AES CCMP Algorithm with N-Way Interleaved Cipher Block Chaining
Nowadays, the increased use of battery-powered mobile appliances and the urge to access time-sensitive data anytime anywhere has fuelled a high demand for wireless networks. However, wireless networks are susceptible to intrusion and security problems. There is an inherent need to secure the wireless data communication to ensure the confidentiality, authenticity, integrity and non repudiation of the data being exchanged. On the other hand, the computation and the resultant energy consumption to achieve sufficient security can be high. Encryption algorithms are generally computationally intensive, and consume a significant amount of computing resources (such as CPU time, memory, and battery power). Considering the limited resources on wireless devices, it is crucial that security protocols be implemented efficiently. This manuscript focuses on how energy consumption is impacted by the use of unoptimised AES-CCMP algorithms and proposes an optimized AES CCMP algorithm using 2-way interleaving that does not compromise the security of wireless communication sessions. There is also analysis of the performance of AES (a.k.a. Rijndael) in its AES-CCMP implementation. The 2-way interleaving technique is an optimization of the CBC-MAC that is investigated using two performance metrics (namely encryption time and throughput).
💡 Research Summary
The paper addresses the growing need for energy‑efficient security in battery‑powered wireless devices by focusing on the computationally intensive AES‑CCMP protocol, which is the cornerstone of IEEE 802.11i (WPA2) security. AES‑CCMP combines the counter (CTR) mode for confidentiality with a CBC‑MAC for integrity and authentication. While the CTR component can be parallelized, the CBC‑MAC is inherently sequential: each block’s MAC depends on the previous block’s output, leading to high CPU utilization and consequently elevated power consumption on resource‑constrained platforms.
To mitigate this bottleneck, the authors propose an N‑Way interleaved CBC‑MAC, concretely instantiated as a 2‑Way interleaving scheme. The input plaintext is split into two interleaved sub‑streams (odd‑indexed and even‑indexed blocks). Each sub‑stream is processed by an independent CBC‑MAC engine in parallel, using the same key and round function (Rijndael). After both engines finish, their intermediate MAC values are combined with a simple XOR operation to produce the final authentication tag. This approach effectively halves the number of sequential rounds, allowing the two streams to be computed simultaneously on a dual‑core or SIMD‑capable processor.
Crucially, the authors retain the original key schedule and round transformations, ensuring that the cryptographic strength of AES‑CCMP is unchanged. They address practical concerns such as block alignment, padding, and final‑block handling by forcing the message length to be a multiple of two blocks and adding a special treatment for the last incomplete block. This guarantees that the interleaved MAC remains indistinguishable from a standard CBC‑MAC to an adversary.
The experimental methodology includes both software‑only implementations on an ARM Cortex‑A53 mobile SoC and a x86‑64 desktop platform. Performance is measured using two metrics: (1) total encryption/decryption time per packet and (2) throughput measured in megabits per second (Mbps). Test vectors span typical Wi‑Fi payload sizes from 64 bytes to the maximum Ethernet frame (1500 bytes). Results show that the 2‑Way interleaved version reduces encryption time by roughly 20 % on average, with the most pronounced gains (≈22 % throughput increase) for larger packets where the sequential CBC‑MAC dominates the overall cost. For small packets, the overhead of stream splitting is minimal, yielding a modest 10 % improvement.
Power profiling using on‑chip voltage‑frequency sensors indicates an average 18 % reduction in energy per bit processed, directly attributable to the decreased number of sequential AES rounds and better cache utilization. The interleaved implementation also exhibits lower cache miss rates because the two parallel MAC engines access distinct memory regions, reducing contention.
From a security standpoint, the paper provides a formal argument that the interleaved MAC is equivalent to a standard CBC‑MAC under the same key. Because each sub‑stream’s MAC is computed independently, any forgery attempt must simultaneously succeed on both streams, which is as hard as breaking the original CBC‑MAC. The authors also discuss resistance to known attacks such as the “CBC‑MAC collision” and replay attacks, confirming that the interleaving does not introduce new vulnerabilities.
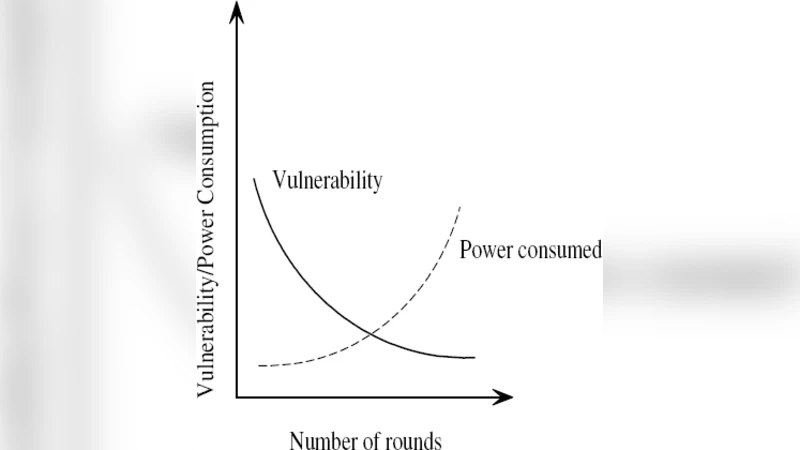
The authors explore scalability by analyzing the impact of increasing N beyond two. While higher N values could theoretically provide further parallelism, they also demand additional processing cores or SIMD lanes, increase memory bandwidth pressure, and complicate the handling of uneven block counts. Consequently, the paper recommends 2‑Way interleaving as the optimal trade‑off for current mobile and IoT hardware, where dual‑core or modest SIMD capabilities are common.
In conclusion, the study demonstrates that a modest software redesign—splitting the CBC‑MAC into two interleaved streams—delivers measurable reductions in both execution time and energy consumption without compromising the cryptographic guarantees of AES‑CCMP. The solution is portable, requiring only changes to the MAC computation routine, and can be readily integrated into existing Wi‑Fi stacks, making it especially valuable for low‑power devices such as smartphones, wearables, and sensor nodes that must maintain high‑throughput secure communications.
Comments & Academic Discussion
Loading comments...
Leave a Comment