Generalized Degrees of Freedom of the Symmetric Gaussian $K$ User Interference Channel
We characterize the generalized degrees of freedom of the $K$ user symmetric Gaussian interference channel where all desired links have the same signal-to-noise ratio (SNR) and all undesired links carrying interference have the same interference-to-n…
Authors: Syed A. Jafar, Sriram Vishwanath
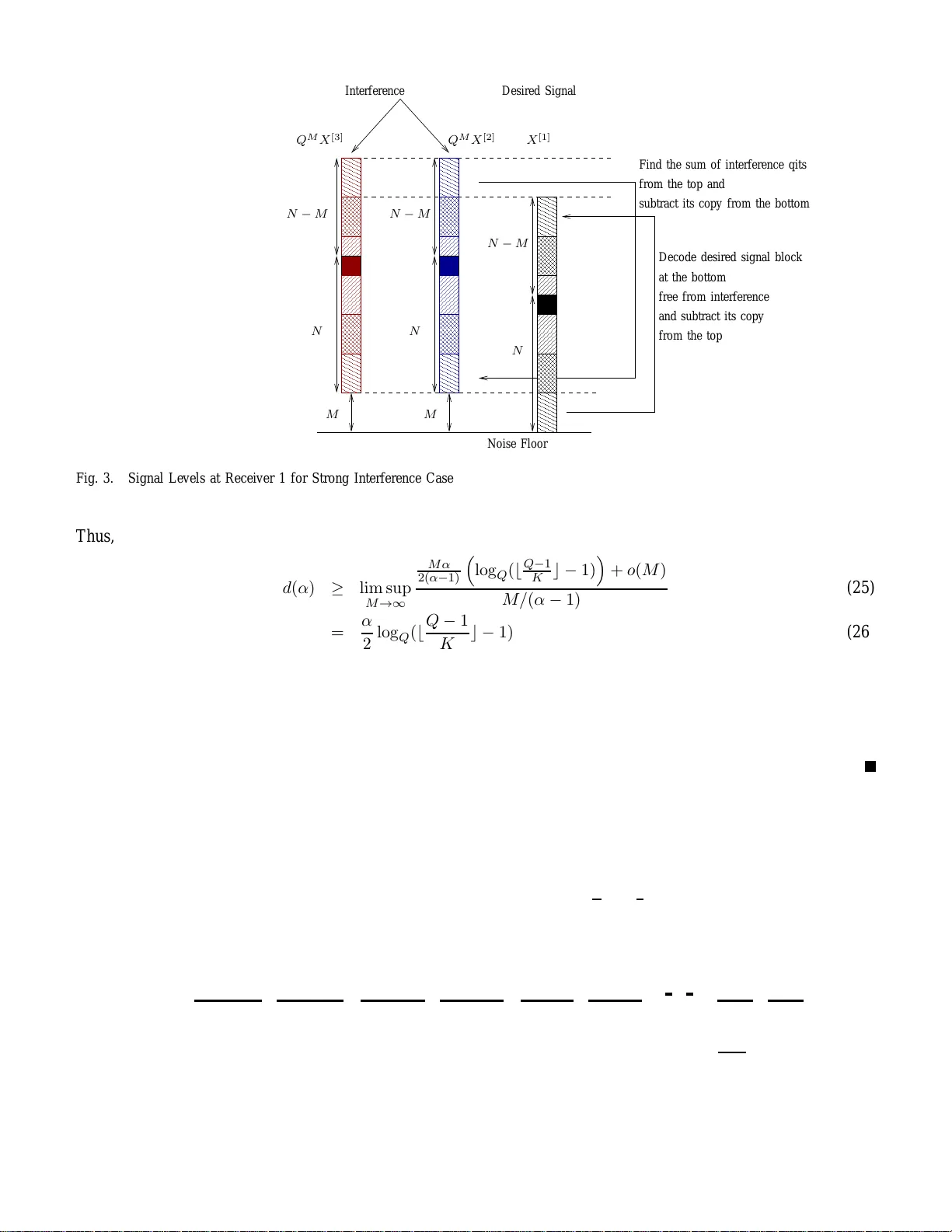
1 Generaliz ed De grees of Freedom of the Symmetric Gaussian K User Interference Ch annel Syed A. Jafar Electrical Engineering and Computer Science Univ ersity of California Irvine, Irvine, California, 92697, USA Email: syed@uci.edu Sriram V ishwanath Department of Electrical Engineering Univ ersity of T exas Austin Austin, T exas, USA Email: sriram@ece.utexas.edu Abstract W e ch aracterize the generalized degrees of freedo m of the K user symme tric Gaussian interference channel where all desired lin ks hav e the same signal-to -noise ratio (SNR) and all undesired links carr ying interference hav e the same interferen ce-to-no ise ratio, INR = SNR α . W e find that th e numb er of gener alized degrees of fr eedom per user, d ( α ) , does no t depend on the n umber of user s, so that th e charac terization is id entical to the 2 user interferen ce ch annel with the excep tion of a singularity a t α = 1 w here d (1) = 1 K . Th e ach ie vable sch emes u se multilevel coding with a nested lattice structure that opens the possibility that the sum of interferin g signals can b e decoded at a receiver even thoug h the message s carried by the inter fering signa ls are not dec odable. 2 I . I N T R O D U C T I O N The capa city of t he two us er Gaussian interference c hannel has recently been characterized upto an acc uracy of one bit per channel us e [1]. A closely related notion, also introduc ed in [1], is that of the generalized degrees of freed om. The generalized degrees o f freedom provide a clear mapping of various interference mana gement approach es to the SNR and INR regimes where they are optimal. For designing wireless networks, the natural question is how the n ew insights provided in [1] generalize to communica tion sc enarios with more than 2 users. Unfortunately , for interference networks with more than 2 use rs, even the con ventiona l degrees of freedom are not known in ma ny cases , e.g. whe n ch annel co ef ficients take a rbitrary but c onstant values. Degrees of freedom are known when channel coefficients are time-v arying or frequency selective and in some cases if the nodes are equipped with multiple antennas [2], [3]. The key insight from the degree of freed om charac terizations is the possibility of interference alignmen t in wireless networks by c oding ac ross the d imension (time, frequ ency , sp ace) along whic h the ch annel coefficients vary . For cha nnels with single an tenna nodes and constant co efficients (i.e., cha nnels that do not vary in time, frequ ency o r space dimensions), deterministic chane l mode ls proposed in [4] identify a new dimension - the sign al level along which the relativity o f a lignment can b e exploited to achieve interferenc e alignment [5], [6]. The use of deterministic ch annel mode ls ha s led to a pproximate ca pacity cha racterizations for the many-to-one and one-to-many Gaussian interference chan nels [5]. Deterministic chann el mode ls are also us ed in [6] to cha racterize the con ventional