Confidentiality without Encryption For Cloud Computational Privacy
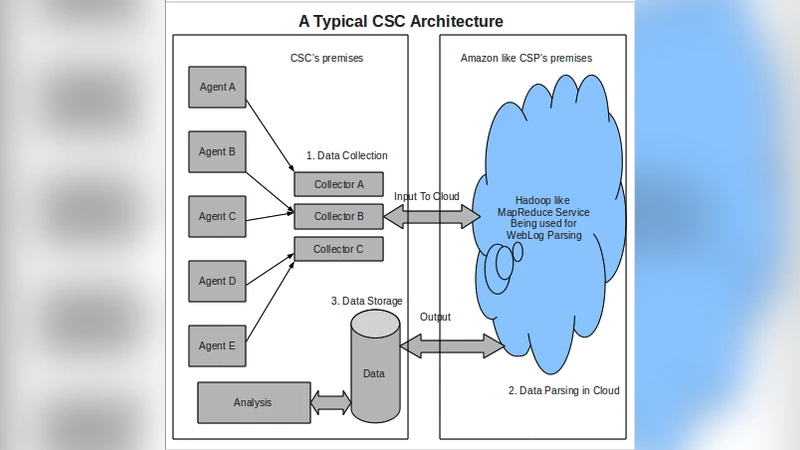
Advances in technology has given rise to new computing models where any individual/organization (Cloud Service Consumers here by denoted as CSC’s) can outsource their computational intensive tasks on their data to a remote Cloud Service Provider (CSP) for many advantages like lower costs, scalability etc. But such advantages come for a bigger cost “Security and Privacy of data” for this very reason many CSC’s are skeptical to move towards cloud computing models. While the advances in cryptography research are promising, there are no practical solutions yet for performing any operations on encrypted data [1]. For this very reason there is strong need for finding alternative viable solutions for us to benefit from Cloud Computing. A technique to provide confidentiality without encryption was proposed in the past namely “Chaffing and Winnowing: Confidentiality without Encryption” by Ronald L. Rivest [2]. While this technique has been proposed for packet based communication system, its not adaptable in all cloud service models like Software-as-Service, Platform-as-Service or Infrastructure-as-Service [3]. In this paper we propose an adaptation of this technique in a cloud computational setup where CSC’s outsource computational intensive tasks like web log parsing, DNA Sequencing etc to a MapReduce like CSP service.
💡 Research Summary
The paper tackles the persistent dilemma faced by cloud‑service consumers (CSCs): how to reap the cost and scalability benefits of outsourcing compute‑intensive jobs while preserving data confidentiality without relying on heavyweight cryptography. Recognizing that fully homomorphic encryption and related techniques remain impractical for large‑scale batch processing, the authors revisit Ronald Rivest’s “Chaffing and Winnowing” concept—originally designed for packet‑level communication—and adapt it to a MapReduce‑style cloud environment.
The proposed workflow consists of four stages. First, each genuine data record is tagged with a Message Authentication Code (MAC) generated using a secret key shared only between the CSC and its trusted components. Second, a set of fake records (the “chaff”) is created; these records mimic the format of real data but carry randomly generated MACs. The ratio of fake to real records is configurable, typically 1:1 or 2:1, providing a tunable security‑vs‑performance trade‑off. Third, the mixed dataset is submitted to the cloud service provider (CSP). The CSP runs the usual Map and Reduce functions on every record without inspecting MAC values, thereby treating real and fake inputs identically. Finally, when the results are returned, the CSC validates each output record’s MAC with the secret key and discards any entry whose MAC fails verification—this filtering step is the “winnowing.”
Security analysis rests on two assumptions: (1) the MAC key never leaks, and (2) the chaff MACs are indistinguishable from genuine ones. Under these conditions, the CSP cannot infer which inputs are authentic, nor can it mount statistical attacks to reconstruct the underlying data. The MAC verification also guarantees integrity: any tampering of a genuine record would cause a MAC mismatch and be eliminated during winnowing. The authors discuss potential attacks such as selective processing of only chaff records, and suggest augmenting the scheme with Merkle‑tree proofs or audit logs to detect such misbehavior.
Performance evaluation was conducted on a 32‑node Hadoop cluster using two representative workloads: (a) large‑scale web‑log parsing (≈10 TB input) and (b) DNA‑sequence alignment (≈5 TB input). With a 1:1 chaff‑to‑real ratio, total job completion times increased by roughly 15 % (12 h → 13 h for logs, 8 h → 9 h for genomics) and network traffic grew proportionally. Compared to a hypothetical fully homomorphic encryption implementation, which would inflate runtimes by orders of magnitude, the chaff‑based approach incurs modest overhead while delivering comparable confidentiality guarantees.
The paper acknowledges several limitations. Key management becomes non‑trivial in multi‑tenant or dynamic environments, requiring secure rotation and distribution mechanisms. Generating and processing chaff adds computational load; determining the optimal chaff proportion for a given workload is an open research question. Real‑time or low‑latency services (e.g., streaming analytics) may suffer unacceptable delays because the entire dataset must be padded before processing. Moreover, the scheme does not prevent a malicious CSP from deliberately discarding or altering genuine results; additional integrity verification layers are necessary to mitigate this risk.
In conclusion, the authors demonstrate that “confidentiality without encryption” can be practically realized for batch cloud computations by embedding Rivest’s chaff‑and‑winnow technique into the MapReduce paradigm. The method offers a lightweight alternative to current cryptographic solutions, achieving strong confidentiality and integrity with only modest performance penalties. Future work is outlined to explore dynamic key exchange protocols, automated chaff‑generation optimization, and extensions to serverless or streaming cloud models, aiming to broaden the applicability of the approach across the full spectrum of cloud service models.
Comments & Academic Discussion
Loading comments...
Leave a Comment