Capacity of Wireless Networks within o(log(SNR)) - the Impact of Relays, Feedback, Cooperation and Full-Duplex Operation
Recent work has characterized the sum capacity of time-varying/frequency-selective wireless interference networks and $X$ networks within $o(\log({SNR}))$, i.e., with an accuracy approaching 100% at high SNR (signal to noise power ratio). In this pap…
Authors: Viveck R. Cadambe, Syed A. Jafar
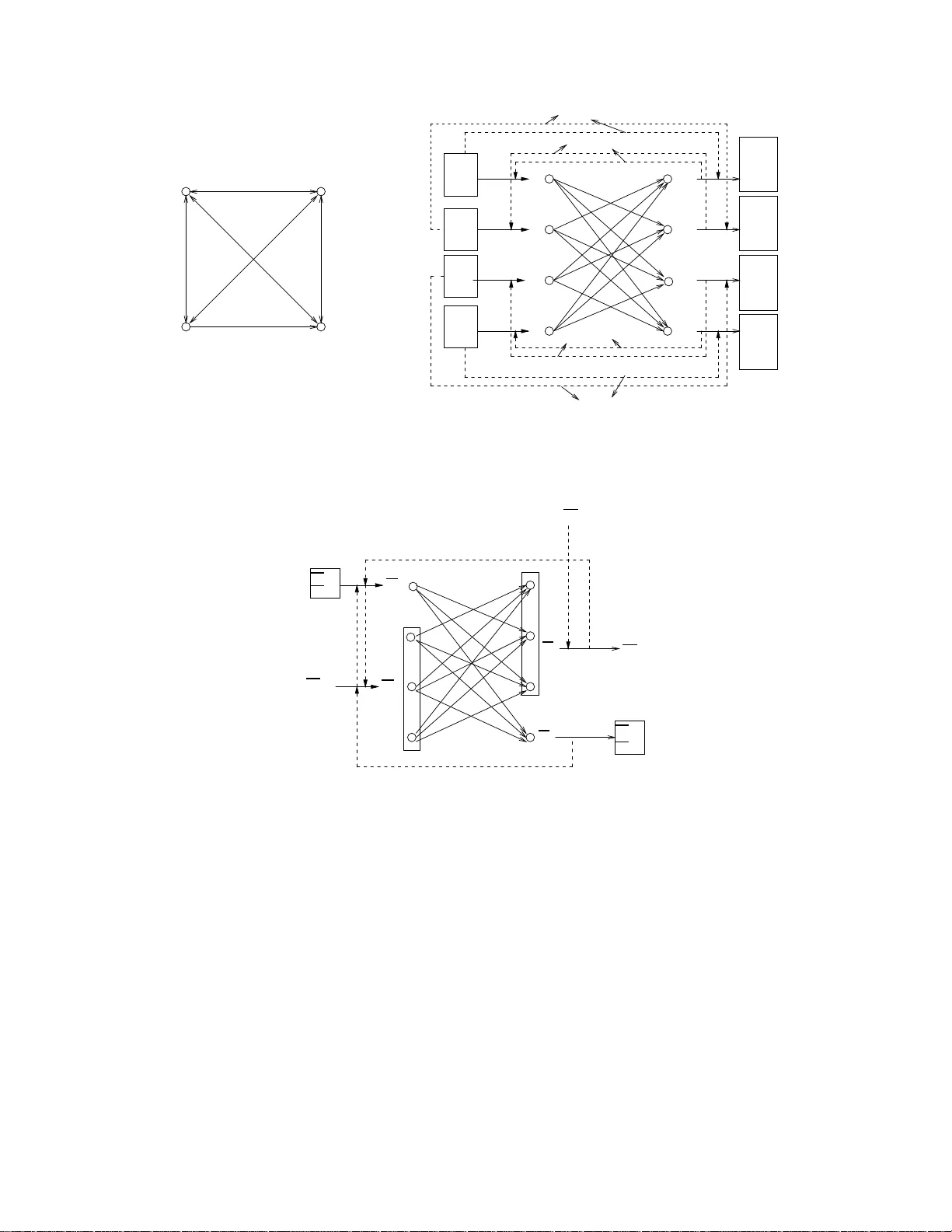
Capacity of W ireless Netw orks within o (log ( SNR )) - the Impact of Relays, Feedback, Cooperation and Full-Duple x Operati on V i veck R. Cadamb e, Syed A. J afar Electrical Engineering and Com puter Science University of California Irv ine, Irvine, Califor nia, 9269 7, USA Email: vcad ambe@uci.edu, syed@uci.edu Abstract Recent w ork has chara cterized the sum capac ity of time-v arying/frequenc y-selective wireless interference netwo rks and X networks within o (log( SNR )) , i.e., wi th an accuracy approaching 100% at high SNR (signal to noise power ratio). In this paper , we seek similar capacity characterizations for wireless networks with relays, feedback, full duplex operation, and transmitter/recei ver cooperation through noisy channels. F irst, we consider a network with S source nodes, R relay node s and D destination nodes with random time-v arying/frequenc y-selective chann el coef ficients and global channel kno wl edge at all nodes. W e allow full-duple x operation at all nodes, as well as causal noise-free feedback of all recei ved signals t o all source and relay nodes. T he sum capacity of this network is characterized as S D S + D − 1 log( SNR ) + o (log( S NR )) . The implication of t he result i s that the capacity benefits of relays, causal feedback, transmitter/receive r cooperation through physical channels and full duplex operation become a negligible fraction of the network capacity at high SNR. Some exceptions to t his result are also pointed out in the paper . S econd , we consider a netw ork with K full duplex nodes with an independe nt message from ev ery node to e very other node in the network. W e fi nd t hat the sum capacity of this network is bounde d belo w by K ( K − 1) 2 K − 2 + o (log( SNR )) and bounded above by K ( K − 1) 2 K − 3 + o (log( SNR )) . I . I N T RO D U C T I O N The recent su rge of interest in app roximate capac ity ch aracterizations of wireless networks has lead to sub stantial progr ess on several lon g standing o pen pro blems. The capac ity of the 2 user interference ch annel and th e capacity of certain r elay networks hav e been char acterized with in a constant nu mber of bits [1] , [ 2]. Th e sum capacity o f the K -user time-varying/fr equency-selecti ve interfe rence c hannel (see Fig ure 1) was characterized in [3] as C ( SNR ) = K 2 log( SNR ) + o (log( SNR )) (1) where SNR represen ts the signal to noise ratio (eq ui valently , the to tal tran smit power of all nodes when the local n oise p o wer at each re cei ver is norm alized to unity ). If the sum c apacity of a network is char acterized as C ( SNR ) = d log( SNR ) + o (log ( SNR )) , then we say that the network has d degree s of freedo m (also known a s multiplexing ga in or capacity pre- log). Since, by d efinition, at high SNR the o (log( SNR )) term is a vanishing fraction of log ( SNR ) , th e accuracy of such a cap acity character ization ap proaches 100% as the SNR ap proaches infinity . The resu lt th at the K user interfer ence n etwork has K/ 2 d egrees of freedom is in teresting becau se it shows th at at high SNR, every user in an interfe rence network is simultan eously ab le to reliably com municate at a ra te close to half of his individual cap acity in the absence o f all interferers. The result reveals th e fallacy o f the conv entional “cake-cutting” view of orthog onal m edium access because, essentially , it implies th at everyone g ets ”half the cake” (whe re the cake rep resents th e rate ac hie vable by the user in the absen ce of interference ). T he achiev able sch eme of [3 ] is based on the idea of interferen ce alignment (see [4] and referen ces therein ). The key to interferen ce a lignment is the realization that the alignmen t o f sig nal dimen sions (in