Detection of Configuration Vulnerabilities in Distributed (Web) Environments
Many tools and libraries are readily available to build and operate distributed Web applications. While the setup of operational environments is comparatively easy, practice shows that their continuous secure operation is more difficult to achieve, many times resulting in vulnerable systems exposed to the Internet. Authenticated vulnerability scanners and validation tools represent a means to detect security vulnerabilities caused by missing patches or misconfiguration, but current approaches center much around the concepts of hosts and operating systems. This paper presents a language and an approach for the declarative specification and execution of machine-readable security checks for sets of more fine-granular system components depending on each other in a distributed environment. Such a language, building on existing standards, fosters the creation and sharing of security content among security stakeholders. Our approach is exemplified by vulnerabilities of and corresponding checks for Open Source Software commonly used in today’s Internet applications.
💡 Research Summary
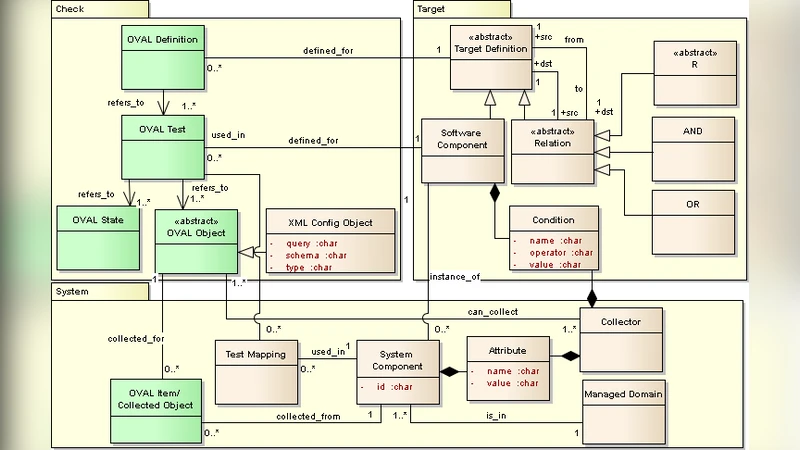
The paper addresses a pressing problem in modern web‑centric enterprises: while building distributed applications with containers, micro‑services, and cloud‑native components has become relatively straightforward, maintaining their security over time remains difficult. Traditional vulnerability scanners and validation tools focus on host‑level assets—operating‑system patches, open ports, or known CVE‑linked binaries—and consequently miss many configuration‑related weaknesses that arise from the interaction of multiple components in a distributed environment. To fill this gap, the authors propose a Declarative Configuration Check Language (DCCL) together with an execution framework that enables security analysts to write machine‑readable, shareable checks for fine‑grained system components and their inter‑dependencies.
Core Design Principles
- Component‑Centric Modeling – Every software artifact (web server, application server, database, library, proxy, etc.) is represented as a “Component” object with attributes such as name, version, exposed interfaces, and required capabilities. The model reuses existing standards like CPE (Common Platform Enumeration) for identification and aligns with CVE metadata for vulnerability mapping.
- Explicit Dependency Graphs – Relationships such as
depends_on,exposes, andrequiresare first‑class constructs, allowing the language to capture the topology of a distributed stack (e.g., Nginx → Tomcat → OpenSSL). This graph‑based view is essential for detecting configuration mismatches that only become exploitable when two or more components interact. - Declarative Policy Syntax – DCCL uses a concise, if‑then‑else style syntax combined with logical operators. Complex security policies (e.g., “if component A runs version < 2.5 and component B requires TLS ≥ 1.2 then raise a warning”) can be expressed in a single line, improving readability and maintainability.
- Standard‑Based Execution Engine – DCCL scripts are serialized as JSON‑LD, making them easy to version‑control and distribute. At runtime, the engine gathers live configuration data (via existing tools such as OpenSCAP, OVAL, or custom inventory agents), maps it to the component model, and evaluates the declarative rules. Because the engine reuses mature assessment frameworks, implementation overhead is low.
Implementation and Empirical Evaluation
The authors built a testbed consisting of a typical three‑tier web application: Nginx as a reverse proxy, Apache Tomcat as the application server, MySQL as the database, and OpenSSL for TLS termination. They selected three well‑known vulnerabilities that illustrate different layers of configuration risk:
- CVE‑2017‑9798 (Apache HTTP Server 2.4.49 Path Traversal) – a classic server‑side flaw.
- CVE‑2020‑9484 (Tomcat 9.0.31 Remote Code Execution) – an application‑server issue that can be triggered only when a vulnerable JAR is present.
- CVE‑2014‑0160 (OpenSSL Heartbleed) – a library‑level bug that becomes exploitable when TLS termination is performed by an outdated OpenSSL version.
For each CVE, the authors authored a DCCL rule that captures not only the vulnerable component version but also the required configuration context (e.g., “Tomcat must be linked against OpenSSL ≥ 1.0.2”). They then executed the DCCL engine against the testbed under two scenarios: (a) a correctly configured stack, and (b) a deliberately mis‑configured stack where Nginx only supports TLS 1.0 while Tomcat expects TLS 1.2, and where an outdated OpenSSL library is present behind the proxy.
Traditional scanners detected the individual vulnerable binaries in scenario (b) but failed to flag the configuration drift between Nginx and Tomcat, nor the fact that the vulnerable OpenSSL was still reachable via the proxy. The DCCL engine, by evaluating the dependency graph, raised three alerts: (i) mismatched TLS versions, (ii) presence of an unpatched OpenSSL library, and (iii) the combination of Tomcat 9.0.31 with the vulnerable OpenSSL, which together constitute a realistic attack vector. The total analysis time averaged 12 seconds, demonstrating suitability for integration into CI/CD pipelines.
Sharing, Reuse, and Automation
A major advantage of the declarative approach is the ease of sharing security content. DCCL rules can be stored in version‑controlled repositories (e.g., GitHub) and packaged as SCAP content bundles, enabling organizations to exchange vetted checks. When a new CVE is published, the corresponding CPE identifiers can be automatically fetched, and a templated DCCL rule can be generated, reducing manual effort. The authors illustrate a CI/CD integration where the DCCL engine runs as a Jenkins stage; any policy violation blocks the deployment and posts a detailed report to a security dashboard, thereby preventing configuration drift from reaching production.
Limitations and Future Work
The paper acknowledges several constraints:
- Learning Curve – Security engineers must become familiar with DCCL syntax and the underlying component model. The authors propose a rule‑generation wizard to mitigate this.
- Inventory Accuracy – The engine’s effectiveness hinges on a reliable inventory of component versions and configurations; incomplete data leads to false negatives.
- Dynamic Environments – Serverless functions and highly elastic Kubernetes clusters may change their composition faster than static inventory collection can keep up. The authors suggest extending the framework with runtime telemetry (e.g., service‑mesh metrics) and exploring machine‑learning techniques to infer dependencies automatically.
Future research directions include (1) automated extraction of dependency graphs from container orchestration manifests, (2) integration of dynamic analysis data (e.g., network flows, logs) to enrich the component model, and (3) evaluation of the approach at scale in large‑enterprise cloud environments.
Conclusion
The authors present a novel, standards‑based declarative language and execution framework that shift vulnerability assessment from a host‑centric view to a configuration‑centric perspective. By modeling components and their relationships explicitly, DCCL can detect subtle, real‑world security gaps that traditional scanners overlook. The empirical results validate the concept, and the emphasis on shareable, reusable security content aligns with modern DevSecOps practices. While challenges remain—particularly around dynamic environments and inventory completeness—the work lays a solid foundation for more holistic, automated security assurance in distributed web ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment