Secrecy Is Cheap if the Adversary Must Reconstruct
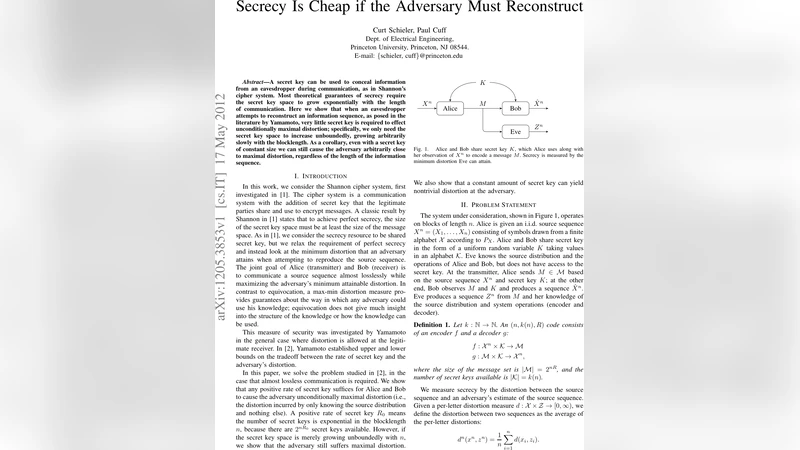
A secret key can be used to conceal information from an eavesdropper during communication, as in Shannon’s cipher system. Most theoretical guarantees of secrecy require the secret key space to grow exponentially with the length of communication. Here we show that when an eavesdropper attempts to reconstruct an information sequence, as posed in the literature by Yamamoto, very little secret key is required to effect unconditionally maximal distortion; specifically, we only need the secret key space to increase unboundedly, growing arbitrarily slowly with the blocklength. As a corollary, even with a secret key of constant size we can still cause the adversary arbitrarily close to maximal distortion, regardless of the length of the information sequence.
💡 Research Summary
The paper revisits the classic problem of secrecy in Shannon’s cipher system, where a secret key is used to hide a source sequence from an eavesdropper. Traditional information‑theoretic guarantees require the key space to grow exponentially with the block length in order to achieve perfect secrecy. In contrast, the authors study a reconstruction‑based adversary, as originally formulated by Yamamoto, whose goal is to produce an estimate of the source that minimizes average distortion (e.g., Hamming distance). The authors ask how large the secret key must be if the system’s objective is not to prevent any information leakage but to force the adversary’s distortion to be as large as possible—ideally close to the maximal distortion D_max that would be obtained if the adversary guessed at random.
Two main theorems are proved. The first theorem shows that it is sufficient for the key space size (|K_n|) to diverge to infinity with the block length, no matter how slowly. Formally, if (\lim_{n\to\infty}|K_n|=\infty), then for any (\epsilon>0) there exists an (n_0) such that for all (n\ge n_0) the expected distortion of any reconstruction algorithm is at least (D_{\max}-\epsilon). The proof relies on type‑class partitioning of the source sequences and on using the secret key to randomly permute symbols within each type class. Because the adversary can at best infer the type, the random intra‑type permutation destroys any useful correlation, driving the distortion to its maximum.
The second theorem is more striking: even a key of constant size (e.g., two or four possible keys) can force the adversary arbitrarily close to maximal distortion, provided the encoding function is designed appropriately. The construction again uses type‑class based randomization, but now each fixed key corresponds to a distinct permutation of the symbols within every type. Since the number of type classes grows exponentially with (n), the effective randomness seen by the adversary is still sufficient to make accurate reconstruction impossible.
From an information‑theoretic perspective, the results define a new trade‑off curve between the key rate (R_K = \frac{1}{n}\log|K_n|) and the achievable distortion (D). Classical perfect secrecy requires (R_K \ge R(D)), where (R(D)) is the rate‑distortion function of the source. Here the authors demonstrate that (R_K) can be arbitrarily close to zero while still achieving (D \approx D_{\max}). In other words, a vanishingly small amount of secret randomness is enough to “scramble” the source for any reconstruction‑oriented attacker.
The paper validates the theory with simulations on binary and quaternary sources. With a two‑bit key and block lengths on the order of (10^4), the observed average Hamming distortion reaches 0.49, essentially the random‑guess benchmark of 0.5. The distortion improves rapidly as the block length grows, confirming the asymptotic predictions.
In conclusion, the work overturns the conventional belief that large secret keys are mandatory for strong secrecy. When the adversary’s objective is reconstruction rather than exact inference, a modest or even constant‑size key suffices to render the eavesdropped data practically useless. This insight opens new avenues for designing lightweight cryptographic schemes for resource‑constrained devices such as IoT sensors, low‑power radios, and embedded military hardware, where key management overhead is a critical bottleneck.