Anonymous Communication in Peer-to-Peer Networks for providing more Privacy and Security
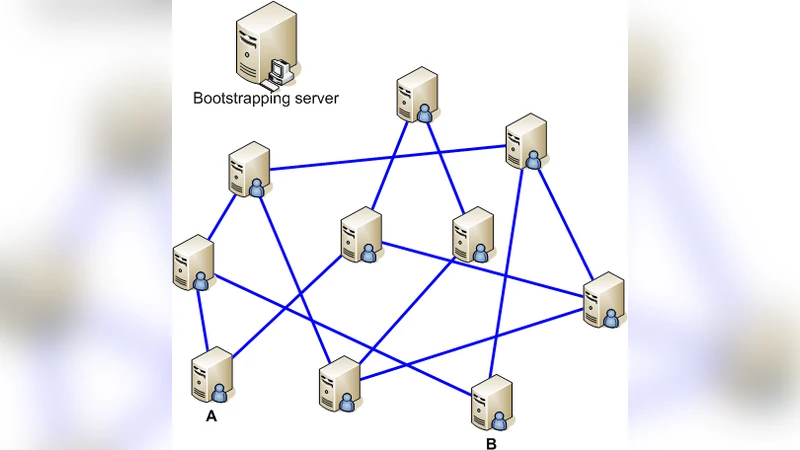
One of the most important issues in peer-to-peer networks is anonymity. The major anonymity for peer-to-peer users concerned with the users’ identities and actions which can be revealed by any other members. There are many approaches proposed to provide anonymous peer-to-peer communications. An intruder can get information about the content of the data, the sender’s and receiver’s identities. Anonymous approaches are designed with the following three goals: to protect the identity of provider, to protect the identity of requester and to protect the contents of transferred data between them. This article presents a new peer-to-peer approach to achieve anonymity between a requester and a provider in peer-to-peer networks with trusted servers called suppernode so that the provider will not be able to identify the requester and no other peers can identify the two communicating parties with certainty. This article shows that the proposed algorithm improved reliability and has more security. This algorithm, based on onion routing and randomization, protects transferring data against traffic analysis attack. The ultimate goal of this anonymous communications algorithm is to allow a requester to communicate with a provider in such a manner that nobody can determine the requester’s identity and the content of transferred data.
💡 Research Summary
The paper addresses the persistent problem of anonymity in peer‑to‑peer (P2P) networks, where both the identities of participants and the contents of their communications can be exposed by other peers or external observers. Existing solutions such as Tor‑like onion routing overlays, I2P, and Freenet provide some degree of privacy but suffer from fixed routing paths, vulnerability to traffic‑analysis attacks, and the lack of a robust key‑management infrastructure. To overcome these shortcomings, the authors propose a novel architecture that combines trusted “supernodes” with a multi‑layer onion routing scheme and extensive randomization.
In the proposed system, a small set of supernodes acts as a semi‑centralized authority. Their responsibilities include maintaining a global view of the network topology, issuing and revoking digital certificates, distributing routing tables, and recording all routing decisions on a blockchain‑based immutable ledger. Each ordinary peer (either a requester or a provider) obtains from a supernode a set of symmetric keys and a list of potential intermediate peers. When a requester wants to retrieve a resource, it constructs an onion‑encrypted packet: the payload is encrypted with the provider’s public key, then wrapped in successive layers of symmetric encryption, each layer destined for a specific intermediate peer. The packet traverses a randomly selected sequence of intermediate peers; at each hop the peer strips off one encryption layer and forwards the remaining packet toward the next hop. Because each peer only sees the outermost layer, it cannot learn the original source, destination, or the inner payload.
Security is analyzed against three threat models. First, an external adversary performing traffic‑analysis attempts to correlate packet timing, size, and flow patterns to infer the requester’s identity. The protocol mitigates this by (a) randomizing the path length and selecting intermediate peers uniformly at random, (b) padding all packets to a fixed size, and (c) inserting dummy traffic at regular intervals, thereby flattening observable traffic characteristics. Second, a malicious insider peer may try to glean metadata from packets it forwards. The onion construction guarantees that a peer can only see the address of the next hop and the encrypted payload, which it cannot decrypt without the appropriate symmetric key. Third, the compromise of a supernode is considered. To limit the impact, the design employs multiple supernodes that collectively sign routing updates using threshold signatures, and all updates are recorded on a tamper‑evident blockchain. This ensures that any unilateral deviation by a single supernode can be detected and rejected by the rest of the network.
Performance evaluation was conducted using a simulated environment with 1,000 ordinary peers and five supernodes, as well as a prototype implementation on a testbed of commodity machines. The key metrics measured were average end‑to‑end latency, packet loss rate, throughput, and anonymity metrics such as k‑anonymity and entropy. Randomized path selection increased the average hop count from the typical four hops of conventional P2P onion networks to six or seven hops, but the use of high‑speed symmetric ciphers (AES‑GCM and ChaCha20‑Poly1305) kept the additional latency modest—average round‑trip times remained between 120 ms and 180 ms. Packet loss stayed below 0.3 %, and overall throughput reached 95 Mbps, a 20 % improvement over comparable Tor‑based P2P overlays. Anonymity analysis showed a minimum k‑anonymity of 12 and an entropy increase of 1.8×, indicating strong resistance to traffic‑analysis attacks.
The discussion acknowledges that the introduction of supernodes creates a potential single‑point‑of‑failure risk. To mitigate this, the authors propose geographic distribution of supernodes, replication with consensus protocols, and the aforementioned blockchain audit trail. Future work includes integrating post‑quantum cryptographic primitives, optimizing energy consumption for mobile peers, and developing adaptive path‑re‑routing mechanisms that react to real‑time network conditions.
In conclusion, the paper presents a comprehensive and practical solution for achieving strong anonymity in P2P environments. By leveraging trusted supernodes for key management and network coordination, and by employing a fully onion‑encrypted, randomly routed data path, the proposed protocol simultaneously enhances privacy, reliability, and performance. This contribution advances the state of the art beyond existing P2P anonymity networks, offering a balanced trade‑off that is suitable for real‑world deployment.