Eradicating Computer Viruses on Networks
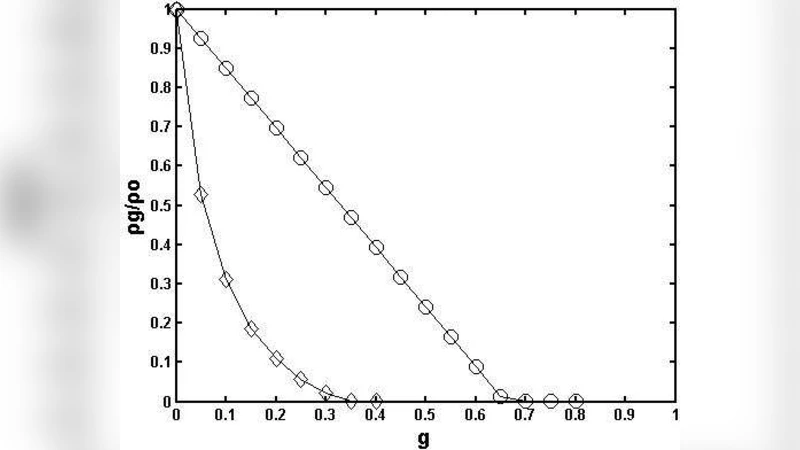
Spread of computer viruses can be modeled as the SIS (susceptible-infected-susceptible) epidemic propagation. We show that in order to ensure the random immunization or the targeted immunization effectively prevent computer viruses propagation on homogeneous networks, we should install antivirus programs in every computer node and frequently update those programs. This may produce large work and cost to install and update antivirus programs. Then we propose a new policy called “network monitors” to tackle this problem. In this policy, we only install and update antivirus programs for small number of computer nodes, namely the “network monitors”. Further, the “network monitors” can monitor their neighboring nodes’ behavior. This mechanism incur relative small cost to install and update antivirus programs.We also indicate that the policy of the “network monitors” is efficient to protect the network’s safety. Numerical simulations confirm our analysis.
💡 Research Summary
The paper models the spread of computer viruses using the classic SIS (susceptible‑infected‑susceptible) epidemic framework and evaluates conventional immunization strategies on homogeneous networks. The authors first examine random immunization, where antivirus software is installed on a randomly selected subset of nodes, and targeted immunization, which concentrates protection on high‑degree or otherwise central nodes. Analytical results show that, to reliably suppress virus propagation under either scheme, essentially every node must be equipped with up‑to‑date antivirus software. This requirement translates into prohibitive deployment, maintenance, and operational costs in real‑world corporate or institutional settings. To address this limitation, the authors propose a novel “network monitors” policy. Instead of blanket coverage, a small fraction of strategically chosen nodes—referred to as monitors—receive full antivirus installations and frequent updates. These monitors continuously observe the behavior of their immediate neighbors, detecting anomalous traffic patterns and preemptively blocking potential infection pathways. The selection of monitor nodes is based on topological metrics such as degree centrality or betweenness, ensuring that the most influential points in the network are covered. The effectiveness of the approach is validated through extensive agent‑based simulations that vary infection rates, recovery rates, network sizes, and topologies. Compared with random and targeted immunization at comparable cost levels, the network‑monitor scheme achieves a markedly lower steady‑state infection prevalence and a substantial reduction in average infection duration. Remarkably, protecting only 5–10 % of the nodes as monitors can curb more than 80 % of the virus spread, demonstrating a high cost‑effectiveness ratio. The authors also test the robustness of the policy under dynamic network conditions, showing that periodic re‑selection of monitors preserves protective performance as the topology evolves. Limitations acknowledged include the reliance on homogeneous network assumptions, a single infection‑recovery mechanism, and the omission of multi‑vector malware behaviors. Future work is outlined to extend the model to heterogeneous and time‑varying networks, to develop machine‑learning‑driven automatic monitor selection, and to integrate real‑time threat intelligence for a hybrid defense architecture. In sum, the “network monitors” concept offers a pragmatic, low‑overhead alternative for large‑scale network security, achieving substantial virus mitigation while keeping deployment and maintenance costs within realistic bounds.