degrees of freedom for some special instanc es of Gaussian interference channe ls with constant channe l coef fi cients. Ho wever , in the richer context of generalized degrees of freedom, there a re no known characterizations for more than 2 u sers. Thu s, it is n ot clea r if interference regimes e legantly identified by [1] g eneralize to interference cha nnels with more than 2 u sers. In this work, our goal is to advance the generalized degrees o f freed om perspective to K user s ymmetric Gaussian interferen ce channe ls with cons tant channe l coe f ficients. W e start with the cha nnel model. I I . T H E S Y M M E T R I C G AU S S I A N I N T E R F E R E N C E C H A N N E L W e con sider the K user interference network desc ribed b y the input-output equations: Y [ k ] ( t ) = X [ k ] ( t ) + r INR SNR K X j =1 ,j 6 = k X [ j ] ( t ) + Z [ k ] ( t ) where at discrete time index t , Y [ k ] ( t ) and Z [ k ] ( t ) are the channe l output and add iti ve white Gauss ian noise (A WGN), respectively , at the k th receiv er and X [ j ] ( t ) is the c hannel input symbol at the j th transmitter , ∀ j, k ∈ K , { 1 , 2 , · · · , K } . All symb ols are real a nd the cha nnel c oefficients are fixed. The time index t is sup pressed henceforth for compa ct no tation. The A WGN is normalized to have ze ro mean and unit variance a nd the input power co nstraint is gi ven b y E h ( X [ k ] ) 2 i ≤ SNR , ∀ k ∈ K . The interference-to-noise-ratio (INR) is defin ed through the parameter α as: log( INR ) log( SNR ) = α (1) ⇒ INR = SNR α (2) Thus, as in [1], the ch annel is parameterized by α . W e de fine the generalized degrees o f freedom per user as: d ( α ) = 1 K lim su p SNR →∞ C Σ ( SNR , α ) 1 2 log( SNR ) (3) 3 d ( α ) 2 3 1 2 2 1 K 1 2 2 3 1 α → 1 Fig. 1. Generalized degre es of freedom for the K user symmetric Gaussian interference channel where C Σ ( SNR , α ) is the s um -capacity of the K us er interference network defined above. Note that we use lim sup to ensure that d ( α ) is always define d, with the understan ding that lim sup an d lim are the same if the ordinary limit exists. Finally , the half in the denominator is becaus e we a re dealing with real signals only . I I I . G E N E R A L I Z E D D E G R E E S O F F R E E D O M ( G D O F ) The gen eralized degrees of freed om for the K user interference cha nnel d escribed above, are p resented in the follo wing theorem. Theorem 3.1: d ( α ) ≤ 1 − α, 0 ≤ α ≤ 1 2 (noisy interference) α, 1 2 ≤ α ≤ 2 3 (weak interference) 1 − α 2 , 2 3 ≤ α < 1 (moderately weak interference) 1 K , α = 1 α 2 , 1 < α ≤ 2 (strong interference) 1 , α ≥ 2 (very strong interference) (4) Remark 1: Note that, with the exception of α = 1 the generalized degrees o f freed om per user do not depe nd on the number of users, so that the GDOF cha racterization is identical to that obtained in [1] for the 2 user s ymmetric Gaussian interference chan nel. Also note that the GDOF c haracterization shows a singu larity at α = 1 when the number of users K > 2 . A. Proof of Outerb ound For the case α = 1 , all receiv ers see statistically equi valent s ignals, which implies that all mes sages c an be decode d by all r eceivers and the sum capa city is the mu ltiple access ca pacity from the K trans mitters to, say , receiv er 1. Mathematically , C Σ ( SNR , 1) = 1 2 log(1 + K SNR ) which implies that d (1) = 1 K . Note that achiev ab ility of 1 /K d egrees