Information Diffusion and External Influence in Networks
Social networks play a fundamental role in the diffusion of information. However, there are two different ways of how information reaches a person in a network. Information reaches us through connections in our social networks, as well as through the influence of external out-of-network sources, like the mainstream media. While most present models of information adoption in networks assume information only passes from a node to node via the edges of the underlying network, the recent availability of massive online social media data allows us to study this process in more detail. We present a model in which information can reach a node via the links of the social network or through the influence of external sources. We then develop an efficient model parameter fitting technique and apply the model to the emergence of URL mentions in the Twitter network. Using a complete one month trace of Twitter we study how information reaches the nodes of the network. We quantify the external influences over time and describe how these influences affect the information adoption. We discover that the information tends to “jump” across the network, which can only be explained as an effect of an unobservable external influence on the network. We find that only about 71% of the information volume in Twitter can be attributed to network diffusion, and the remaining 29% is due to external events and factors outside the network.
💡 Research Summary
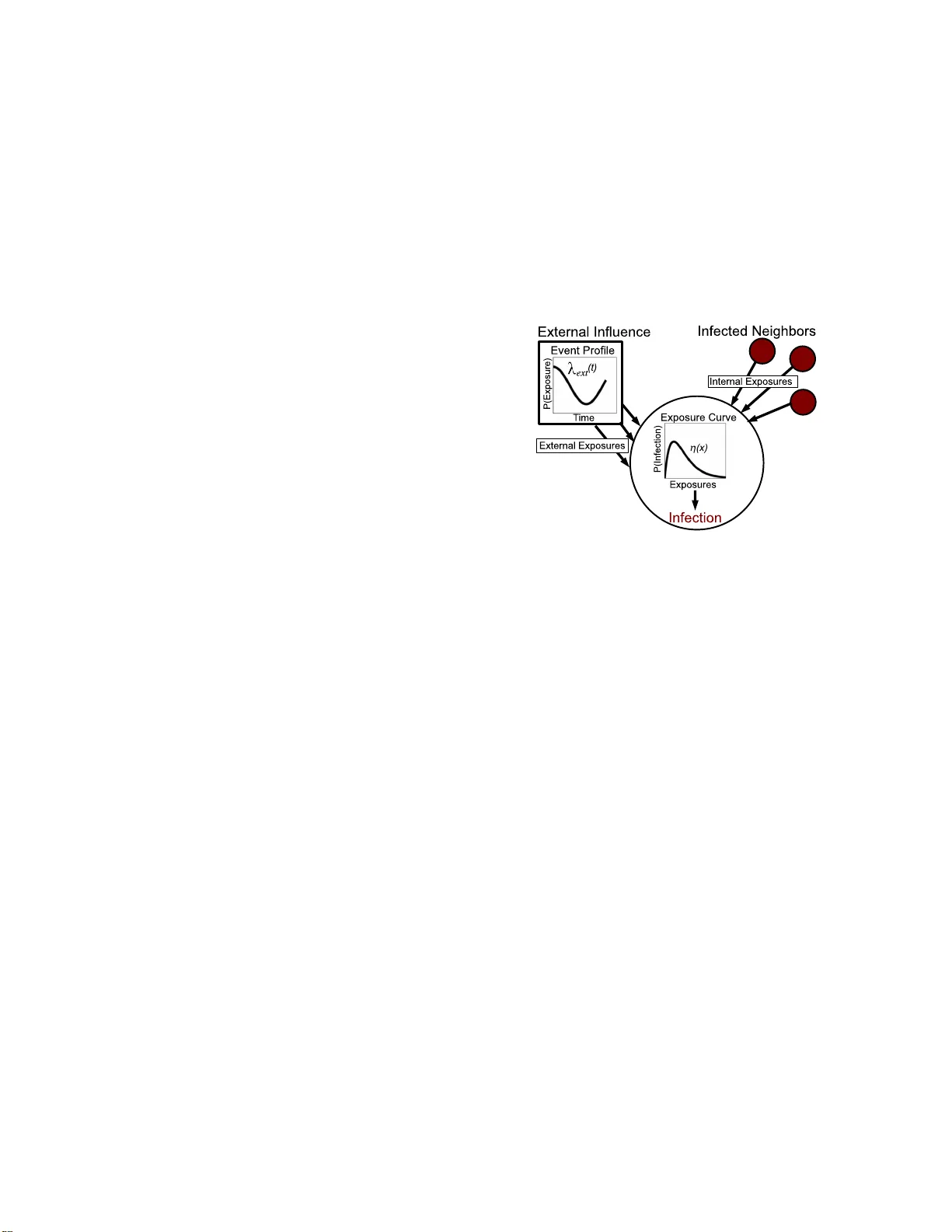
The paper tackles a fundamental limitation of most diffusion models on social networks: the assumption that information spreads exclusively through edges connecting users. In reality, users are also exposed to information from external sources such as news media, blogs, or offline events. To capture both pathways, the authors propose a stochastic diffusion framework that simultaneously models internal contagion (node‑to‑node transmission) and external influence (direct infection from outside the network).
