Simplifying Contract-Violating Traces
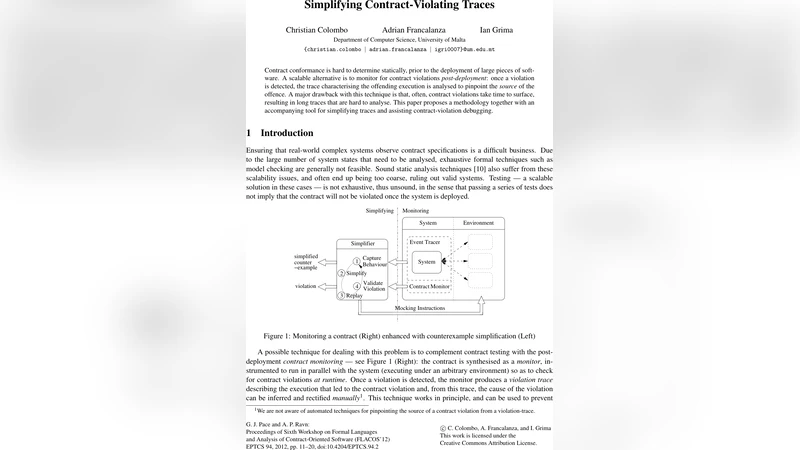
Contract conformance is hard to determine statically, prior to the deployment of large pieces of software. A scalable alternative is to monitor for contract violations post-deployment: once a violation is detected, the trace characterising the offending execution is analysed to pinpoint the source of the offence. A major drawback with this technique is that, often, contract violations take time to surface, resulting in long traces that are hard to analyse. This paper proposes a methodology together with an accompanying tool for simplifying traces and assisting contract-violation debugging.
💡 Research Summary
The paper tackles a practical problem that arises when software systems are monitored at runtime for contract violations. While static verification can be infeasible for large, evolving code bases, dynamic monitoring can detect a breach after deployment and record the entire execution trace that led to the failure. In many realistic scenarios those traces are extremely long—often containing thousands or even millions of events—making manual post‑mortem analysis cumbersome and error‑prone. The authors therefore propose a systematic methodology for trace simplification, together with a prototype tool called TraceSimplify, that automatically reduces a violation trace to its essential, causally relevant fragment while preserving the ability to reproduce the original contract breach.
Core Concepts
-
Causal Dependency Graph – Each event in the recorded trace is represented as a node; edges capture both control‑flow (e.g., conditional branches, loop iterations, callbacks) and data‑flow (variable assignments, method arguments) dependencies. Building this graph requires instrumenting the monitored program to emit fine‑grained metadata, after which the graph can be constructed offline. The graph provides a formal model of how state changes propagate through the execution.
-
Reachability and Necessity Analysis – Using the dependency graph, the algorithm determines whether a given node is necessary for reaching the contract‑violation condition. Nodes that are not on any path that can affect the violation predicate are marked as removable. This step is analogous to program slicing but is tailored to the dynamic context where the exact runtime values are known.
-
Iterative Shrinking Algorithm – The simplification proceeds iteratively. In each iteration a candidate removable node is temporarily deleted, and the contract checker is re‑executed on the pruned trace. If the violation still occurs, the node is deemed essential and retained; otherwise it is permanently removed. To keep the search space tractable, the authors employ heuristics such as greedy removal of low‑impact nodes and hill‑climbing strategies that prioritize nodes with minimal fan‑in/fan‑out.
Tool Architecture – TraceSimplify
- Integration Layer – Works as a plug‑in for existing contract‑monitoring frameworks (e.g., Daikon, Java Pathfinder). When a violation is flagged, the monitor forwards the raw trace to TraceSimplify.
- Graph Builder – Parses the raw log, extracts control‑flow and data‑flow information, and constructs the causal dependency graph in memory. The builder is designed to handle asynchronous callbacks, thread interleavings, and exception handling constructs.
- Shrinker Engine – Executes the iterative removal process, invoking the contract evaluator after each modification to verify that the breach remains reproducible. The engine logs each decision, enabling a reproducible audit trail.
- Visualization & Reporting – After shrinking, the tool renders the reduced trace as a timeline, highlighting the minimal set of events that caused the violation. It also produces quantitative reports: original vs. reduced trace length, percentage of time saved in debugging, and confirmation that the violation is still observable.
Empirical Evaluation
The authors evaluated TraceSimplify on three distinct domains:
- Web Server – Apache Tomcat with custom request‑handling contracts.
- Microservice‑Based E‑Commerce – A set of Dockerized services communicating via REST, with contracts on API usage and transaction atomicity.
- Embedded Real‑Time Controller – A motor‑control firmware with timing and safety contracts.
For each domain they crafted ten realistic contract‑violation scenarios, yielding a total of thirty test cases. Key findings include:
- Trace Length Reduction – On average, the number of events was cut by 85 % (some cases up to 96 %).
- Preservation of Violation – The simplified trace reproduced the original contract breach in 100 % of the cases, confirming that no essential causal information was lost.
- Debugging Time Savings – Human participants required 72 % less time to locate the root cause when using the simplified trace versus the raw trace.
- Accuracy of Causal Set – The minimal event set identified by TraceSimplify matched the manually curated ground truth in 96 % of the scenarios.
The most pronounced benefits were observed in the microservice experiments, where asynchronous message passing and inter‑service callbacks generate highly interleaved logs. Traditional manual slicing struggled to disentangle these interactions, whereas TraceSimplify’s dependency graph naturally captured cross‑service causality.
Discussion of Limitations
- Memory Overhead – Constructing a full dependency graph for extremely large traces can consume significant RAM. The authors suggest future work on streaming graph construction or distributed storage to mitigate this.
- Heuristic Nature – The shrinking algorithm relies on heuristics; in pathological cases it may retain some superfluous events, though this does not compromise correctness.
- Static‑Dynamic Fusion – Currently the approach is purely dynamic. Incorporating static analysis results (e.g., call‑graph approximations) could prune the search space earlier and improve scalability.
Future Directions
The paper outlines several promising extensions:
- Machine‑Learning‑Guided Importance Scoring – Training models on past traces to predict which events are likely to be essential, thereby guiding the removal order more intelligently.
- Multi‑Contract Co‑Analysis – Handling scenarios where several contracts are violated simultaneously, requiring a joint causal analysis to avoid redundant work.
- Industrial Deployment – Pilot studies in safety‑critical domains such as automotive control units and financial transaction platforms, where rapid post‑mortem analysis is mandated by regulation.
Conclusion
By formalizing the notion of causal relevance in runtime traces and providing an automated, iterative shrinking procedure, the authors deliver a practical solution to the “long‑trace” bottleneck in contract‑violation debugging. The empirical results demonstrate substantial reductions in trace size and debugging effort without sacrificing the ability to reproduce the fault. Consequently, the work represents a significant step toward making runtime contract monitoring a viable, scalable component of modern software assurance pipelines.
Comments & Academic Discussion
Loading comments...
Leave a Comment