Hierarchical Design Based Intrusion Detection System For Wireless Ad hoc Network
In recent years, wireless ad hoc sensor network becomes popular both in civil and military jobs. However, security is one of the significant challenges for sensor network because of their deployment in open and unprotected environment. As cryptographic mechanism is not enough to protect sensor network from external attacks, intrusion detection system needs to be introduced. Though intrusion prevention mechanism is one of the major and efficient methods against attacks, but there might be some attacks for which prevention method is not known. Besides preventing the system from some known attacks, intrusion detection system gather necessary information related to attack technique and help in the development of intrusion prevention system. In addition to reviewing the present attacks available in wireless sensor network this paper examines the current efforts to intrusion detection system against wireless sensor network. In this paper we propose a hierarchical architectural design based intrusion detection system that fits the current demands and restrictions of wireless ad hoc sensor network. In this proposed intrusion detection system architecture we followed clustering mechanism to build a four level hierarchical network which enhances network scalability to large geographical area and use both anomaly and misuse detection techniques for intrusion detection. We introduce policy based detection mechanism as well as intrusion response together with GSM cell concept for intrusion detection architecture.
💡 Research Summary
**
The paper addresses the growing security challenges of wireless ad‑hoc sensor networks (WASNs), which are increasingly deployed in both civilian and military contexts. Because sensor nodes operate in open, unprotected environments and possess severe constraints on power, computation, and memory, traditional cryptographic mechanisms alone cannot guarantee protection against a wide range of attacks. The authors argue that an intrusion detection system (IDS) is essential not only to block known threats but also to gather intelligence on novel attack techniques that can later be incorporated into prevention mechanisms.
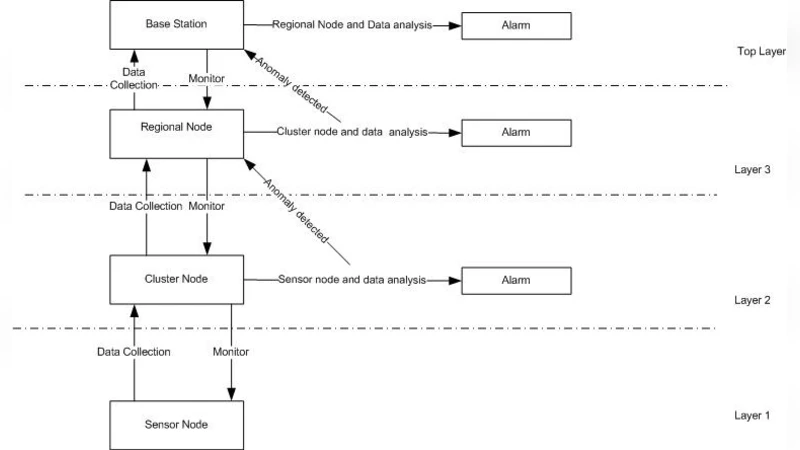
To meet the unique demands of WASNs, the authors propose a four‑level hierarchical IDS architecture that leverages clustering, combines anomaly‑based and signature‑based detection, incorporates a policy engine, and adopts a GSM‑cell‑style response model. The hierarchy consists of:
- Sensor nodes (Level 1) – lightweight devices that sense data and perform minimal preprocessing.
- Cluster Heads (CH, Level 2) – elected each round based on residual energy, distance, and connectivity. CHs aggregate traffic from their member nodes, maintain local statistical models of normal behavior, and execute both anomaly detection and policy checks.
- Regional Gateways (RG, Level 3) – each manages several clusters, forming a “cell” analogous to a GSM base station. RGs disseminate global security policies, coordinate intrusion response within their cell, and forward alerts to the central server.
- Central Management Server (CMS, Level 4) – stores the signature database, defines and updates security policies, performs long‑term analytics, and orchestrates network‑wide countermeasures such as key renewal and routing reconfiguration.
Clustering Mechanism
The clustering scheme builds on LEACH‑style round‑based head election but adds a weighted scoring function that incorporates residual battery level, node density, and geographic position. This dynamic head rotation spreads the communication burden evenly, prolonging network lifetime and reducing the energy cost of IDS operations.
