LWE-based Identification Schemes
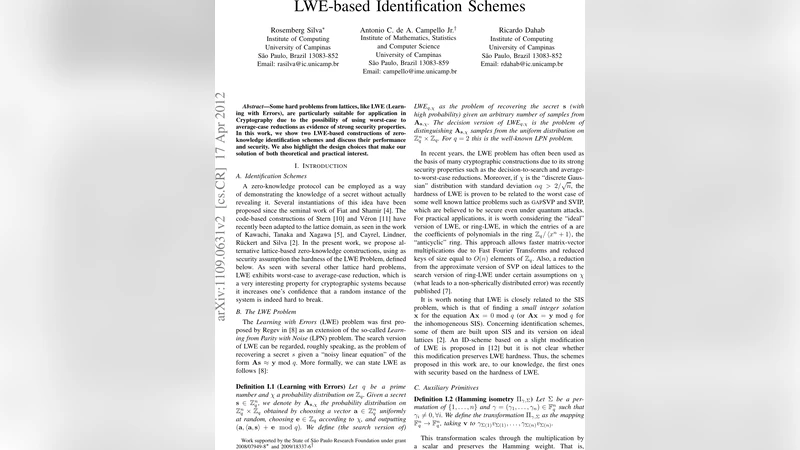
Some hard problems from lattices, like LWE (Learning with Errors), are particularly suitable for application in Cryptography due to the possibility of using worst-case to average-case reductions as evidence of strong security properties. In this work, we show two LWE-based constructions of zero-knowledge identification schemes and discuss their performance and security. We also highlight the design choices that make our solution of both theoretical and practical interest.
💡 Research Summary
The paper presents two novel zero‑knowledge identification (ZKI) protocols whose security is rooted in the hardness of the Learning with Errors (LWE) problem, a cornerstone of lattice‑based cryptography. After a brief motivation, the authors recall the definition of LWE, its search and decision variants, and the worst‑case to average‑case reductions that link LWE to classic lattice problems such as SVP and SIVP, thereby providing quantum‑resistant security guarantees.
The first construction is a three‑round protocol with a soundness error of 2/3. The key generation algorithm samples a random matrix A∈ℤ_q^{n×m}, a secret vector s∈ℤ_q^m, and an error vector e∈ℤ_q^n drawn from a prescribed distribution χ. The public key consists of (A, b=As+e, p=wt(e)), while the secret key is (s, e). During identification, the prover picks a random mask u, a non‑zero scaling vector γ, and a permutation Σ of the coordinates. Three commitments are computed: c₁ = com(Π_{γ,Σ}), c₂ = com(Π_{γ,Σ}(A(u+s))) and c₃ = com(Π_{γ,Σ}(Au+b)). The verifier challenges the prover with a random value ch∈{1,2,3}. Depending on ch, the prover opens the appropriate pair of commitments together with the necessary auxiliary data (e.g., u+s, Π_{γ,Σ}(e)). Completeness follows directly from the knowledge of (s,e). Soundness is proved by a standard “puzzle‑ballot” argument: if a cheating prover can answer two different challenges for the same commitment triple with probability exceeding 2/3+ε, then either a collision in the commitment scheme is found or the secret (s,e) can be recovered, contradicting LWE hardness. Zero‑knowledge is established via a simulator that predicts the verifier’s challenge, constructs commitments accordingly (sometimes using dummy values), and rewinds the verifier when the predicted challenge does not match. Because the commitment scheme is statistically hiding, the simulated transcript is indistinguishable from a real execution.
The second construction adapts a previously known identification scheme with soundness error 1/2 to the LWE setting and further optimizes it using ring‑LWE. The key generation algorithm now also computes a matrix A⊥ satisfying A·A⊥=0 and a vector y=A⊥e. The public key becomes (A, A⊥, y, b, p). The prover again selects a random vector u, a scaling vector γ, and a permutation Σ, and forms two commitments: c₁ = com(γ·Σ·A⊥·u) and c₂ = com(Π_{γ,Σ}(u)·Π_{γ,Σ}(e)). The verifier sends a random scalar α; the prover replies with β = Π_{γ,Σ}(u+αe). After receiving a binary challenge ch∈{1,2}, the prover opens the corresponding commitment (c₁ or c₂) together with the relevant auxiliary data. Completeness, soundness (error (q+1)/(2q)≈1/2), and zero‑knowledge are proved analogously to the first scheme, with the crucial observation that revealing Π_{γ,Σ}(e) in one challenge and Π_{γ,Σ}(u) in the other allows extraction of e if a cheating prover can answer both challenges for the same commitment pair.
Both protocols benefit from the use of the weight‑preserving transformation Π_{γ,Σ}, which enables the verifier to check the Hamming weight of the error vector without learning its content, and from a statistically hiding commitment scheme that provides collision resistance. To improve practical performance, the authors suggest instantiating the schemes over the ring ℤ_q
Comments & Academic Discussion
Loading comments...
Leave a Comment