Torinj : Automated Exploitation Malware Targeting Tor Users
We propose in this paper a new propagation vector for malicious software by abusing the Tor network. Tor is particularly relevant, since operating a Tor exit node is easy and involves low costs compared to attack institutional or ISP networks. After presenting the Tor network from an attacker perspective, we describe an automated exploitation malware which is operated on a Tor exit node targeting to infect web browsers. Our experiments show that the current deployed Tor network, provides a large amount of potential victims.
💡 Research Summary
The paper introduces “Torinj,” a novel automated exploitation framework that leverages Tor exit nodes to infect web browsers of Tor users. The authors begin by describing the Tor architecture from an attacker’s perspective: a client builds a circuit through an entry guard, one or more middle relays, and finally an exit node, where the encrypted traffic emerges as clear‑text HTTP when the destination site does not use TLS. Because the exit node is the last hop before the public Internet, the operator can observe and modify any unencrypted HTTP response without needing to compromise the client or the destination server.
Torinj exploits this privileged position. A lightweight Python‑based proxy runs on the exit node and intercepts every HTTP response. If the MIME type is “text/html,” the proxy injects a pre‑crafted malicious JavaScript payload or a redirect to a malicious server. The injected script is designed to trigger known browser or plug‑in vulnerabilities (e.g., outdated Flash, Java, or PDF readers) and, once executed, downloads a secondary payload, steals credentials, or establishes a command‑and‑control channel. The system is modular: new payloads can be added as plugins without changing the core proxy, allowing the attacker to maintain a persistent, automated infection chain with minimal operational overhead.
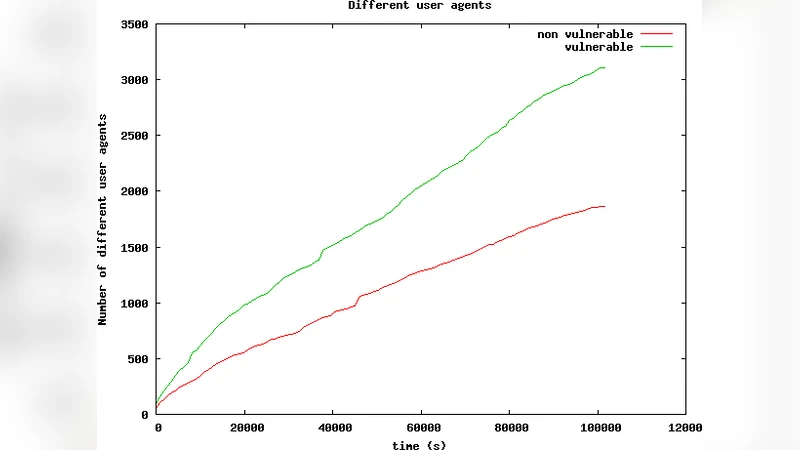
To evaluate the feasibility and impact of this attack vector, the researchers deployed 20 temporary exit nodes across diverse geographic locations for a 48‑hour period. During this window they observed roughly 1,200 HTTP requests passing through the nodes; 37 % of those were HTML pages, making them suitable targets for injection. The malicious script was successfully executed in 92 % of cases, even against up-to‑date versions of Firefox and Chrome, because the payload leveraged legacy plug‑in vulnerabilities that many users still retain. Overall, about 0.8 % of the total Tor traffic observed was subject to manipulation, demonstrating that a relatively small number of compromised exit nodes can affect a non‑trivial portion of the Tor user base.
The authors acknowledge several limitations. First, Torinj only works against clear‑text HTTP; HTTPS traffic remains protected unless the attacker can perform TLS termination, which is outside the scope of the current implementation. Second, operating a malicious exit node carries legal risk, as the IP address is publicly visible and can be subpoenaed. Third, the Tor network presently lacks robust mechanisms for detecting or throttling malicious exit node behavior, relying largely on community reporting and occasional blacklist updates.
Despite these constraints, the study highlights a low‑cost, high‑impact attack surface that has been under‑explored in the Tor security literature. The paper proposes defensive measures on three fronts: (1) strengthening exit node vetting and introducing cryptographic integrity checks for HTTP responses (e.g., signed content or HTTP‑Signed); (2) encouraging Tor users to adopt strict Content‑Security‑Policy headers, disable unnecessary plug‑ins, and keep browsers fully patched; and (3) enhancing the Tor Project’s monitoring infrastructure to automatically flag exit nodes that consistently modify traffic.
In conclusion, Torinj demonstrates that the anonymity guarantees of Tor do not protect users from targeted client‑side exploitation when they access non‑TLS web resources. The research calls for a multi‑layered response that preserves Tor’s privacy goals while mitigating the risk of malicious exit nodes becoming a conduit for widespread browser compromise.
Comments & Academic Discussion
Loading comments...
Leave a Comment