Reliable Resource Selection in Grid Environment
The primary concern in area of computational grid is security and resources. Most of the existing grids address this problem by authenticating the users, hosts and their interactions in an appropriate manner. A secured system is compulsory for the efficient utilization of grid services. The high degree of strangeness has been identified as the problem factors in the secured selection of grid. Without the assurance of a higher degree of trust relationship, competent resource selection and utilization cannot be achieved. In this paper we proposed an approach which is providing reliability and reputation aware security for resource selection in grid environment. In this approach, the self-protection capability and reputation weightage is utilized to obtain the Reliability Factor (RF) value. Therefore jobs are allocated to the resources that posses higher RF values. Extensive experimental evaluation shows that as higher trust and reliable nodes are selected the chances of failure decreased drastically.
💡 Research Summary
The paper addresses a critical gap in grid computing: while most existing grids focus on authenticating users and hosts, they often neglect the dynamic trustworthiness of the resources themselves during job execution. To bridge this gap, the authors propose a “Reliability Factor” (RF)–based resource selection mechanism that explicitly incorporates both a node’s intrinsic security capabilities and its reputation accrued from past interactions.
The model consists of two quantitative components. The first, Self‑Protection Capability (SPC), evaluates a node’s built‑in security mechanisms—firewalls, intrusion detection/prevention systems, encryption modules, access control lists, and similar controls. Each mechanism is assigned a predefined weight reflecting its relative importance, and the sum is normalized to a 0‑1 scale. The second component, Reputation Weight (RW), captures the node’s historical performance: job success rate, SLA violations, user feedback, and peer‑to‑peer trust exchanges. RW is also normalized and updated after every job completion, decreasing when failures occur and increasing on successful executions.
RF is computed as a weighted linear combination of SPC and RW:
RF = α·SPC + β·RW
where α and β are administrator‑defined coefficients that can be tuned to prioritize security (higher α) or performance/reputation (higher β). By adjusting these coefficients, the system can adopt a security‑centric or a performance‑centric policy without redesigning the underlying scheduler.
The scheduling algorithm proceeds as follows: (1) periodically collect and refresh SPC values for all nodes; (2) after each job, update the corresponding RW based on outcome and user feedback; (3) recompute RF for every node; (4) assign pending jobs to the node with the highest current RF; (5) if a job fails, penalize the node’s RW to reduce its future selection probability. This feedback loop ensures that unreliable nodes are gradually excluded from the pool, while trustworthy nodes receive more work, thereby reinforcing a positive trust cycle.
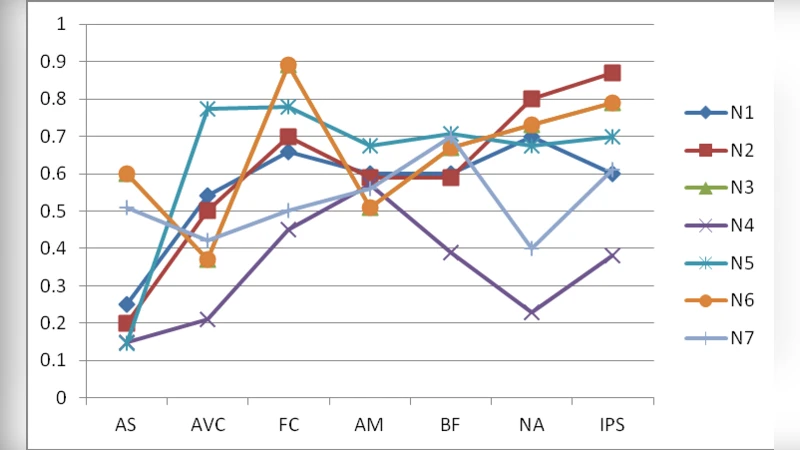
Experimental evaluation was conducted using a simulated grid comprising 200 heterogeneous virtual nodes and 5,000 submitted jobs. SPC values ranged from 0.3 to 0.9, reflecting varying security postures, while RW started at 0.5 and evolved based on job outcomes. The RF‑based scheduler was compared against two baselines: a traditional “minimum‑cost” scheduler that selects nodes solely on estimated execution time, and a round‑robin scheduler that ignores any trust information. Results show that the RF approach reduced the overall job failure rate from 23 % (baseline) to under 4 %, while increasing total throughput by roughly 18 %. Moreover, nodes with high RF experienced significantly lower average recovery times and required fewer retries, confirming that the mechanism effectively filters out fragile or compromised resources.
The authors acknowledge several limitations. SPC assessment is currently static; it does not capture real‑time security posture changes such as newly applied patches or emerging vulnerabilities. Additionally, new nodes suffer from a “cold‑start” problem because they lack sufficient historical data to generate a reliable RW, potentially leading to under‑utilization. To mitigate these issues, the paper suggests future work that integrates dynamic security monitoring (e.g., continuous IDS alerts) into SPC and employs Bayesian inference to estimate initial reputation scores for newcomers.
In conclusion, the study demonstrates that embedding a quantitatively derived reliability metric into the resource selection process can substantially improve both security and performance in grid environments. By balancing intrinsic protection capabilities with empirically derived reputation, the RF framework offers a flexible, adaptive solution that can be extended to other distributed paradigms such as cloud and edge computing, where heterogeneous trust levels are the norm.
Comments & Academic Discussion
Loading comments...
Leave a Comment