Model formulation
Each node i can become “infected” (i.e., mention a URL) at time t via two independent mechanisms. The internal mechanism is governed by an internal hazard function λ_int(Δt), where Δt is the elapsed time since a neighbor j became infected. This function captures the decreasing likelihood of transmission as time passes after a neighbor’s adoption. The external mechanism is described by a time‑varying external infection rate η(t), which is the same for all nodes and reflects the aggregate effect of out‑of‑network events (breaking news, TV coverage, celebrity endorsements, etc.). The overall infection intensity for node i at time t is the sum λ_int(·) from all infected neighbors plus η(t). The model treats infection events as points of a non‑homogeneous Poisson process, allowing the use of likelihood‑based inference.
Parameter inference
Because η(t) and λ_int(·) are not directly observable, the authors develop an efficient Expectation‑Maximization‑style algorithm. In the E‑step, each observed infection time is probabilistically assigned to either an internal or external cause based on the current estimates of the two functions. In the M‑step, the assignments are aggregated over all nodes and time windows to update η(t) and λ_int(·) in a non‑parametric fashion (piecewise constant histograms). The algorithm scales linearly with the number of edges, making it feasible for networks with millions of users and billions of edges.
Data and experimental setup
The authors apply the method to a complete one‑month Twitter firehose (approximately 20 billion tweets). They extract all tweets containing URLs, identify the first appearance of each URL, and construct a follower graph among the users who mentioned that URL. This yields a dynamic diffusion cascade for each URL together with the underlying social graph.
Key findings
- External influence is substantial – On average, 29 % of all URL mentions are best explained by the external infection rate η(t), while 71 % are attributable to network diffusion.
- Temporal spikes in η(t) align with real‑world events – Peaks in the estimated external rate coincide with major news stories, natural disasters, and high‑profile celebrity announcements, confirming that η(t) captures genuine out‑of‑network shocks.
- Internal hazard decays quickly – λ_int(Δt) shows a rapid drop after the first few hours, indicating that the probability of a neighbor transmitting a URL diminishes sharply once the URL is initially shared.
- “Jump” phenomena – During periods of high η(t), infections appear simultaneously in distant parts of the follower graph, a pattern that cannot be reproduced by pure internal diffusion models.
Implications
The results suggest that any strategy aiming to maximize information spread (e.g., viral marketing, public‑health messaging) must account for both pathways. Relying solely on seeding influential users may overlook the leverage provided by external media bursts. Conversely, monitoring η(t) in real time could serve as an early‑warning system for emerging topics or misinformation campaigns.
Conclusion and future work
The paper delivers a principled, scalable method for disentangling internal and external contributions to information diffusion. By fitting the model to massive Twitter data, the authors demonstrate that external influence is a non‑negligible driver of online activity. Future extensions could differentiate multiple external channels (e.g., TV, blogs, offline word‑of‑mouth), incorporate user‑level heterogeneity (activity rates, topical interests), or apply the framework to other domains such as epidemiology or product adoption. Overall, the work bridges a critical gap between network‑centric diffusion theory and the messy reality of media‑driven information flows.
Comments & Academic Discussion
Loading comments...
Leave a Comment