of freedo m per user is tri vial. For α 6 = 1 the outerbound is straightforward as well. Eliminating a ll but two us ers, say users 1 and 2, the generalized degrees of freedom characte rization for the remaining two users is giv en by the result of [1] wh ich is the same as the outerbound above. Adding b ack other use rs does not help the se two users’ rates, so the result of [1 ] becomes an o uterbound on the d egrees o f freedom ach ie ved b y users 1 a nd 2 in the K us er interference chan nel. The sa me argument applies for any subs et o f two users. Combining thes e outerbo unds p roduces the outerbound of Theorem 3.1. Note that the o uterbound is tight for K = 2 , as estab lished in [1]. 4 Next we e stablish tight innerbou nds for ea ch regime. For this purpos e we break the result of The orem 3.1 into several lemmas, each of which is covered in a separate section. I V . A C H I E V A B I L I T Y O F G E N E R A L I Z E D D E G R E E S O F F R E E D O M A. Preliminary Se tup In this paper , all the achiev a ble scheme s for the ge neralized degrees of freedom are o btained by first finding the optimal sc heme for the de terministic chan nel model and then translating it to the Ga ussian channe l, in a similar manner as [6]. T o av o id repetition, we state the common aspe cts of the ach iev able schemes before addres sing the indi vidual scen arios. For a gi ven α 6 = 1 , consider the seque nce o f SNR values (indexed by M ) suc h that: SNR = Q 2 M | α − 1 | (5) where Q ≫ K is a large but fixed positiv e integer value a nd M is a positi ve integer whose value grows to infi nity producing a sequen ce of SNR values that approach infin ity as well. Using ( 5), we can re write the input-output equation (1) as: Y [ k ] = X [ k ] + Q sgn ( α − 1) M K X j =1 ,j 6 = k X [ j ] + Z [ k ] where sgn ( x ) = 1 if x > 0 and − 1 if x < 0 . T o co mpute lowerbounds on the gen eralized degree s of freedo m we will expres s both the symmetric rate R sym , i.e. a rate achieved simultane ously by each user , an d the SNR as functions of M , Q , α . W e use log Q ( · ) for both rate and SNR. Thus , d ( α ) = 1 K lim su p SNR →∞ C Σ ( SNR , α ) 1 2 log( SNR ) ≥ lim sup M →∞ R sym ( M , Q, α ) M / | α − 1 | (6) where we use d (5) to ma ke the substitution 1 2 log Q ( SNR ) = M / | α − 1 | . W e will oc casiona lly represent pos itive real signals in base- Q no tation using Q − ary digits 0 , 1 , 2 , · · · , Q − 1 , which we denote as “qits”. T o avoi d confusion we will mark the Q -ary repres entation as [ · ] Q . For example, when we write: A = [ · · · A 3 A 2 A 1 A 0 .A − 1 A − 2 A − 3 · · · ] Q then it is implied that A i are integers with values betwe en 0 a nd Q − 1 , o r the qits in the Q-ary repres entation of the real number A . Equiv alently , A = ∞ X i = −∞ A i Q i , A i ∈ { 0 , 1 , · · · , Q − 1 } 1) T ran smit Scheme: W e impose some structure on the Q − a ry represen tation of the transmit s ignal X [ k ] , which is expressed as: X [ k ] = h X [ k ] N − 1 · · · X [ k ] 3 X [ k ] 2 X [ k ] 1 X [ k ] 0 .X [ k ] − 1 X [ k ] − 2 X [ k ] − 3 · · · X [ k ] − L i Q (7) i.e., the mos t sign ificant (non-ze ro) qit corresp onds to the coefficient of Q N − 1 and the leas t sign ificant (non- zero) qit correspo nds to the coef fi cient of Q − L for some N , L . The s ame s tructure applies to all u sers, k ∈ K . Additional structure may also be impose d on the transmitted signals for diff erent interference regimes cons idered in subseq uent sections. In eac h case, the values of the q its are restricted to e nsure that (in the a bsenc e of noise) addition 5 of interfering signals does n ot produ ce carry ov ers. For example this could be ac complished by the restriction that X [ k ] i ∈ { 0 , 1 , · · · , ⌊ Q − 1 K ⌋} . Note that 0 ≤ X [ k ] ≤ Q N . Thus, the transmitted power E ( X [ k ] ) 2 < Q 2 N . The power cons traint (1) is satisfied if Q 2 N ≤ S N R . This is guaranteed by the choice : N = M | α − 1 | (8) Each qit is code d in time ind ependen tly of other qits in the manne r o f multi-le vel cod ing. Th us, over T c hannel uses, the cod ew ord for qit i from transmitter k is X [ k ] i (1) , X [ k ] i (2) , · · · , X [ k ] i ( T ) . 2) R eceive S cheme: Each rec ei ver k ∈ K takes the mag nitude o f the received signal, reduc es it modulo Q m , discards the value be lo w the decimal point an d expres ses the res ult in Q − ary repres entation a s: Y [ k ] = j | Y [ k ] | mo d Q m k = m − 1 X i =0 Y [ k ] i Q i , Y [ k ] i ∈ { 0 , 1 , · · · , Q − 1 } (9) Here, m = max( N , N + sgn ( α − 1) M ) is the maximum number of qits see n at the rec eiv er above the dec imal place (noise flo or) that are contributed by the transmitted signals. The k th receiv er views the i th qit a s a s eparate channe l with input X [ k ] i and output Y [ k ] i . Let us also defi ne a noise-free version of the receiv ed signal, ˆ Y [ k ] = X [ k ] + Q sgn ( α − 1) M K X j =1 ,j 6 = k X [ j ] which is esse ntially the rec eiv ed signal in the deterministic channe l model o f [4]. Let P e i be the p robability that the i th qit of ˆ Y [ k ] is not the s ame as the i th qit of Y [ k ] , 0 ≤ i ≤ m − 1 . Th e key idea is that due to the structure impose d on the transmitted q its and the finite variance of noise, this probab ility P e i is a motonica lly de creasing function of i and ap proaches zero as i beco mes lar ge . Thus, as M , N and i become lar ge, the limiting rate achieved with no ise-free cha nnel output ˆ Y [ k ] i is iden tical to the ra te a chieved wi th ou tput Y [ k ] i by cod ing across c hannel use s over each qit sepa rately . W e provide a detailed exposition of this argument only for the very strong interference cas e. The argument a pplies to a ll a chiev able sche mes in this paper in a straightforward fashion. For other a pplications of the same argument see [6]. W e start with the very strong interference regime. B. V ery Str ong Interference The follo wing theorem es tablishes the generalized degrees of freedom for the very strong interference case. Lemma 4.1: For the K user symmetric Gaussian channel defined in Section II, the generalized degrees of freedom d ( α ) = 1 for α ≥ 2 . Pr oo f: The transmitted symbo l o f user j is constructed as follo ws: X [ j ] = h X [ j ] N − 1 X [ j ] N − 2 X [ j ] N − 3 · · · X [ j ] 1 X [ j ] 0 . 0 i Q (10) The same con struction is used for all transmitters. W e restrict the values of the qits as: X [ j ] i ∈ { 1 , 2 , · · · , Q − 2 } , ∀ j ∈ { 1 , 2 , · · · , K } , i ∈ { 0 , 1 , · · · , N − 1 } (11) Note t hat the qit v alue s 0 and Q − 1 are n ot us ed. While not neces sary , this is done to simplify the argument that the impact of the noise is limited a nd it does not propagate indefin itely through carry overs into higher signal lev els. The v alue of N is cho sen to satisfy the power co nstraint N = M | α − 1 | (12) 6 Desired Signal Q M X [3] Q M X [2] Interfer ence Decoded Interfere nce-Free N N N M M Noise Floor X [1] Fig. 2. Signal Lev els at Recei ver 1 for V ery Strong Interference Case as in (8). Since α ≥ 2 note that this implies that M ≥ N . The key idea is that multiplication b y Q M shifts the dec imal point in the Q -ary representation ( X [ j ] ) Q by M places to the right. T hus, an interfering signal reaches a receiv er shifted up by M qits. Since M ≥ N all t he interference is easily e liminated by a s imple modulo Q N operation at the receiv er . T o acc ount for noise, let u s ev a luate the proba bility P e i for 0 ≤ i ≤ N . Note that: 1 − P e i = Prob ( ˆ Y [ k ] i = Y [ k ] i ) ≥ Prob Z [ k ] ≤ Q i − 1 (13) becaus e regardles s of wh ether it is p ositi ve or negati ve, any additive n oise with magnitude n o more than Q i − 1 does not af fect the coefficient o f Q i . Thus, P e i is monotonica lly dec reasing in i and goes to 0 as i becomes large. Now consider the chan nel with inp ut X [ k ] i and no ise-free ou tput ˆ Y [ k ] i as defined above. Becau se of the shift o f the interfering qits out of the d esired space we have: ˆ Y [ k ] i = X [ k ] i , 0 ≤ i ≤ N − 1 . (14) Thus, this chann el ha s channel capac ity ˆ C i = log Q ( Q − 2) qits per chann el us e. The no isy c hannel has inp ut X [ k ] i and ou tput Y [ k ] i . Howe ver becau se P e i approach es zero a s i → ∞ the capac ity of the noisy chan nel ca n be expressed as: lim i ≤ N − 1 ,i → ∞ C i = ˆ C i (15) ⇒ N − 1 X i =0 C i = N log Q ( Q − 2) + o ( N ) (16) Thus, we express the symmetric achiev able rate for the proposed scheme as: R sym = M α − 1 log Q ( Q − 2) + o ( M ) Substituting into (6) we have d ( α ) ≥ lim sup M → ∞ M α − 1 log Q ( Q − 2) + o ( M ) M / ( α − 1) (17) = log Q ( Q − 2) (18) 7 Observing that Q can be ch osen to be arbitrarily large and comparing with the outerboun d for α ≥ 2 , we have d ( α ) = 1 , ∀ α ≥ 2 . (19) C. Str ong Interference The follo wing theorem es tablishes the generalized degrees of freedom for the strong interference ca se. Lemma 4.2: For the K user symmetric Gaussian channel, d ( α ) = α/ 2 for 1 < α ≤ 2 . Pr oo f: The transmitted symbo l o f user j is constructed as follo ws: X [ j ] = X [ j ] 2 N − M − 1 · · · X [ j ] N | {z } N − M “copy” qits X [ j ] N − 1 · · · X [ j ] 0 | {z } N q its . 0 Q (20) The same con struction is used for all transmitters. W e restrict the values of the qits as: X [ k ] i ∈ { 1 , 2 , · · · , ⌊ Q − 1 K ⌋ − 1 } (21) This ensures that no carryovers are produce d by the ad dition of the interfering sign als in the absenc e of noise and that P e i approach es ze ro as i becomes lar g e. Further , we require that: X [ j ] 2 N − M − i = X [ j ] i − 1 (22) for i ∈ { 1 , 2 , · · · , N − M } . Thus the most significant N − M q its are simply cop ies of the least significa nt N − M qits in oppos ite order . W ith this c onstruction the transmit power ca n be expressed in the form of the following outerbound: E h ( X [ j ] ) 2 i ≤ Q 2 N − M 2 (23) The power c onstraint is satisfied if 2 N − M ≤ M α − 1 . So we choos e: N = M α 2( α − 1) ≥ M (24) The decoding takes place stepwise in block s of size M qits, as i llustrated in F igure 3. I n each s tep the least significant block of M qits of de sired signal is de coded free from interference a nd its copy present in the the most significant M -qit bloc k of the desired signal, is