Security Analysis of Vehicular Ad Hoc Networks (VANET)
Vehicular Ad Hoc Networks (VANET) has mostly gained the attention of today’s research efforts, while current solutions to achieve secure VANET, to protect the network from adversary and attacks still not enough, trying to reach a satisfactory level, for the driver and manufacturer to achieve safety of life and infotainment. The need for a robust VANET networks is strongly dependent on their security and privacy features, which will be discussed in this paper. In this paper a various types of security problems and challenges of VANET been analyzed and discussed; we also discuss a set of solutions presented to solve these challenges and problems.
💡 Research Summary
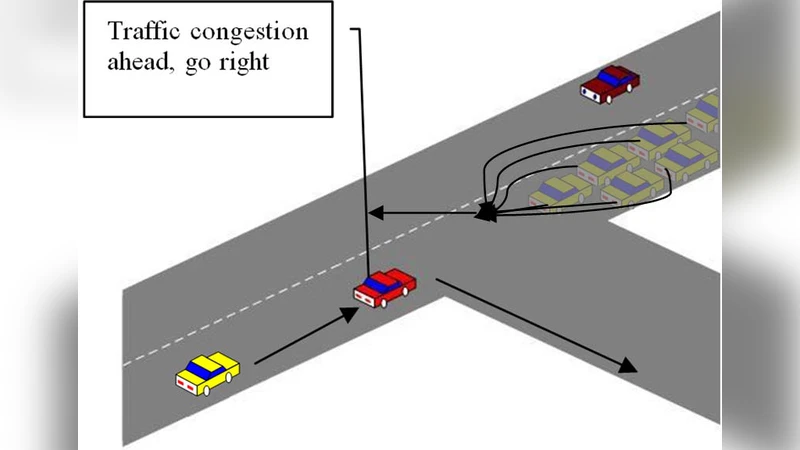
The paper provides a comprehensive examination of security and privacy challenges in Vehicular Ad Hoc Networks (VANETs), a technology that underpins many emerging intelligent transportation services such as collision avoidance, traffic management, and autonomous driving support. It begins by outlining the unique characteristics of VANETs—high node mobility, short-lived connections, and reliance on open wireless media—that differentiate them from traditional fixed networks and make them especially vulnerable to a wide range of attacks. The authors identify four core security requirements: authentication and identity verification, data integrity, privacy protection, and availability. Each requirement is mapped to specific threat categories, including physical-layer jamming, radio frequency interference, message forgery, replay attacks, Sybil attacks, location tracking, and both DoS and DDoS attacks that can cripple cooperative vehicular services.
A detailed survey of existing countermeasures follows. Public Key Infrastructure (PKI) and certificate‑based authentication are recognized as foundational, yet their overhead in certificate distribution and revocation is problematic for the low‑latency environment of VANETs. Group signatures and ring signatures provide anonymity but suffer from heavy verification costs and complex group management. Blockchain‑based consensus mechanisms promise decentralized trust, immutability, and tamper‑evidence, but block generation latency, storage demands, and energy consumption conflict with real‑time vehicular constraints. Machine‑learning‑driven intrusion detection systems can identify anomalous traffic patterns on the fly, yet they are prone to false positives and require extensive, representative training data that is difficult to obtain in dynamic road scenarios. Lightweight cryptographic primitives such as elliptic‑curve signatures (e.g., Ed25519) and hardware security modules (TPM, HSM) mitigate computational load, but a lack of cross‑manufacturer standardization hampers interoperability.
The authors critically evaluate these solutions, highlighting that most research addresses isolated threats rather than providing a holistic, multi‑layered defense. They point out the scarcity of protocols that simultaneously satisfy authentication, privacy, integrity, and availability while meeting the stringent latency and scalability demands of VANETs. Moreover, many proposals remain confined to simulation environments, lacking validation in real‑world testbeds, and there is an evident gap in standardized interfaces that would enable seamless cooperation among vehicle manufacturers, infrastructure operators, and service providers.
In the concluding section, the paper proposes a roadmap for future work. It advocates for a multi‑tiered security architecture that integrates protective mechanisms at the physical, link, network, and application layers, thereby creating defense‑in‑depth. A hybrid authentication framework is suggested, combining dynamic key exchange, group‑based credentials, and short‑lived pseudonyms to balance strong identity assurance with privacy. For privacy preservation, the authors recommend differential privacy techniques and traffic‑mixing strategies to obscure location information without sacrificing the timeliness of safety messages. To address data integrity and availability, they propose a lightweight consensus model that merges blockchain’s immutability with Directed Acyclic Graph (DAG) structures, reducing block finality time while maintaining tamper resistance. Finally, they call for active participation in international standardization bodies to define interoperable security APIs and for extensive field trials using real vehicles to assess performance, robustness, and user acceptance. By following this integrated approach, the paper argues that VANETs can evolve from a research prototype into a secure, reliable backbone for next‑generation intelligent transportation systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment