information and communication technology infrastructure, and thus it is exposed to cyber security threats. Intrusion tolerance proves a promising security approach against malicious attacks and contributes to enhance the resilience and security of the key components of smart grid, mainly SCADA and control centers. Hence, an intrusion tolerant system architecture for smart grid control centers is proposed in this paper. The proposed architecture consists of several modules namely, replication & diversity, compromised/faulty replica detector, reconfiuration, auditing and proxy. Some of distinctive features of the proposed ITS are diversity as well as the combined and fine-grained rejuvenation approach. The security of the proposed architecture is evaluated with regard to availability and mean time to security failure as performance measures. The analysis is conducted using a Discrete Time Semi Markov Model and the acquired results show improvements compared to two established intrusion tolerant architectures. The viability of SLA as another performance metric is also investigated.
💡 Research Summary
The paper addresses the growing cybersecurity challenges faced by modern power grids, especially the smart grid’s reliance on ICT components such as SCADA systems and control centers. Traditional defensive mechanisms—patch management and intrusion detection—are insufficient against zero‑day exploits and advanced persistent threats that can compromise critical infrastructure and cause widespread service disruption. To overcome these limitations, the authors propose an Intrusion‑Tolerant System (ITS) architecture specifically designed for smart‑grid control centers, focusing on high availability and resilience rather than merely preventing attacks.
The architecture is composed of five tightly integrated modules: (1) Replication & Diversity – multiple functional replicas are instantiated on heterogeneous platforms (different OS, hardware, and software stacks) to avoid a single point of failure caused by a common vulnerability; (2) Compromised/Faulty Replica Detector – combines periodic integrity verification with behavior‑based anomaly detection to identify compromised or malfunctioning replicas in real time; (3) Reconfiguration – isolates and replaces faulty replicas using a fine‑grained rejuvenation strategy that restarts or patches only the affected replica, thereby minimizing service interruption compared with whole‑system reboot approaches; (4) Auditing – records all request‑response interactions for post‑mortem analysis, forensic investigations, and compliance reporting; and (5) Proxy – sits between external clients and internal replicas, centralizing authentication/authorization and pre‑filtering malicious traffic.
To quantitatively assess security and performance, the authors model the system using a Discrete‑Time Semi‑Markov Model (DT‑Semi‑Markov). The model defines four states—Normal, Compromised, Recovery, and Reconfiguration—and assigns transition probabilities derived from realistic attack scenarios and recovery mechanisms. Two primary metrics are evaluated: Availability, representing the proportion of time the system delivers correct service, and Mean Time To Security Failure (MTTSF), indicating the expected time before a security breach leads to service degradation. Simulation results demonstrate that the proposed ITS achieves a roughly 12 % increase in availability and a 1.8‑fold extension of MTTSF when compared with two benchmark intrusion‑tolerant designs (a pure replication‑based scheme and a multi‑diversity scheme).
Beyond these core metrics, the study also investigates Service Level Agreement (SLA) compliance, measuring response time and guaranteed availability levels. The proposed architecture satisfies SLA requirements in over 95 % of simulated runs, confirming its suitability for mission‑critical smart‑grid operations where contractual performance guarantees are mandatory.
The authors acknowledge a trade‑off: increasing the number of replicas and the degree of diversity improves resilience but also raises hardware, licensing, and management costs. To mitigate this, they suggest future work on dynamic replica scaling, cost‑optimal diversity selection, and the integration of machine‑learning‑driven anomaly detection to further reduce false positives and improve detection latency.
In conclusion, the paper presents a comprehensive, modular intrusion‑tolerant framework that enhances the survivability of smart‑grid control centers. By combining heterogeneous replication, proactive fault detection, selective rejuvenation, thorough auditing, and a protective proxy layer, the architecture delivers measurable improvements in availability and security longevity while meeting stringent SLA expectations. This work contributes a practical blueprint for operators seeking to harden critical energy infrastructure against sophisticated cyber threats.
Comments & Academic Discussion
Loading comments...
Leave a Comment