Formal Verification of Safety Properties for Ownership Authentication Transfer Protocol
In ubiquitous computing devices, users tend to store some valuable information in their device. Even though the device can be borrowed by the other user temporarily, it is not safe for any user to borrow or lend the device as it may cause private data of the user to be public. To safeguard the user data and also to preserve user privacy we propose and model the technique of ownership authentication transfer. The user who is willing to sell the device has to transfer the ownership of the device under sale. Once the device is sold and the ownership has been transferred, the old owner will not be able to use that device at any cost. Either of the users will not be able to use the device if the process of ownership has not been carried out properly. This also takes care of the scenario when the device has been stolen or lost, avoiding the impersonation attack. The aim of this paper is to model basic process of proposed ownership authentication transfer protocol and check its safety properties by representing it using CSP and model checking approach. For model checking we have used a symbolic model checker tool called NuSMV. The safety properties of ownership transfer protocol has been modeled in terms of CTL specification and it is observed that the system satisfies all the protocol constraint and is safe to be deployed.
💡 Research Summary
The paper addresses a pressing security concern in ubiquitous computing environments: the risk of private data exposure when a personal device is temporarily lent or permanently sold to another user. Conventional safeguards—such as data encryption and access‑control mechanisms—do not fully mitigate the problem because they assume that the device’s ownership remains unchanged. If ownership is not formally transferred, the former owner may still retain the ability to interact with the device, opening the door to impersonation, data leakage, or malicious misuse, especially in cases of loss or theft.
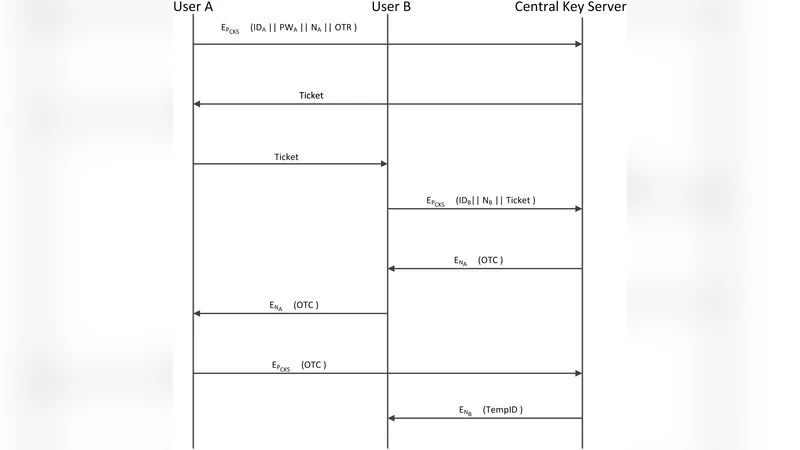
To solve this, the authors propose an Ownership Authentication Transfer (OAT) protocol that explicitly binds device usage rights to a verified owner. The protocol involves three principal entities: the current owner (seller), the prospective owner (buyer), and a trusted central authentication server. The interaction proceeds in three phases. First, the seller authenticates to the server by presenting a digitally signed proof of current ownership together with the device’s identifier; the server validates this proof and issues a one‑time transfer token. Second, the buyer registers with the server, proves his/her identity, and submits the seller‑provided token as part of a transfer request. The server cross‑checks the seller’s token, the buyer’s credentials, and any policy constraints (e.g., payment confirmation). Upon successful verification, the server generates a fresh device certificate and cryptographic keys for the buyer, simultaneously revoking the seller’s credentials and updating the device’s internal key store. Consequently, the former owner is cryptographically barred from accessing the device, while the new owner gains exclusive, authenticated control.
The technical contribution of the paper lies in the rigorous formal modeling and verification of this protocol. The authors encode the protocol’s concurrent processes using Communicating Sequential Processes (CSP), representing each participant as an independent process that communicates over well‑defined channels. This CSP model captures ordering constraints, possible interleavings, and potential deadlock conditions. They then translate the CSP specification into the input language of NuSMV, a symbolic model checker, and express the desired safety properties in Computation Tree Logic (CTL). The key CTL specifications include: (1) “Globally, if ownership has not been transferred, the old owner cannot use the device” (AG ¬(oldOwnerCanUse ∧ ¬ownershipTransferred)); (2) “If ownership is transferred, eventually the new owner will be able to use the device” (AG (ownershipTransferred → AF newOwnerCanUse)); and (3) “A stolen or lost device cannot be used without successful ownership transfer” (AG ¬stolenDeviceCanBeUsed). Model checking confirms that all these properties hold, indicating that the protocol is free from deadlocks, authentication bypasses, and replay attacks.
The authors also present scenario‑based evaluations. In a theft simulation, an adversary possessing the stolen device attempts to authenticate using the former owner’s credentials. Because the server has not received a valid transfer request, it rejects the attempt, thereby preventing unauthorized use. Conversely, a legitimate buyer who follows the OAT steps obtains a fresh certificate and can operate the device without hindrance. These experiments demonstrate that the protocol not only enforces ownership semantics but also preserves user privacy and data integrity under adverse conditions.
Finally, the paper discusses future extensions. The authors suggest integrating a blockchain‑based decentralized authentication ledger to eliminate a single point of failure, supporting simultaneous multi‑device ownership transfers, and optimizing cryptographic operations for resource‑constrained devices. By combining a clear protocol design with formal verification via CSP and NuSMV, the work provides a compelling blueprint for secure, trustworthy ownership handover in modern mobile and IoT ecosystems, ensuring that devices can be safely sold, lent, or reclaimed without compromising the confidentiality of the data they contain.
Comments & Academic Discussion
Loading comments...
Leave a Comment