time, frequ ency , space and codes) is relati ve to th e o bserver ( receiv er). Since every receiver sees a different p icture, sign als may be constructed to ca st overlapping sh adows at th e receivers wh ere they constitute interf erence while they re main distinguishable at the receivers where they are desired . X n etworks are a g eneralization of interference networks. Un like an interference n etwork where each tra nsmitter has a message f or only its correspond ing receiver , in an X n etwork every tra nsmitter ha s an independ ent message for e very receiver . Reference [5] stu died the S × D X network (Figure 1), i.e., a n etwork with S transmitter s, D receivers and S D independ ent messages - o ne message for each transmitter-receiver pair . Using an in terference alignment based achiev a ble schem e, [5] ch aracterized th e sum cap acity of the S × D X network as C ( SNR ) = S D S + D − 1 log( SNR ) + o (log( SNR )) . (2) In other words, the S × D X network has S D S + D − 1 degrees of freedo m. For S = D = K it is interesting to n ote that th e degrees of freed om benefits of X networks over interferen ce networks diminish a s the number o f users, K , in creases. The results of [5] an d [3] show that inter ference alignment suffices to ach ie ve the cap acity of wireless interference and X network s at high SNR. Howe ver , many intere sting po ssibilities are not explored by these scenarios. In general, a wireless network can hav e relay nodes. The nod es may be capab le of full-d uplex o peration so th at they can all transmit and r ecei ve simu ltaneously and th us co-op erate to imp rove rates of co mmunication. Furthermo re, ev en when perfe ct glo bal channel knowledge is already assumed, n oise-free (causal) feedb ack of received signals ma y have sig nificant ben efits in a wireless network . For K -user inter ference network s, degrees of f reedom with relay s and tr ansmitter/receiver co operation thr ough noisy ch annels have been explo red in [ 14] and an outerbo und of K / 2 is obta ined. Since th e results of [3] sh o w that K / 2 degrees o f freedo m can be ac hie ved e ven without relay s and c W 2 c W K c W 1 X 2 X 1 W 2 W 1 c W 2 ,S X 1 X 2 X S Y D . . . Y 2 Y 1 Y K Y 1 Y 2 . . . . . . . . . . . . . . . c W D, 1 c W D,S c W 2 , 1 c W 1 , 1 c W 1 ,S W 1 ,S W D,S W 1 , 2 W N , 2 W 1 , 1 W D, 1 W K C ( SNR ) = K 2 log( SNR ) + o (log( SNR )) C ( SNR ) = S D S + D − 1 log( SNR ) + o (log( SNR )) The K us er interference channel X K The S × D X channel Fig. 1. Interference and X channe ls Recei ved symbol T ransmitted symbol Y 1 X 1 X 2 Y 2 (b) (a) Fig. 2. K user full duplex net work wit h (a) K = 2 , (b) K = 4 cooper ation, the co nclusion is that relays and transmitter/receiver coop eration cann ot increase the degrees of freedom of interference networks. I n this p aper , we seek a generalization of the results of [14 ] f rom in terference n etworks to X network s. In particular, we seek a d egrees of freedom chara cterization for fully conn ected wireless X ne tworks with r elays, feedback , transmitter (receiv er) co operation and fu ll duplex operation . I I . S U M M A RY O F R E S U LT S There are two main re sults in the paper . Th e first result applies to networks wh ose sour ce and destination nodes are disjoint. In other words, if a node is a source node for a message, then it cannot be the destination node for any message in the network (and vice versa). In Section III we intr oduce the S × R × D network - a fully connected network with S source nod es, R relay nodes and D destination nod es with full d uplex operatio n a ssumed at all nodes. Since node s are full duplex, th ey c an all transmit and receive and thus network allows co -operation between all nod es throu gh noisy chan nels. Also included is per fect causal fe edback channel of all r ecei ved signals to all source and relay n odes. W e show that this network has S D S + D − 1 degrees of freedo m mean ing that the capacity o f the n etwork can be expr essed as C ( SNR ) = S D S + D − 1 log( SNR ) + o (log ( SNR )) Note that th e ab ove ap proximation is identical to the approximation in e quation ( 2). Achiev ability th us fo llo ws trivially from the interferen