Security of the DNS Protocol - Implementation and Weaknesses Analyses of DNSSEC
Today, Internet offers many critical applications. So, it becomes very crucial for Internet service providers to ensure traceability of operations and to secure data exchange. Since all these communications are based on the use of the Domain Name System (DNS) protocol, it becomes necessary to think to enhance and secure it by proposing a secure version of this protocol that can correct the whole or a part of the DNS protocol weaknesses and vulnerabilities. In this context, DNSsec was created by the IETF to ensure the integrity of DNS data and authentication of the source of such data. DNSsec is based on the key cryptography public to provide different security services. In the present paper, we will present first the DNS protocol and its weaknesses. After that, we will be interested in studying the DNSsec implementation and data exchange, and then give a deep analysis of its weaknesses.
💡 Research Summary
The paper begins by emphasizing the indispensable role of the Domain Name System (DNS) in today’s Internet‑driven society and points out that the original DNS design, conceived in an era when security was not a primary concern, lacks any built‑in authentication or integrity verification. As a result, classic attacks such as cache poisoning, spoofing, man‑in‑the‑middle, and amplification‑based DDoS are trivially possible. The authors describe how the UDP‑centric transport further aggravates the problem because oversized responses trigger IP fragmentation, which many middleboxes drop, leading to denial‑of‑service conditions.
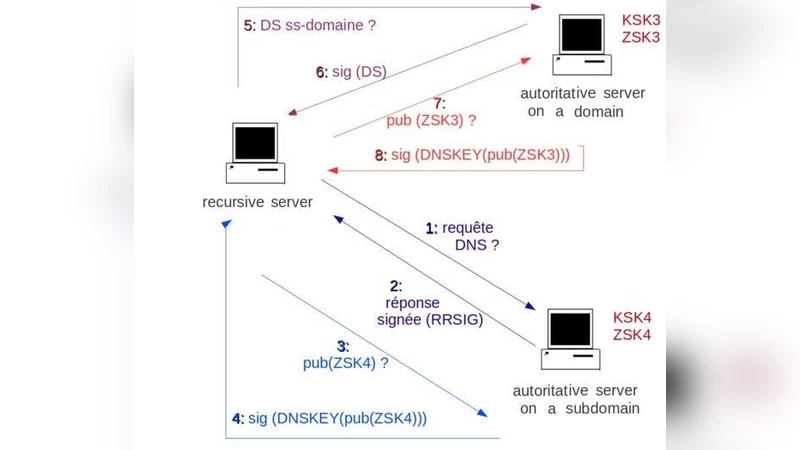
To address these systemic flaws, the IETF introduced DNSSEC (Domain Name System Security Extensions). DNSSEC augments DNS with public‑key cryptography and digital signatures, enabling resolvers to verify that a received RR set has not been altered and that it originates from an authoritative source. The paper details the core components: DNSKEY records publish a zone’s public keys; RRSIG records contain signatures generated with the corresponding private keys; DS (Delegation Signer) records link a child zone to its parent, forming a chain of trust that ultimately terminates at the root’s trust anchor. The separation of Key Signing Keys (KSK) and Zone Signing Keys (ZSK) is explained as a means to simplify key rollover and reduce the performance impact of frequent signing operations. The authors also discuss the use of NSEC and NSEC3 records for authenticated denial‑of‑existence, noting that NSEC3’s hash‑based approach mitigates zone‑enumeration attacks to some extent.
The bulk of the analysis focuses on the practical weaknesses that emerge when DNSSEC is deployed. First, signed records increase DNS payload size dramatically, often exceeding the traditional 512‑byte UDP limit. This forces the use of TCP fallback or EDNS0 extensions, both of which introduce latency and expose the system to fragmentation‑related attacks. Second, the key‑rollover process is intricate: KSK and ZSK have different lifetimes, TTLs, and activation windows, and any mis‑timing can break the chain of trust, rendering an entire zone unverifiable. Third, the existence proofs provided by NSEC/NSEC3 inadvertently enable full zone enumeration, raising privacy concerns for domain owners who wish to keep their sub‑domains hidden. Fourth, most current deployments rely on RSA‑SHA‑1 or RSA‑SHA‑256 signatures; the paper warns that these algorithms will become obsolete in the face of quantum‑computing threats, and it highlights emerging support for ECC‑based schemes such as ECDSA and Ed25519 as a necessary evolution. Fifth, the trust anchor model is a single point of failure: compromise of the root key would invalidate the global DNSSEC validation infrastructure, prompting the authors to suggest multi‑anchor or transparency‑log mechanisms as mitigations.
The authors then survey the state of DNSSEC adoption. While the root zone and several top‑level domains (TLDs) have been signed, the overall proportion of signed domains remains low, largely due to operational complexity, increased bandwidth consumption, and the need for careful key management. The paper concludes that DNSSEC successfully addresses DNS data integrity but does not provide confidentiality, and its deployment introduces performance penalties, management overhead, and new attack surfaces. The authors call for continued standard‑body work to refine algorithms, simplify rollover procedures, improve privacy‑preserving denial‑of‑existence methods, and integrate DNSSEC with complementary technologies such as DANE, DNS‑over‑HTTPS, and DNS‑based authentication frameworks. Only through such holistic evolution can the DNS ecosystem achieve the robust security required for the future Internet.