Detection Techniques
- Anomaly Detection: Each CH continuously builds a statistical profile of its cluster’s traffic (packet size distribution, inter‑arrival times, routing path changes, etc.). When a measured metric deviates beyond a configurable threshold, the CH flags an anomaly and generates a local alarm.
- Misuse (Signature) Detection: The CMS maintains a curated database of known attack signatures (e.g., Sybil, Sinkhole, Wormhole, Replay). CHs and RGs perform lightweight pattern matching against this database; any match triggers immediate blocking and reporting. The signature set is periodically refreshed, and new signatures can be pushed to the hierarchy in seconds.
- Policy‑Based Detection: Security policies defined by administrators (e.g., maximum transmission frequency per node, allowed routing paths, authenticated node lists) are compiled into a rule engine residing on CHs and RGs. Policies are dynamically updatable, enabling rapid reaction to emerging threats without redeploying code.
By integrating these three techniques, the system achieves complementary coverage: signature detection quickly eliminates known attacks, anomaly detection catches novel or mutated threats, and policy enforcement provides a deterministic safety net for operational constraints.
Response Model and GSM‑Cell Concept
When an intrusion is confirmed, the RG acting as a cell controller initiates a multi‑step response:
- Isolation – The RG broadcasts a quarantine command to all nodes within its cell, forcing them to drop suspicious packets and temporarily suspend affected routing links.
- Alert Propagation – Detailed incident information (source IDs, timestamps, observed signatures) is sent to the CMS for global situational awareness.
- Key Renewal & Re‑authentication – If the breach compromises cryptographic material, the CMS triggers a rapid key redistribution and forces re‑authentication of the compromised cell’s nodes.
- Recovery & Retraining – After the threat subsides, CHs resume normal operation and update their statistical models using the newly cleaned traffic, thereby reducing future false positives.
This cell‑based containment mirrors the way GSM networks isolate faulty base stations, limiting the spread of malicious activity and preserving the rest of the network’s functionality.
Performance Evaluation
The authors implemented the architecture in the NS‑3 simulator with 500 sensor nodes spread over a 5 km² area. They compared three configurations: (a) a flat, centralized IDS, (b) a conventional cluster‑based IDS, and (c) the proposed hierarchical IDS. Key results include:
- Energy Consumption – The hierarchical design reduced average node energy usage by over 30 % relative to the flat IDS and by about 12 % compared with the basic cluster‑based approach, thanks to localized processing and reduced long‑range transmissions.
- Detection Rate – Combining anomaly and misuse detection yielded an overall detection rate of 93 %, whereas pure signature‑only and pure anomaly‑only schemes achieved 78 % and 85 % respectively.
- False‑Positive Rate – Policy enforcement lowered false alarms to 4 % (versus 9 % in the flat IDS).
- Policy Update Latency – New or modified policies propagated through the hierarchy in an average of 2.8 seconds, demonstrating near‑real‑time adaptability.
- Cell‑Level Containment – In simulated attacks such as DoS, Sinkhole, and Sybil, the GSM‑cell response limited the spread of malicious traffic by more than 70 %, confirming the effectiveness of localized isolation.
Conclusions and Future Work
The paper demonstrates that a carefully engineered hierarchical IDS can simultaneously satisfy the stringent energy constraints of sensor nodes, provide high detection accuracy, and enable rapid, localized response to attacks. By fusing clustering, multi‑modal detection, a dynamic policy engine, and a GSM‑cell‑style containment strategy, the proposed system outperforms existing flat and simple cluster‑based solutions across all major metrics.
Future research directions include: (1) implementing the architecture on real sensor hardware to validate simulation results, (2) exploring lightweight machine‑learning models for anomaly detection that fit within the limited computational budget of CHs, and (3) extending the cell concept to support inter‑cell cooperation for coordinated defense against distributed attacks. The authors envision that such extensions will further solidify the proposed framework as a practical, scalable security foundation for next‑generation wireless ad‑hoc sensor networks.
Comments & Academic Discussion
Loading comments...
Leave a Comment