ce alignment based achiev ab le scheme of [ 5] between the S source node s and D destination nod es. The ou terbound is shown in Th eorem 1 in Section IV. The seco nd result of this paper is for the K user full du plex network c onsidered in Section V. There is an indepen dent message from ev ery n ode to ea ch of the o ther K − 1 nod es in the network so that there are a total o f K ( K − 1) messages. All nod es in the network functio n simultan eously as source, relay an d destination nodes. In Theorem 2, the su m capacity o f this network is bou nded as C ( SNR ) ≥ K ( K − 1) 2 K − 2 log( SNR ) + o (log ( SNR )) C ( SNR ) ≤ K ( K − 1) 2 K − 3 log( SNR ) + o (log ( SNR )) The ach ie vable scheme is based on interf erence align ment. Next, we discuss the implication s o f these r esults. A. Can Re lays, F eedback, Co-operation and Full Dup le x Operation Impr ove th e De gr ees of F reedom of a W ir eless Network ? An interesting im plication of the results is th at the capacity imp rovements d ue to relay s, fe edback, full dup lex operation and noisy co- operation become a negligib le fraction of the n etwork capacity as SNR increases. Pu t differently , these factors (r elays e tc.) do not improve the d egrees of f reedom o f wir eless networks. Thus, in most wireless network s, the sear ch fo r capacity improvemen ts o f the or der o f log( SNR ) ends in inter ference alig nment. While the r esult is obtain ed fo r a broad class of n etworks, it is limited by the u nderlying assump tions. For example, we assume that each node is equipped with only a single antenna, the chann el coefficients are time-v arying/f requency selecti ve and drawn rand omly fro m a continu ous distribution whose support is bounded belo w by a non-zero constant (i.e., the n etwork is fully co nnected), the cha nnel kn o wledge is global and per fect. Some examples of scen arios where d egrees of f reedom can b e improved are listed below . 1) Relays can improve the degrees of fr eedom if a n etwork is not f ully conn ected. 2) Co-operation can incr ease the d egrees of freedom if th e cost of co -operation is n ot acco unted for (e.g ., in genie-aide d cognitive radio networks). 3) Full duplex o peration can increase the degrees of f reedom if the same node can be the source for one message and the destination fo r another m essage. 4) Feedback can improve the degrees of freedo m if it is provided to a d estination node, in wh ich case it helps the d ecoder b y providing , in e f fect, extra antenn as tha t can be u sed to n ull out inter ference. In the remaind er of this section, we discuss th e above statements in detail. B. Relays It is easy to co nstruct exam ples of networks that are not fully connected where the presence of relays increases the d egrees o f free dom. A simp le example would be a 3 node network where the ch annel coefficient between the source and d estination is zero, so that a non-ze ro capa city can only be achieved thr ough the relay nod e. W e fu rther illustrate the sign ificance o f this re sult b y placin g it into persp ecti ve with some existing resu lts on relay n etworks. The ben efits o f relay s on the degrees of freedom of network s have been considered in [6] , [7] . [6] considered a single K -antenn a transmitting node commu nicating with a K -antenna receiving node through multiple o rthogona l hops o f distributed parallel relays. U sing a simp le amplify and forward scheme they showed that the capac ity of R dist ribut ed relays K distribut ed destina tions K distribut ed sources Fig. 3. The paralle l relay channel this network scales as K log( SNR ) + o (log ( SNR )) . Reference [7] considered a 2 h op p arallel relay n etwork with K distributed sou rces and K distributed de stinations, with the sources and destinations separated by a layer of R distributed relay s (Figure 3). Like the inter ference network, th e p arallel relay network has K messages, one from each transmitter to its uniqu e correspon ding receiver . I n th is setting, the r esults of [7] ind icate th at if the relays are full- duplex and the num ber o f r elays R → ∞ , the sum cap acity approach es K log( SNR ) so that the network has K d egrees of freedo m using an achiev