subtracted out. At the same time, the mos t significant M -qit b lock of the sum of the interferers’ sign als is use d to cance l ou t the least signific ant M -qit bloc k of the sum of interfering qits. Thus, each step produces a new M -qit block of desired signal free from interference and a ne w M -qit block of interfering signals free from the desired signa l. Th e proced ure is continued until a ll N qit s of d esired signa l are decode d. Note that the interferenc e qits a re not d ecoded , b ut ra ther the su m of the interference co dew ord symbo ls and nois e is subtracted from its co py . Thus, the cance llation o f interference introduces noise in the desired sign al. Ho wever , the proba bility P e i once ag ain ap proaches zero a s the block size M increa ses and the same arguments (as explained in the very strong interference case ) apply for characterizing the rate of de sired signa l within o ( M ) for e ach M -qit block. Using this ac hiev ab le scheme , the sy mmetric rate achieved simultane ously by all users is: R sym = M α 2( α − 1) log Q ( ⌊ Q − 1 K ⌋ − 1 + o ( M ) 8 00 00 11 11 00 00 11 11 000 000 111 111 00 00 00 11 11 11 00 00 00 00 11 11 11 11 00 00 00 00 00 00 11 11 11 11 11 11 000 000 000 111 111 111 000 000 000 000 111 111 111 111 000 000 000 000 000 000 111 111 111 111 111 111 00 00 00 00 00 00 11 11 11 11 11 11 00 00 00 00 11 11 11 11 000 000 000 000 000 000 111 111 111 111 111 111 000 000 000 000 111 111 111 111 00 00 00 00 00 00 00 11 11 11 11 11 11 11 00 00 00 11 11 11 00 00 00 00 00 00 11 11 11 11 11 11 00 00 00 00 11 11 11 11 00 00 00 11 11 11 N N − M N − M N − M Noise Floor M M N subtract its copy from the bottom Find the sum of interferenc e qits from the top and from the top at the bottom free from interferenc e and subtrac t its copy Decode desire d signal block Q M X [2] Interfer ence Desired Signal X [1] Q M X [3] N Fig. 3. Signal Lev els at Recei ver 1 for Strong Interference Case Thus, d ( α ) ≥ lim sup M → ∞ M α 2( α − 1) log Q ( ⌊ Q − 1 K ⌋ − 1) + o ( M ) M / ( α − 1) (25) = α 2 log Q ( ⌊ Q − 1 K ⌋ − 1) (26) Observing tha t Q can be chosen to be arbitrarily lar ge wh ile K is fixed, and comparing with the outerboun d, we have d ( α ) = α/ 2 , ∀ α ∈ (1 , 2] . (27) D. Mode rately W eak Interference The following the orem establishes the ge neralized degrees of freedom for the moderately we ak interferenc e case . Lemma 4.3: For the K user symmetric Gaussian channel, d ( α ) = 1 − α 2 for 2 3 ≤ α < 1 . Pr oo f: The transmitted symbo l o f user j is constructed as follo ws: X [ j ] = X [ j ] 2 N +3 M − 1 · · · X [ j ] N +3 M | {z } N q its X [ j ] 3 M + N − 1 · · · X [ j ] 2 M + N | {z } M q its X [ j ] 2 M + N − 1 · · · X [ j ] 2 M | {z } N “ copy” qits 0 · · · 0 | {z } M z eros X [ j ] M − 1 · · · X [ j ] 0 | {z } M qits . 0 Q The sa me cons truction is used for all transmitters. All transmitted qits lie betwee n 1 an d ⌊ Q − 1 K ⌋ − 1 . Further , we require that X [ j ] 2 N +3 M − i = X [ j ] 2 M + i − 1 (28) for i ∈ { 1 , 2 , · · · , N } . Thus, the most signfica nt N qits are copied in re verse order . 