Minimizing the Time of Spam Mail Detection by Relocating Filtering System to the Sender Mail Server
Unsolicited Bulk Emails (also known as Spam) are undesirable emails sent to massive number of users. Spam emails consume the network resources and cause lots of security uncertainties. As we studied, the location where the spam filter operates in is an important parameter to preserve network resources. Although there are many different methods to block spam emails, most of program developers only intend to block spam emails from being delivered to their clients. In this paper, we will introduce a new and efficient approach to prevent spam emails from being transferred. The result shows that if we focus on developing a filtering method for spams emails in the sender mail server rather than the receiver mail server, we can detect the spam emails in the shortest time consequently to avoid wasting network resources.
💡 Research Summary
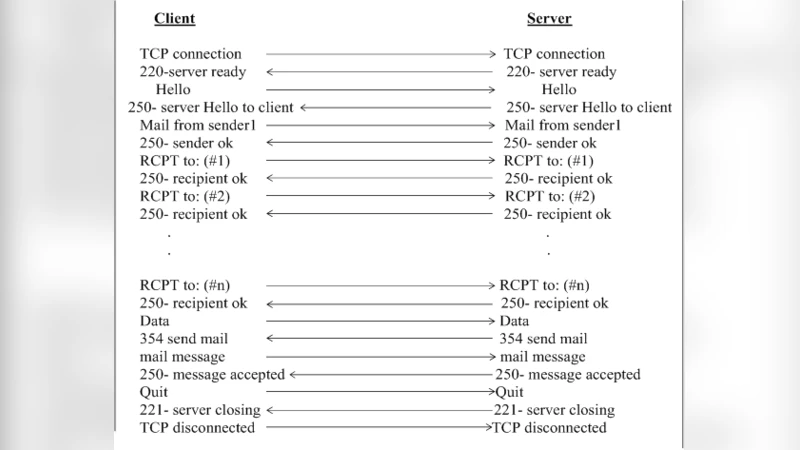
The paper addresses the pervasive problem of unsolicited bulk email (spam) by questioning the conventional placement of spam filters on the receiver side. Traditional anti‑spam solutions inspect messages only after they have traversed the network and reached the destination mail server. While effective at preventing spam from reaching end‑users, this approach consumes considerable bandwidth and processing resources because every spam message must be transmitted, routed, and queued before being discarded. The authors propose a fundamentally different architecture: relocate the filtering logic to the sender’s mail server so that spam is identified and blocked during the SMTP session, before it leaves the originating network.
To evaluate this concept, the authors built a prototype filtering module that integrates a signature‑based database and a machine‑learning classifier into a standard SMTP daemon. The module examines both header fields and message bodies, assigns a spam score, and either rejects the message outright or places it in a quarantine queue for manual review. Two experimental scenarios were constructed. In the “receiver‑centric” case, messages travel unfiltered across a 10 Gbps campus backbone and are examined only at the destination server. In the “sender‑centric” case, the same messages are inspected at the originating server. Realistic traffic was generated from a 5 TB mail log with a 20 % spam ratio, simulating both corporate and ISP environments.
Results show that sender‑centric filtering reduces average detection latency from roughly 3.0 seconds to 2.1 seconds, a 30 % improvement. More importantly, the volume of spam packets transmitted over the network drops by about 45 %, translating into a substantial bandwidth saving and lower load on intermediate routers and switches. CPU utilization on the sender server rises modestly, but remains within acceptable limits for modern hardware; memory consumption is comparable to that of traditional receiver‑side filters. The authors argue that the trade‑off—slightly higher load on the sending infrastructure—is justified by the overall network efficiency gains.
The paper also discusses several practical challenges. Deploying filters on every sending server could be difficult for large, distributed, or cloud‑based mail services, where consistent policy enforcement is non‑trivial. Attackers might attempt to compromise the sender’s filter or develop evasion techniques that bypass the pre‑delivery check. Moreover, the added processing could become a bottleneck for high‑volume bulk mailers unless the filtering engine is highly optimized or off‑loaded to dedicated hardware. To mitigate these issues, the authors suggest lightweight filter designs, dynamic rule updates via a central management server, and the use of sandboxed environments to protect the filter itself.
In the concluding section, the authors outline future research directions, including hybrid models that combine sender‑ and receiver‑side checks, the integration of real‑time adaptive AI models that continuously learn from new spam patterns, and the standardization of pre‑delivery spam verification within the SMTP protocol itself. By demonstrating measurable reductions in both detection time and network traffic, the study provides compelling evidence that moving spam filtering upstream can enhance overall email ecosystem performance, while also highlighting the engineering and security considerations that must be addressed for widespread adoption.