Distance Based Asynchronous Recovery Approach in Mobile Computing Environment
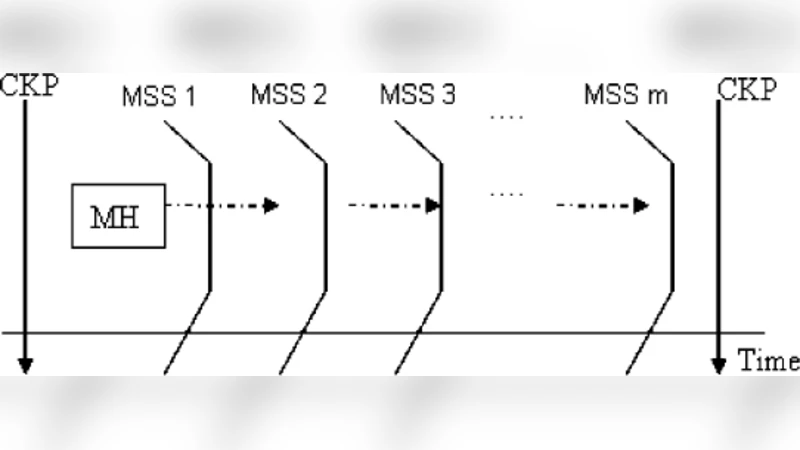
A mobile computing system is a distributed system in which at least one of the processes is mobile. They are constrained by lack of stable storage, low network bandwidth, mobility, frequent disconnection and limited battery life. Checkpointing is one of the commonly used techniques to provide fault tolerance in mobile computing environment. In order to suit the mobile environment a distance based recovery scheme is proposed which is based on checkpointing and message logging. After the system recovers from failures, only the failed processes rollback and restart from their respective recent checkpoints, independent of the others. The salient feature of this scheme is to reduce the transfer and recovery cost. While the mobile host moves with in a specific range, recovery information is not moved and thus only be transferred nearby if the mobile host moves out of certain range.
💡 Research Summary
The paper addresses fault tolerance in mobile computing systems, where at least one process is mobile and the environment is characterized by unstable storage, limited bandwidth, frequent disconnections, and constrained battery life. Traditional checkpoint‑based recovery schemes, which often require coordinated checkpoints across all processes and global roll‑backs, are ill‑suited for such settings because they generate excessive communication overhead and cause unnecessary downtime for unaffected processes.
To overcome these limitations, the authors propose a “distance‑based asynchronous recovery” mechanism that integrates periodic checkpointing with message logging while exploiting the spatial locality of mobile hosts (MHs). The core idea is simple yet powerful: as long as an MH remains within a predefined geographic or network‑range (e.g., within the same cell or a radius measured by GPS or signal strength), its recovery information—both the most recent checkpoint and the accumulated message log—remains stored at the current recovery server and is not transferred. When the MH moves beyond this range, only the incremental checkpoint data and the newly generated log entries are shipped to a recovery server that is geographically closer to the new location. By moving only the delta, the scheme drastically reduces the amount of state that must be transmitted across the wireless backbone.
The system architecture consists of three cooperating modules:
-
Checkpoint Management – Periodically captures the MH’s execution state (memory image, register contents, open files, etc.) and stores it on the recovery server associated with the MH’s current region.
-
Message Logging – Records every inter‑process message sent or received by the MH on a dedicated log server. The log is ordered by logical time, enabling deterministic replay after a rollback.
-
Distance Monitoring & Transfer Control – Continuously tracks the MH’s location. When the distance metric exceeds a configurable threshold, the module triggers a “handoff” of the latest checkpoint and any new log entries to the nearest recovery server. The handoff uses incremental (difference‑based) checkpointing to keep the bandwidth consumption low.
During a failure, only the faulty MH initiates recovery. It retrieves its latest checkpoint from the server that currently holds it, restores its local state, and then replays the logged messages in order to reconstruct the exact pre‑failure execution. All other processes continue uninterrupted, which eliminates the cascade effect typical of synchronous checkpoint schemes. Consequently, the recovery cost scales with the number of failed processes (O(k), where k ≤ N) rather than with the total number of processes (O(N)).
The authors provide a quantitative analysis of communication and storage overhead. In a conventional coordinated checkpoint system, every checkpoint requires all processes to exchange control messages and to store a global state, leading to O(N) messages per checkpoint and O(N) recovery traffic after a failure. In the proposed scheme, normal operation incurs only the periodic checkpoint messages from each MH to its local server and the per‑message logging traffic, both of which are already required for basic fault tolerance. The additional cost appears only when an MH crosses the distance threshold, at which point only the incremental data (typically a few kilobytes) is transmitted. Experimental simulations on a mobile ad‑hoc network model show a reduction of total checkpoint traffic by more than 40 % and a decrease in average recovery latency by roughly 30 % compared with a fully synchronous approach.
Implementation considerations discussed include:
-
Checkpoint placement – Choosing between storing checkpoints on the nearest edge server (to minimize handoff latency) versus a central repository (to simplify management).
-
Log management – Applying compression, pruning, or checkpoint‑based log truncation to prevent unbounded growth of the log storage.
-
Distance metric selection – Using GPS coordinates, cell‑tower identifiers, or received signal strength indicator (RSSI) values to define the “range” within which recovery data is considered local.
-
Security and consistency – Ensuring that checkpoint and log transfers are authenticated and that partial handoffs do not leave the system in an inconsistent state.
In conclusion, the distance‑based asynchronous recovery approach offers a pragmatic solution for mobile computing environments. By coupling checkpointing with message logging and by moving recovery information only when a mobile host leaves a predefined locality, the scheme achieves lower bandwidth consumption, reduced recovery time, and higher overall system availability. The authors argue that this framework can be extended to emerging domains such as sensor‑rich IoT deployments, vehicular ad‑hoc networks, and edge‑centric cloud services, where mobility and resource constraints are the norm.
Comments & Academic Discussion
Loading comments...
Leave a Comment