9 000 000 000 000 111 111 111 111 000 000 000 111 111 111 000 000 000 000 000 000 000 111 111 111 111 111 111 111 000 000 111 111 00 00 00 11 11 11 00 00 00 11 11 11 00 00 00 11 11 11 00 00 00 11 11 11 00 00 00 00 00 00 11 11 11 11 11 11 000 000 000 111 111 111 000 000 000 111 111 111 000 000 000 111 111 111 000 000 000 000 000 000 111 111 111 111 111 111 000 000 000 111 111 111 000 000 111 111 M N M N Decode Desired Signa l Qits Free from Interfere nce and Subtract its Copy Noise Floor M N M N Q − M X [3] Q − M X [2] Desired S ignal Interfer ence X [1] Decoded Free of Interference of interfe rence qits Subtract the sum M M M N N M Fig. 4. Signal Lev els at Recei ver 1 for Moderately W eak Interference Case W ith this c onstruction the transmit power ca n be expressed in the form of the following outerbound: E h ( X [ j ] ) 2 i ≤ Q 2 N +3 M 2 (29) The power c onstraint is satisfied if 2 N + 3 M ≤ M 1 − α , so we choos e: N = M (3 α − 2) 2(1 − α ) (30) The key idea for t he ach ie vable s cheme is illustrated in Figu re 4 . Decoding takes place in blocks of M qits. Starting from the noise floo r , the M least s ignificant qits o f the interference appe ar below the noise floor a nd are discarded. The M leas t s ignificant qits of the de sired signal coinc ide with the zero pa dding q its of the interferers so they can b e d ecoded without interference as well. F rom this point on the decod ing p roceeds in similar steps. Each step, the most significan t M qits of the des ired s ignal do not see any interference and are decode d interference -free. These qits are subtracted from the copy that appears at the least s ignificant end . Similarly , the sum of the M least significant q its o f the interference is comp uted free from d esired signa l and this s um is subtrac ted from the most significant interferenc e qits to produ ce an interference free des ired signal block . The step is repeated until all the desired qits are dec oded. The symmetric rate a chiev ed with this s cheme is: R sym = (2 M + N ) log Q ⌊ Q − 1 K ⌋ − 1 + o ( M ) = 2 M + M (3 α − 2) 2(1 − α ) log Q ⌊ Q − 1 K ⌋ − 1 + o ( M ) = M (1 − α/ 2) (1 − α ) log Q ⌊ Q − 1 K ⌋ − 1 + o ( M ) 10 Thus, d ( α ) ≥ lim sup M → ∞ M (1 − α/ 2) (1 − α ) log Q ⌊ Q − 1 K ⌋ − 1 + o ( M ) M / ( α − 1) (31) = 1 − α 2 log Q ⌊ Q − 1 K ⌋ − 1 (32) Observing tha t Q can be chosen to be arbitrarily lar ge wh ile K is fixed, and comparing with the outerboun d, we have d ( α ) = 1 − α/ 2 , ∀ α ∈ [ 2 3 , 1) . (33) E. W eak Interference The follo wing theorem es tablishes the generalized degrees of freedom for the weak interference cas e. Lemma 4.4: For the K user symmetric Gaussian channel, d ( α ) = α for 1 2 ≤ α ≤ 2 3 . Pr oo f: The transmitted symbo l o f user j is constructed as follo ws: X [ j ] = X [ j ] 2 M + N − 1 · · · X [ j ] 2 M | {z } N q its 0 · · · 0 | {z } M z eros X [ j ] M − 1 · · · X [ j ] 0 | {z } M q its . 0 Q The same con struction is used for all transmitters. All transmitted qits lie be tween 1 and Q − 2 . W ith this c onstruction the transmit power ca n be expressed in the form of the following outerbound: E h ( X [ j ] ) 2 i ≤ Q N +2 M 2 (34) The power c onstraint is satisfied if we ch oose N + 2 M ≤ M (1 − α ) , so we ch oose N = M (2 α − 1) 1 − α ≤ M (35) The scheme is explaine d Fig. 5. The cha nnel pushes the interference le vel do wn by M qits. Thus, the least significant M qits of the desired signa l a lign with the z ero padding qits of interference and can be decode d free from interference. Sinc e, N ≤ M , the most s ignificant N qits are also free from interference. Thu s, the symmetric rate achieved simultaneous ly by all us ers is expressed as: R sym = M (2 α − 1) (1 − α ) + M log Q ( Q − 2) + o ( M ) Thus, d ( α ) ≥ lim