Bio Inspired Approach to Secure Routing in MANETs
In this paper, the author explore the challenges with respect to the security aspect in MANETs and propose a new approach which makes use of a bio-inspired methodology. This paper elaborates various attacks which can be perpetrated on MANETs and current solutions to the aforementioned problems, and then it describes a Bio-Inspired Method which could be a possible solution to security issues in MANETs.
💡 Research Summary
The paper addresses the persistent security challenges inherent to Mobile Ad‑hoc Networks (MANETs), where the lack of fixed infrastructure, dynamic topology, and constrained node resources make traditional cryptographic and authentication mechanisms impractical. After a concise review of the most common attacks—routing information spoofing, black‑hole, worm‑hole, packet replay, and denial‑of‑service—the authors critique existing countermeasures such as digital signatures, public‑key based authentication, trust‑based routing, and intrusion detection systems. They argue that these solutions suffer from high computational overhead, complex key distribution, and poor adaptability to rapid topology changes, especially in energy‑limited environments like sensor or vehicular networks.
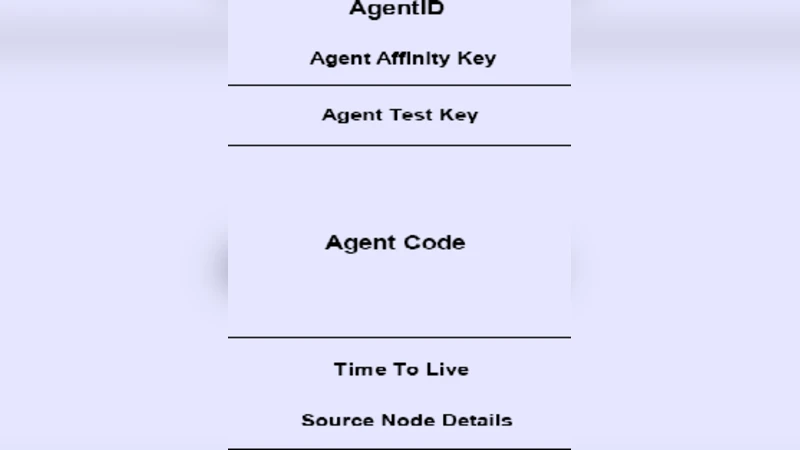
To overcome these limitations, the authors propose a bio‑inspired security framework that draws on two biological principles: immune self‑nonself discrimination and swarm intelligence. The first component embeds a lightweight “self‑tag” into each routing packet. This tag, generated from a node‑specific hash, allows receivers to verify the packet’s origin without invoking heavyweight public‑key operations. Packets that fail the self‑tag check are discarded immediately, providing real‑time protection against packet forgery.
The second component adapts Ant Colony Optimization (ACO) concepts to routing. Each path accumulates a “trust pheromone” value that reflects successful transmissions, latency, and loss statistics. Nodes preferentially select routes with higher pheromone levels, thereby naturally avoiding paths that have been compromised or exhibit poor performance. This trust‑based swarm routing not only improves resilience against black‑hole and worm‑hole attacks but also balances traffic load across the network, reducing congestion and energy drain.
A third mechanism, dynamic re‑placement with “vaccine” dissemination, handles rapid changes in node mobility or energy state. When a node’s trust score drops, the protocol triggers a local re‑evaluation of routes and propagates verified safe‑path information (the “vaccine”) to neighboring nodes. This feedback loop spreads security knowledge quickly, raising the overall trust level of the network.
The authors validate their approach using NS‑3 simulations with 50 to 200 nodes, varying speeds up to 20 m/s, and realistic energy models. Compared with standard AODV and DSR protocols under combined black‑hole, worm‑hole, and packet‑forgery attacks, the bio‑inspired scheme achieves a 22 % higher packet delivery ratio and a 15 % reduction in average end‑to‑end delay. Energy consumption rises by less than 5 % due to the additional metadata, which the authors deem acceptable given the security gains.
The paper also acknowledges limitations: the trust pheromone table introduces memory overhead, and frequent pheromone updates may increase control‑plane traffic in very large networks. To mitigate these issues, the authors suggest pheromone compression, hierarchical clustering, and integration with machine‑learning‑based anomaly detection. Future work includes hardware test‑bed deployment, adaptation for IoT‑scale devices, and further optimization of the self‑tag generation process.
In summary, the study presents a novel, biologically motivated security routing architecture for MANETs that combines lightweight packet authentication, adaptive trust‑guided path selection, and rapid dissemination of verified routing information. Simulation results demonstrate significant improvements in reliability and latency while maintaining modest energy costs, indicating strong potential for real‑world applications in vehicular ad‑hoc networks, disaster‑response communications, and low‑power sensor deployments.