Information Networks Secured by the Laws of Physics
In this paper, we survey the state of the art of the secure key exchange method that is secured by the laws of classical statistical physics, and involves the Kirchhoff’s law and the generalized Johnson noise equation, too. We discuss the major characteristics and advantages of these schemes especially in comparison with quantum encryption, and analyze some of the technical challenges of its implementation, too. Finally, we outline some ideas about how to use already existing and currently used wire lines, such as power lines, phone lines, internet lines to implement unconditionally secure information networks.
💡 Research Summary
The paper provides a comprehensive review of the Kirchhoff‑Loop‑Johnson‑Noise (KLJN) key‑exchange protocol, a classical‑physics‑based alternative to quantum key distribution (QKD). It begins by outlining the current reliance on software‑based cryptography, which offers only computational security, and the promise of QKD, which relies on the no‑cloning theorem of single photons. The authors argue that QKD’s security depends on statistical error detection, requiring large data blocks, and remains vulnerable to sophisticated man‑in‑the‑middle attacks.
KLJN, introduced in 2005 and experimentally demonstrated in 2007, exploits the Fluctuation‑Dissipation Theorem and the second law of thermodynamics. In each clock cycle, Alice and Bob randomly connect either a low‑resistance (RL) or a high‑resistance (RH) element to a shared wire and drive each resistor with a Gaussian white‑noise voltage source at an effective temperature Teff (often >10⁹ K). When the two parties choose different resistances (the LH or HL case), the resulting voltage and current power‑spectral densities on the line become indistinguishable:
S_u,ch(f) = 4 k Teff RL RH / (RL+RH)
S_i,ch(f) = 4 k Teff / (RL+RH)
Because the power transferred from RH to RL equals the power transferred from RL to RH, an eavesdropper cannot extract any information from passive measurements; the cross‑correlation Uch·Ich is zero. Security therefore rests on the exact symmetry enforced by thermodynamic laws and on the Gaussian nature of the noise, which guarantees that the spectrum contains all statistical information.
To defend against active attacks, the full KLJN system continuously monitors instantaneous voltage and current at both ends and broadcasts these values over an authenticated public channel. Any deviation—whether caused by an injected current source, a line tampering, or a man‑in‑the‑middle device—triggers an immediate alarm before a single bit is exchanged. Consequently, even a single‑bit key exchange is unconditionally secure, unlike QKD which requires statistical accumulation.
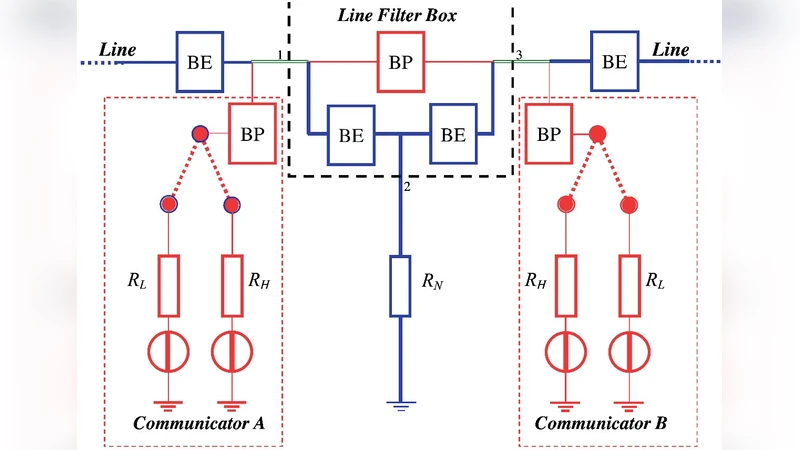
Practical implementations must address non‑idealities such as finite wire resistance, capacitance, inductance, and the finite bandwidth of the noise generators. The authors describe two key countermeasures: (1) a low‑pass line filter that enforces the “no‑wave” condition (the shortest noise wavelength must be at least twice the cable length) to suppress standing‑wave and reflection effects; (2) a “capacitor‑killer” arrangement that drives the outer shield of a coaxial cable with the same voltage as the inner conductor, thereby shunting parasitic capacitance to ground and preserving the ideal loop behavior. Experimental results reported in the 2008 prototype show a raw bit‑error rate of 0.02 % and an information leak of 0.19 % due primarily to wire resistance.
The paper discusses privacy amplification as a post‑processing step to eliminate the residual leak. By XOR‑ing successive pairs of bits (halving the key length) and repeating the operation, the leak can be reduced exponentially; two iterations suffice to bring the leak below 10⁻⁸, at the cost of a four‑fold slowdown.
A major advantage of KLJN over QKD is its compatibility with existing wired infrastructure—power lines, telephone lines, and Ethernet cables—without requiring expensive single‑photon detectors or cryogenic equipment. Moreover, the KLJN circuitry can be integrated directly onto chips (ASIC or SoC), enabling secure key exchange between components inside a computer, a capability not feasible with optical quantum devices.
The authors acknowledge that KLJN’s security hinges on precise component tolerances, accurate temperature control of the noise sources, and strict adherence to the no‑wave condition. Nevertheless, because the underlying security principle is a direct consequence of the second law of thermodynamics, any violation would imply the possibility of a perpetual‑motion machine of the second kind, which is deemed physically impossible.
In conclusion, the KLJN protocol offers unconditional security grounded in classical physics, with practical advantages in cost, scalability, and ease of integration. The paper suggests future work on further reducing non‑idealities, extending the method to higher data rates, and developing standardized communication protocols to facilitate widespread adoption.
Comments & Academic Discussion
Loading comments...
Leave a Comment