sup M → ∞ M α 1 − α log Q ( Q − 2) + o ( M ) M / ( α − 1) (36) = α log Q ( Q − 2) (37) Observing tha t Q can be chosen to be arbitrarily lar ge wh ile K is fixed, and comparing with the outerboun d, we have d ( α ) = α, ∀ α ∈ [ 1 2 , 2 3 ] . ( 38) 11 Noise Floor M N M M N M M N M Decoded Free of Interference Decoded Free of Interference X [1] Desired Signal Interfer ence Q − M X [2] Q − M X [3] Fig. 5. Signal Lev els at Recei ver 1 for W eak Interference Case F . Noisy Interference The following theorem establishes the gen eralized degrees of free dom for the nois y interference case ( 0 ≤ α ≤ 1 / 2 ). Lemma 4.5: For the K user symme tric Gaussian channe l, d ( α ) = 1 − α for 0 ≤ α ≤ 1 2 . An optimal sc heme in the degrees of freedom sense is to use Ga ussian c odeboo ks and treat interference a s noise. Pr oo f: W ith Ga ussian codeboo ks and with interference treated a s noise, the symmetric ach iev able rate is : R sym = 1 2 log 1 + SNR 1 + ( K − 1) INR = 1 2 log 1 + SNR 1 + ( K − 1) SNR α = 1 2 (1 − α ) log ( SNR ) + o (log( SNR )) (39) and therefore as SNR → ∞ , the innerbound on degrees of freedom d ( α ) ≥ 1 − α which coinc ides with the outerbound for α ≤ 1 / 2 . V . C O N C L U S I O N W e fou nd the gen eralized d egrees of freedom per us er for the K user symmetric Gau ssian interference chann el to be indep endent of the number o f use rs with the exception of a singularity at α = 1 . The sy mmetric channe l mod el itself imposes a special structure on t he channe l coefficients which plays an i mportant role in the achiev a ble scheme s. This work reaffirms the importance of the deterministic c hannel mod el of [4] a s well as the importance of structured coding for interferenc e networks with more than 2 users. For future work, many impo rtant directions remain open. For example, extension s to a symmetric c hannels, complex s ignals and cha nnel co ef ficients, time varying and frequency s electiv e channe ls with rando m co efficients, an d multiple antennas are all interesting d irections. Another promising d irection is to use the generalized degrees of freedo m as a guide to pursue ca pacity cha racterizations within a cons tant nu mber of bits in the mann er of [1] for more than 2 use rs. 12 R E F E R E N C E S [1] R. Et kin, D. Tse, and H. W ang, “Gaussian interference channel capacity to within one bit, ” submitted to IEEE T ransac tions on Information Theory , F eb . 2007. [2] V . Cadambe and S. Jafar , “Interference alignment and t he degrees of f reedom of the k user interference channel, ” in Submitted to t he IEEE T ransactions on Information T heory . Pr eprint available t hr ough http://newport.eecs.uci.edu/ syed , July 2007. [3] V . Cadambe and S. Jafar , “Degrees of freedom of wireless X networks, ” in Submitted t o IE EE T ransaction s on Information Theory . Pr eprint available on arxiv:0711.28 24 and thr ough http://newport.eecs.uci.edu/ syed , Nov 2007. [4] A. S . A vestimehr , S . Diggavi, and D. Tse, “ A deterministic approach to wireless relay networks, ” Oct 2007, arXiv:cs.IT/0710.3777. [5] G. B resler , A. Parekh, and D . Tse, “ Approximate capacity of the many-to-one interference channel, ” S ep. 2007. Allerton C onference. [6] V . Cadambe, S. Jafar , and S. Shamai, “Interference alignment on the deterministic channel and application to gaussian networks, ” arxi v:0711.2547 .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment