Reply to recent scepticism about the foundations of quantum cryptography
In a series of recent papers, Hirota and Yuen claim to have identified a fundamental flaw in the theory underlying quantum cryptography, which would invalidate existing security proofs. In this short note, we sketch their argument and show that their conclusion is unjustified — it originates from a confusion between necessary and sufficient criteria for secrecy.
💡 Research Summary
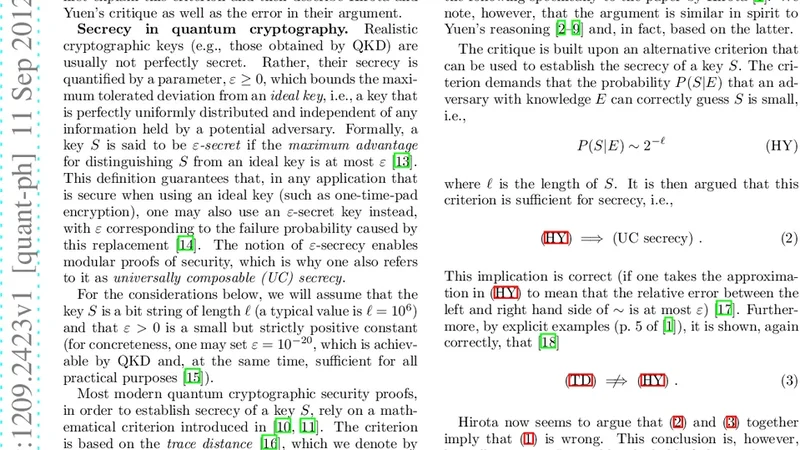
The paper addresses recent claims by Hirota and Yuen that a fundamental flaw exists in the theoretical foundations of quantum cryptography, specifically in the security proofs of quantum key distribution (QKD). The authors begin by outlining the standard security framework used in QKD, which defines secrecy in terms of the trace‑distance parameter ϵ and embeds this definition within a composable security model. In this model, an ϵ‑secure protocol guarantees that the joint state of the key and an adversary’s system deviates from an ideal, perfectly secret state by at most ϵ, and this bound composes linearly across protocol stages.
Hirota and Yuen’s argument is reconstructed in two steps. First, they assert that the ϵ‑definition is a necessary condition rather than a sufficient one, implying that any non‑zero ϵ could, in principle, allow a complete breach of secrecy. Second, they present a specific quantum state that they claim could arise in a realistic QKD implementation, arguing that the resulting information leakage would be unacceptable unless ϵ were set to an unrealistically small value.
The authors demonstrate that this line of reasoning conflates necessary and sufficient criteria. In the established literature, ϵ‑security is explicitly a sufficient condition: if the trace distance is bounded by ϵ, then the adversary’s advantage in distinguishing the real key from a uniformly random key is at most ϵ/2. This does not imply that any non‑zero ϵ automatically leads to a total loss of secrecy; rather, it quantifies the maximum possible leakage. The paper emphasizes that the composable security framework relies on this sufficiency, allowing protocol designers to choose ϵ values that are exponentially small (e.g., 10⁻¹⁰⁰) so that the probability of any practical attack succeeding is negligible.
A detailed technical analysis follows, revisiting the relationship between trace distance, distinguishability, and operational security metrics. The authors show that the state constructed by Hirota and Yuen, while mathematically permissible, would occur with a probability that is exponentially suppressed under realistic parameter choices. Consequently, the alleged “counterexample” does not invalidate the existing security proofs; it merely highlights a scenario that would be excluded by the standard selection of security parameters.
The paper also clarifies how the composable security definition ensures that security guarantees are preserved when QKD is used as a sub‑routine in larger cryptographic tasks. By bounding the total failure probability of a composed system as the sum (or maximum) of the individual ϵ‑values, the framework guarantees that the overall security remains within the desired threshold.
In conclusion, the authors argue that Hirota and Yuen’s criticism stems from a misinterpretation of the role of the ϵ‑parameter. The established security proofs remain sound because they are built on a sufficient‑condition definition of secrecy, coupled with a disciplined choice of ϵ that renders any residual leakage practically irrelevant. Therefore, the foundations of quantum cryptography, as currently understood, are not undermined by the claims in the cited papers.
Comments & Academic Discussion
Loading comments...
Leave a Comment