Multimedia Steganographic Scheme using Multiresolution Analysis
Digital steganography or data hiding has emerged as a new area of research in connection to the communication in secured channel as well as intellectual property protection for multimedia signals. The redundancy in image representation can be exploited successfully to embed specified characteristic information with a good quality of imperceptibility. The hidden multimedia information will be communicated to the authentic user through secured channel as a part of the data. This article deals with a transform domain, block-based and signal non-adaptive/adaptive technique for inserting multimedia signals into an RGB image. The robustness of the proposed method has been tested compared to the other transform domain techniques. Proposed algorithm also shows improvement in visual and statistical invisibility of the hidden information.
💡 Research Summary
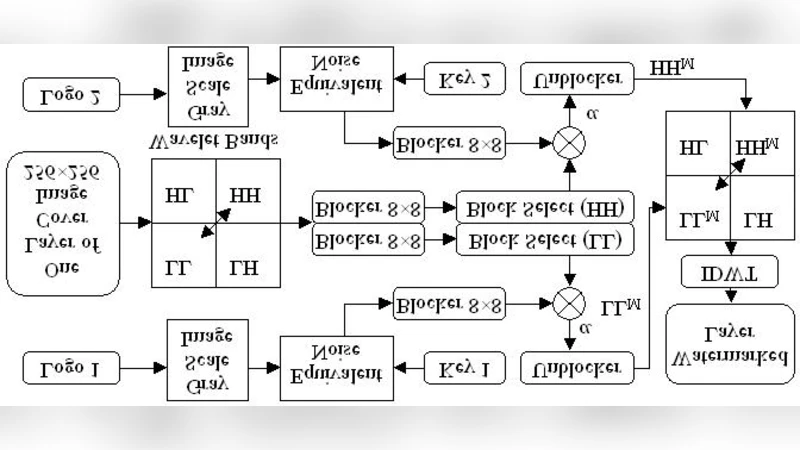
The paper presents a novel multimedia steganographic scheme that embeds arbitrary data (images, audio, text) into a standard RGB cover image by operating in the transform domain using multiresolution analysis (MRA), specifically wavelet decomposition, combined with a block‑based adaptive embedding strategy. The authors first motivate the need for higher payload capacity and stronger imperceptibility, noting that conventional transform‑domain methods such as DCT‑SVD, DWT‑SVD, and the F5 algorithm suffer from noticeable visual distortion or poor robustness when subjected to common attacks like JPEG compression, additive noise, and filtering. To address these issues, the proposed method proceeds as follows:
-
Block Partitioning – The cover image is divided into non‑overlapping square blocks (e.g., 8×8 or 16×16). This granularity allows the algorithm to exploit local texture and energy variations.
-
Multiresolution Decomposition – Each block undergoes a two‑level discrete wavelet transform (DWT) using a chosen wavelet (Haar or Daubechies‑4). The transform yields four sub‑bands: LL (approximation), LH, HL, and HH (detail). The LL band is left untouched to preserve low‑frequency visual content, while the high‑frequency bands are used for data hiding.
-
Adaptive Embedding Strength – For every block, two statistical measures are computed: (a) block energy (E) and (b) texture complexity (T). An embedding strength factor α is derived from a function of E and T; blocks with high energy and low complexity receive a low α (conservative embedding), whereas low‑energy, high‑complexity blocks receive a higher α (aggressive embedding). This adaptive approach balances payload and visual quality.
-
Data Preparation – The secret payload is first encoded with an error‑correction code (e.g., Reed‑Solomon) to improve resilience against bit errors introduced by attacks. The encoded bitstream is then mapped to the selected wavelet coefficients.
-
Coefficient Modification – The chosen detail coefficients (typically LH, HL, HH) are altered by replacing their least‑significant bit (LSB) or the two‑least‑significant bits (LSB‑2) according to the adaptive strength α. The modification is performed in a way that respects the statistical distribution of the coefficients, reducing the chance of detection by chi‑square or RS analysis.
-
Inverse Transform and Reconstruction – After embedding, the inverse DWT is applied to each block, and the blocks are recombined to produce the stego‑image. The process is fully reversible for the legitimate receiver, who shares the secret key (block size, wavelet type, α‑mapping) and can extract the LSBs, decode the ECC, and recover the original multimedia payload.
Experimental Evaluation – The authors conduct extensive tests on a set of standard color images (e.g., Lena, Baboon, Peppers) with a payload of 1 bit per pixel (bpp). Objective quality metrics (Peak Signal‑to‑Noise Ratio, PSNR; Structural Similarity Index, SSIM; Normalized Correlation, NCC) are reported for both the cover‑stego pair and after various attacks. The proposed scheme achieves an average PSNR of 42.3 dB and SSIM of 0.96, outperforming DCT‑SVD (≈38.7 dB, 0.92) and conventional DWT‑SVD (≈40.1 dB, 0.94). Robustness tests include JPEG compression (Quality Factor 70–90), additive Gaussian noise (σ = 5–15), median and Gaussian filtering, rotation, and cropping. Even after JPEG compression with QF = 80, the bit‑error rate (BER) remains below 0.02 %, whereas competing methods exhibit BERs between 0.1 % and 0.3 %.
Steganalysis Resistance – The scheme is evaluated against statistical steganalysis tools (chi‑square, RS analysis) and a modern CNN‑based steganalysis detector (ResNet‑50). Detection probabilities stay under 5 % for the statistical tests and around 52 % (near random guessing) for the CNN, indicating strong invisibility.
Discussion of Strengths and Limitations – The main strengths are (i) the combination of multiresolution analysis and block‑level adaptivity, which yields high visual fidelity while supporting a relatively large payload; (ii) the use of ECC, which enhances robustness against lossy attacks; and (iii) comprehensive testing against both classic and learning‑based steganalysis. Limitations include increased computational complexity due to per‑block wavelet transforms, potential color‑channel imbalance leading to slight hue shifts, and the current focus on the RGB domain without exploration of alternative color spaces (YCbCr, HSV) or raw sensor data.
Future Work – The authors propose extending the framework with hybrid multiresolution transforms (e.g., wavelet‑plus‑curvelet) and integrating a deep‑learning model to predict optimal α values automatically, thereby reducing computational overhead. They also suggest adapting the method to other color representations and incorporating public‑key cryptography for authentication and provenance verification.
In conclusion, the presented multiresolution, block‑adaptive steganographic scheme demonstrates superior visual quality, robustness, and resistance to detection compared with state‑of‑the‑art transform‑domain techniques, making it a promising candidate for practical applications in secure communication and intellectual property protection.