ab le scheme based on amplify an d f orward. Referen ce [5 ] shows a similar result fo r parallel relay networks by viewing each hop as an X network . Th e achiev able scheme of [5] u ses decode- and-forward and full-d uplex relays to achieve K R ( K + R − 1) degrees of freedom ov er this n etwork. Observe that by increasing R , we ca n get arbitrarily close to K d egrees o f freed om. Thu s, if we a ssume th at source nodes are not dir ectly c onnected to the d estination nodes, as in Figure 3, then the re sults of [5] and [7] p rovide interesting examples where full-du plex relay s increase the degrees of freed om from K / 2 to K . Ho wev er , the key d if ference between the p arallel relay n etworks in these cases an d th e m odel in this paper is that the former n etwork is not fully connected since the links from the so urce n odes to destination n odes are absent. I f the parallel relay network of Figure 3 is fu lly connected , i.e., if ther e are no n-zero channel co ef ficients from all source nod es to all the destinatio n nodes, surprisingly , the resulting network has only K / 2 degrees o f free dom (by th e result of Theorem 1) . In oth er words, the presence of direct links from source to destination nodes in this network reduces the degrees of fr eedom of the n etwork by a factor of h alf. By artificially imposing the h alf-duplex constraint on th e relays, the relay-aid ed schemes of [5] (and [7]) can provide o nly an alternate m eans of ach ie v ing K / 2 degrees of f reedom throug h a 2-phase op eration. C. Cognitive Coop eration The b enefits of co gniti ve cooperation in commun ication networks is cu rrently an active area of resear ch [8], [9], [10], [11]. A comm only studied model of cognitive interference networks assumes that certain nodes ac quire ap riori knowledge of certain messages w ith th e aid of a g enie. Fro m th e degre es of freedom pe rspecti ve, cog niti ve message sharing can indeed incr ease th e number o f degrees of freedom of a network. For example, it is easily seen that in the 2 user interf erence n etwork with 2 messages (see Figu re 4 ), sharing two messages achiev es the full cooperation multiplexing gain of 2 [4]. Oth er examples wher e cognitive message sharing increases the n umber of degrees of Y 2 W 1 W 2 X 1 X 2 ˆ W 2 Y 1 ˆ W 1 Y 2 W 2 Genie W 1 W 2 Genie W 1 X 1 X 2 ˆ W 2 Y 1 ˆ W 1 W 2 Genie Genie W 1 Fig. 4. T wo user inter ference chann el with cog niti ve message sharin g, eac h with 2 de grees of freedom freedom o f interferen ce and X networks can be found in [ 10], [4] , [12 ]. It is importa nt to n ote that the models of [4], [10], [12], do not account for the cost of co operation. F or example, in Figure 4 (a), the cost of transmitter 2 acquir ing message W 1 and transmitter 1 acquir ing W 2 are not factor ed in to the problem f ormulation. Referen ces [13 ], [14] consider the 2 user interfer ence chann el wh ere the cost-f ree genie is r eplaced by ph ysical channels thr ough which the tr ansmitters and/or r ecei vers can shar e inform ation and find that the network has only 1 degree of freedom. Thus, the degrees of freedo m benefits of genie- aided coop eration disappear when the cost o f co operation is taken in to account. Theo rem 1 in this p aper extends this in sight to the general class of X n etworks. D. Full Duplex Operation The fact that full d uplex op eration impr oves the number of degree s of free dom can b e easily o bserved in the 2 way 2 user point-to- point chan nel which h as 2 degrees of freedo m (Figu re 2). In a more ge neral network with K nodes an d a message from every node to every other n ode (Figur e 2), full dup lex operation can be shown to increase the numb er of degrees of freed om. For examp le, conside r a n etwork with K nodes. In Theore m 2, we show that the cap acity of this K node fu ll duplex network satisfies K ( K − 1) 2 K − 2 log( SNR ) + o (log ( SNR )) ≤ C f ull − duplex ( SNR ) ≤ K ( K − 1) 2 K − 3 log( SNR ) + o (log ( SNR )) If we assum e half du plex opera tion, then th e optimal arran gement is with K / 2 nodes beh a ving as transmitters and K / 2 n odes behaving as receivers to form a K / 2 u ser X network . This network h as K 2 4 K − 4 degrees of f reedom so tha t we can write C half − d uplex ( SNR ) = K 2 4 K − 4 log( SNR ) + o (log ( SNR )) Clearly full- duplex oper ation in creases th e degrees of freedom of a network with K nod es. Note that the S × R × D network of T heorem 1 includes full- duplex op eration in its m odel. The difference from the K u ser f ull du plex network of section V and the S × R × D network of Theor em 1 is that in the latter , n odes that ar e message sour ces ar e not d estination nodes. E. F eedback While we know that perf ect feedb ack does not increase the cap acity of a mem ory-less point- to-point channel, feedback has been shown to increase the capacity of the multiple access [17] , [18] and broadc ast [15] cha nnels. 1 2 3 ˆ W 2 , 1 W 3 , 2 ˆ W 1 , 3 W 1 , 3 W 2 , 1 ˆ W 3 , 2 Fig. 5. A network where feedback inc reases deg rees of freedom Howe ver, the issue addressed here is whether fee dback can increase the de gr ees of fr eedo m of a wireless network. W e show in Theorem 1 that even perfec t feedb ack to the source- nodes and relays does no t increase the degrees of freedom o f a fully co nnected network with S source nod es, D destination no des and R relays. W e can howe ver construct a scen ario where feed back impr oves the d egrees of freedom of a n etwork. T o see this consider a 3 nod e full duplex network with 3 messages as in Figur e 5. If there is n o feedbac k in this 3 node network, the numb er of degrees of free dom of this network is u pperbou nded by 2 - the d egrees of free dom of a 3 no de full- duplex network discu ssed in the previous subsection. Now , if we inc lude feedb ack in this n etwork as shown in Figure 5, we can show that 3 degrees of freedo m are achiev ab le, with each message achieving 1 degree o f freedom . T o see this, co nsider node 1 . Let th e channel g ain for the signal fr om nod e i to nod e j be eq ual to H j,i and Z j be the A WGN term at r ecei ver j . Th is rece i ved symbol at this node is equal to H 1 , 2 X 2 + H 1 , 3 X 3 + Z 1 . Also, the n ode obtains info rmation of H 2 , 3 X 3 + Z 2 throug h feed back from node 2 . Using the feedback , node 1 can zero -force the interferen ce from node 2 and thus obtain 1 degree of free dom for the message W 1 , 3 . Similarly the remaining two messages can each achieve 1 degree of freedo m so tha t 3 d egrees of freedo m are achiev a ble over the network. Thus, fe edback increases the degrees of f reedom of th is network. The reason feedback helped the network of Fig ure 5 is that it provide d a decoder with an extra antenn a which can be used to cancel interferen ce. Th erefore, fe edback can increase the degrees of freedom if it is provided to a decodin g node. I I I . S Y S T E M M O D E L F O R A N S × R × D N O D E X N E T W O R K Consider an S × R × D no de n etwork, i.e., a network with S + R + D no des where n odes 1 , 2 , · · · , S are sources, nodes S + 1 , S + 2 , · · · , S + R are r elays, and no des S + R + 1 , S + R + 2 , · · · , S + R + D are destination nod es (see Figu re 6). Follo wing the definition of an X network [5], for all j ∈ { 1 , 2 , · · · , S } and for all i ∈ { S + R + 1 , S + R + 2 , · · · , S + R + D } , there is an in dependent messag e W i,j to be c ommunicated f rom source n ode j to destination nod e i . Full d uplex operation is a ssumed so tha t all no des are cap able of tran smitting and rece i v ing simultaneously . The S distributed sou rces R relays D distributed destinatio ns Perfect Feedback Node 1 Node S + R + 1 Node S + R + D Node S Fig. 6. The S × R × D network input an d outpu t signals of the S × R × D no de network are related as: Y i ( n ) = S + R + D X j =1 H i,j ( n ) X j ( n ) + Z i ( n ) , i ∈ { 1 , 2 , · · · , S + R + D } , n ∈ N (3) where, at the n th discrete time slot, X j ( n ) is the symb ol transmitted by node j , Y i ( n ) is the symbol rece i ved by node i , H i,j ( n ) is the ch annel from nod e j to node i and Z i ( n ) is the zer o mean unit variance ad diti ve white Gaussian no ise (A WGN) at node i . W e use the following no tation, X n i , { X i (1) , X i (2) , · · · , X i ( n ) } (4) Similar n otation is used for ou tput signals and the ad diti ve no ise term s as well. The chann el co ef ficients H i,j ( n ) , ∀ i, j ∈ { 1 , 2 , · · · , S + D + R } ar e known ap riori 1 to all nod es. W e assume th e channel coefficients are time-varying/fr equency-selecti ve with values drawn randomly from a continuous distribution with suppo rt bound ed below by a non -zero constant. Thu s, all chann el coefficients take non-z ero values and the network is f ully-conne cted. Th e A WGN terms Z i ( n ) have unit variance an d are ind ependent identically distributed (i.i.d.) in time a nd across no des. Perfect (n oise-free) and causal feedback o f all received signals is av ailable to all sour ce and relay nodes, but no t to th e d estination nod es. For cod e words span ning N channel uses, the encod ing f unctions are as follows, X i ( n ) = f i,n W S + R +1 ,i , W S + R +2 ,i , · · · , W S + R + D, i , Y n − 1 1 , Y n − 1 2 , · · · , Y n − 1 S + R + D , i ∈ { 1 , 2 , · · · , S } f i,n Y n − 1 1 , Y n − 1 2 , · · · , Y n − 1 S + R + D , i ∈ { S + 1 , S + 2 , · · · , S + R } f i,n Y n − 1 i , i ∈ { S + R + 1 , · · · , S + R + D } 1 Thus, we also show that non-causa l channel kno wledge does not incre ase the degrees of freedom. for n = 1 , 2 , · · · , N . In other words, the signal transmitted from a source nodes at time n is co mpletely determined by a ll th e messages originating at that source no de and the re cei ved sign als of all the no des upto time n − 1 (causality cond ition). The signal transmitted by a destination nod e at time n can only dep end o n a ll the received signals at that nod e upto time n − 1 . This is because the destin ation nodes do not receive feedback of oth er node s’ received sig nals. The signal tran smitted from a relay node can only d epend on the r ecei ved signals of all the no des upto tim e n − 1 . The dec oding functio ns are a s follows, ˆ W i,j = g i,j Y N i , i ∈ { S + R + 1 , S + R + 2 , · · · , S + R + D } , j ∈ { 1 , 2 , · · · , S } Thus, a destination node can only use its own received signa l to decode all its desired messages. The pro bability of err or is the pro bability that there is at least one message W i,j that is not d ecoded corr ectly , i.e. ˆ W i,j 6 = W i,j for some ( i, j ) . The total power across all transmitters is assumed to be ρ per ch annel u se. W e den ote the size of th e message set by | W i,j ( ρ ) | . Let R i,j ( ρ ) = log | W i,j ( ρ ) | N denote the rate of the codeword encoding the me ssage W i,j , wh ere the codewords span N slots. A r ate-matrix [( R i,j ( ρ ))] is said to be achievable if messages W i,j can be encoded at rates R i,j ( ρ ) so th at the p robability of error can be made arb itrarily sma ll simultaneou sly for all messages by choo sing approp riately long N . Let C ( ρ ) repr esent th e cap acity region o f th e S × R × D nod e n etwork, i. e., it re presents the set of all ach ie vable rate-matrices [( R j i ( ρ ))] . The degrees of freedom region of the S × R × D n ode network is defined as D = ( [( d i,j )] ∈ R S D + : ∀ [( α i,j )] ∈ R S D + S + R + D X i = S + R +1 S X j =1 α i,j d i,j ≤ lim sup ρ →∞ sup [( R i,j ( ρ ))] ∈ C ( ρ ) S + R + D X i = S + R +1 S X j =1 ( α i,j R i,j ( ρ )) 1 log( ρ ) ) I V . D E G R E E S O F F R E E D O M O F T H E S × R × D N O D E X N E T W O R K Theorem 1 : Le t D out △ = [( d i,j )] : ∀ ( u, v ) ∈ { 1 , 2 · · · S } × { S + R + 1 , S + R + 2 , · · · , S + R + D } S + R + D X q = S + R +1 d q,u + S X p =1 d v, p − d v, u ≤ 1 Then D ⊆ D out where D represents the d egrees of freedom r egion of the S × R × D no de X n etwork. Furthermo re, the to tal n umber of d egrees of freedo m of the S × R × D network can be u pperbou nded as f ollo ws max [( d i,j )] ∈D S X j =1 S + R + D X i = S + R +1 d i,j ≤ S D S + D − 1 Equiv alently , th e su m capacity C ( ρ ) of this network can be b ounded as C ( ρ ) ≤ S D S + D − 1 log( ρ ) + o (log( ρ )) Pr oof: T o p rove the the orem, a ll we n eed to show is that for any ( p, q ) ∈ { 1 , 2 , . . . , S } × { S + R + 1 , S + R + 2 , . . . , S + R + D } S + R + D X i = S + R +1 d i,p + S X j =1 d q,j − d q,p ≤ 1 3 4 1 2 Feedback Feedback ˆ W 3 , 1 ˆ W 4 , 1 , ˆ W 4 , 2 W 3 , 1 , W 4 , 1 W 4 , 2 Fig. 7. 4 user X netw ork In othe r w ords, for all messages th at either originate at no de p o r are intended for no de q , the total nu mber of degrees of freedo m cannot be mo re than on e. For convenience, we w ill sho w the inequality for ( q , p ) = (1 , S + R + D ) . By sym metry , the inequality extend s to all desired values of p, q . W e therefor e intend to show that S + R + D X i = S + R +1 d i, 1 + S X j =1 d S + R + D, j − d S + R + D, 1 ≤ 1 T o sh o w this, we first eliminate all the messages that are not associated with either sour ce n ode 1 o r destination node S + R + D , i.e. , we set W i,j = φ, ( i − ( S + R + D )) ( j − 1) 6 = 0 . Since we are on ly seeking a n outerbo und on the r ates of a subset of m essages, it is im portant to note tha t eliminating a m essage can not hu rt the rates o f the remaining messages [4 ]. Now , we transfor m th e original S × R × D no de n etwork with single antenna nod es in to a 2 × 0 × 2 nod e network, i. e., a n X network with 2 source n odes, zero relay n odes and 2 d estination node s where one source an d one destination h a ve mu ltiple antenn as (see Fig ure 7) . This is do ne by allo wing f ull co operation between the S − 1 source nodes 2 , · · · , S and the R relay nodes S + 1 , S + 2 , · · · , S + R so that th ey effectiv ely b ecome o ne transmitter with S + R − 1 antennas. Similarly , destination nodes S + R + 1 , S + R + 2 , · · · , S + R + D − 1 are also allowed to perfec tly c ooperate so that they form one receiver with D − 1 an tennas. Ag ain, note that allowing the nodes to coop erate can not r educe the d egrees o f freedom r egion and therefor e does not co ntradict our o uterbound argument. W e represent the resulting 4 node X ne twork ( Figure 7) by the f ollo wing input- output equatio ns. Y i ( n ) = 4 X j =1 H i,j ( n ) X j ( n ) + Z i ( n ) , i ∈ { 1 , 2 , 3 , 4 } (5) where Y 1 ( n ) = Y 1 ( n ) Y 2 ( n ) = [ Y 2 ( n ) Y 3 ( n ) · · · Y S + R ( n )] T Y 3 ( n ) = [ Y S + R +1 ( n ) Y S + R +2 ( n ) · · · Y S + R + D − 1 ( n )] Y 4 ( n ) = Y S + R + D ( n ) Thus, n odes 2 and 3 act as mu ltiple antenna n odes with S + R − 1 and D − 1 an tennas respectively . X i ( n ) , Z i ( n ) are also defined in a correspond ing m anner fo r i ∈ { 1 , 2 , 3 , 4 } . Th e definition of the chan nel coe f ficients H i,j ( n ) is clear from equations (3) an d (5), and f rom Figures 6 and 7. Multiple m essages that have the same sourc e an d the sam e d estination are c ombined in th e 4 n ode X network as follows: W 3 , 1 = [ W S + R +1 , 1 W S + R +2 , 1 · · · W S + R + D − 1 , 1 ] (6) W 3 , 2 = φ (7) W 4 , 1 = W S + R + D, 1 (8) W 4 , 2 = [ W S + R + D, 2 W S + R + D, 3 · · · W S + R + D, S ] (9) Over this X network, the encod ing fun ctions are as f ollo ws X 1 ( n ) = f 1 ,n W 3 , 1 , W 4 , 1 , Y n − 1 1 , Y n − 1 2 , Y n − 1 3 , Y n − 1 4 (10) X 2 ( n ) = f 2 ,n W 4 , 2 , Y n − 1 1 , Y n − 1 2 , Y n − 1 3 , Y n − 1 4 (11) X 3 ( n ) = f 3 ,n Y n − 1 3 (12) X 4 ( n ) = f 4 ,n Y n − 1 4 (13) and the decoding f unctions are the following: ˆ W 3 , 1 = g 3 , 1 Y N 3 (14) ˆ W 4 , 1 = g 4 , 1 Y N 4 (15) ˆ W 4 , 2 = g 4 , 2 Y N 4 (16) The rates and the degrees of free dom region of this network are define d in a mann er similar to the S × R × D network. For this 4 nod e X network, it follows fro m Lem ma 1 (stated below) that: d 3 , 1 + d 4 , 1 + d 4 , 2 ≤ 1 where d i,j represents th e number o f degrees of f reedom corre sponding to message W i,j . Using equation ( 6)-(9), we can re-write the above ou terbound in terms of degre es of f reedom of th e S × R × D network as follows. S + R + D X i = S +1+ R d i, 1 + S X j =1 d S + R + D, j − d S + R + D, 1 ≤ 1 By sym metry , the above in equality implies that S + R + D X i = S +1+ R d i,p + S X j =1 d q,j − d q,p ≤ 1 The o uterboun d o n the degrees of freed om re gion D is th erefore shown. Summing all inequ alities of the above form over all ( p, q ) ∈ { 1 , 2 , . . . S } × { S + R + 1 . . . S + R + D } , the bou nd on th e to tal num ber of degrees of freedom ca n be obtain ed In the above p roof we used the following lemma. ˆ W 3 , 1 W 4 , 1 , W 4 , 2 Genie 4 1 2 Feedback Feedback ˆ W 4 , 1 , ˆ W 4 , 2 W 3 , 1 , W 4 , 1 U 4 ( n ) U 3 ( n ) U 1 ( n ) U 2 ( n ) W 4 , 2 Fig. 8. The outerboun d argument for the 4 use r X networ k - Lemma 1 Lemma 1: . In the 4 node X network describ ed by equ ations (5),(10)-(13), (14)-(1 6 ) and Figure 7 , the total number o f degrees of fre edom can be upper-bou nded by max D X d 3 , 1 + d 4 , 2 + d 4 , 3 ≤ 1 where D X represents th e degrees of f reedom region of this 4 node X chan nel Define U i ( n ) = H i, 1 ( n ) X 1 ( n ) + Z i ( n ) , i = 1 , 2 , 3 , 4 In or der to pr ove Lemma 1, we n eed the following result Lemma 2: In the 4 nod e X network of Figur e 7 and equations (5),( 10)-(13), ( 14)-(16), th e following thre e statements a re true. S 1 ( n ) : X n 1 ← W 3 , 1 , W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 S 2 ( n ) : X n 2 , X n 3 , X n 4 ← W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 S 3 ( n ) : Y n 1 , Y n 2 , Y n 3 , Y n 4 ← W 4 , 2 , U n 1 , , U n 2 , U n 3 , U n 4 where A ← B means that the value o f A is completely d etermined b y the knowledge of the value taken by B . A pr oof of the above lemma is plac ed in Appe ndix I. W e now procee d to a proo f of Lemma 1 A. Pr oo f o f Lemma 1 Let a genie provide the messages W 4 , 1 , W 4 , 2 and U 1 ( n ) , U 2 ( n ) , U 3 ( n ) , U ( 4 n ) to node 3 at channel use n ∈ N . Note that L emma 2 imp lies that the node can construct Y i ( n ) , i = 1 , 2 , 3 , 4 usin g this side informatio n from the genie. Also n ote tha t in the gen ie sup ported 4 no de X network in Figu re 8, node 3 is not explicitly shown to receive Y 3 ( n ) because it is already contained in th e info rmation available to node 3 . Next we find outerb ounds on the ra tes in the genie sup ported 4 no de X network. Using Fano’ s ineq uality , we can write N R 3 , 1 ( ρ ) ≤ I ( W 3 , 1 ; W 4 , 1 , W 4 , 2 , U N 1 , U N 2 , U N 3 , U N 4 ) + N ǫ N ≤ I ( W 3 , 1 ; U N 1 , U N 2 , U N 3 , U N 4 | W 4 , 1 , W 4 , 2 ) + N ǫ N ≤ H ( U N 1 , U N 2 , U N 3 , U N 4 | W 4 , 1 , W 4 , 2 ) | {z } T 1 − H ( U N 1 , U N 2 , U N 3 , U N 4 | W 3 , 1 , W 4 , 1 , W 4 , 2 ) | {z } T 2 + N ǫ N (17) Simplifying th e ter ms, T 2 = N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) , U 4 ( n ) | W 3 , 1 , W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 ) ( a ) ≥ N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) , U 4 ( n ) | W 3 , 1 , W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 , X 1 ( n )) ≥ N X n =1 H ( Z 1 ( n ) , Z 2 ( n ) , Z 3 ( n ) , Z 4 ( n )) ≥ N X n =1 M 1 + M 2 + M 3 + M 4 X i =1 H ( Z i ( n )) ≥ N ( M 1 + M 2 + M 3 + M 4 ) log (2 π e ) (18) where M i represents the numb er of antenn as at nod e i in the X network . Ineq uality (a) uses the fact that conditionin g on X 1 ( n ) reduces entropy . T 1 = H ( U N 1 , U N 2 , U N 3 , U N 4 | W 4 , 1 , W 4 , 2 ) = N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) , U 4 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 ) = N X n =1 H ( U 4 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 ) + N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 , U 4 ( n )) ( b ) = N X n =1 H ( U 4 ( n ) + 4 X j =2 H 4 ,j X j ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 ) + N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 , U 4 ( n )) ( c ) = N X n =1 H ( Y 4 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 , Y 4 ( n − 1 )) N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) | W 4 , 1 , W 4 , 2 , U n − 1 1 , U n − 1 2 , U n − 1 3 , U n − 1 4 , U 4 ( n )) ( d ) ≤ N X n =1 H ( Y 4 ( n ) | W 4 , 1 , W 4 , 2 , Y 4 ( n − 1 )) + N X n =1 H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) | U 4 ( n )) ≤ H ( Y N 4 | W 4 , 1 W 4 , 2 ) + N X n =1 3 X i =1 H ( U i ( n ) | U 4 ( n )) (19) Equality (b) uses statements S 1 ( n ) , S 2 ( n ) of Lemma 2. (c) uses S 3 ( n ) of Lemma 2. Inequality (d) uses the fact that co nditioning r educes entropy to boun d both terms of the summan d on the rig ht ha nd side. Now , w e can b ound the seco nd term in T 1 as follows H ( U i ( n ) | U 4 ( n )) = H ( H i, 1 ( n ) X 1 ( n ) + Z i ( n ) | H , 1 ( n ) X 1 ( n ) + Z S + R + D ( n )) ( e ) ≤ M i X j =1 H ( H [ j ] i, 1 X 1 ( n ) + Z [ j ] i ( n ) | H 4 , 1 ( n ) X 1 ( n ) + Z 4 ( n )) ( f ) ≤ M i X j =1 log 1 + | H [ j ] i, 1 | 2 ρ 1 1 + | H 4 , 1 | 2 ρ 1 ! + log (2 πe ) ! ≤ M i X j =1 log 1 + | H [ j ] i, 1 | 2 ρ 1 1 + | H 4 , 1 | 2 ρ 1 !! + N M i log(2 π e ) (20) where in (e), Z [ j ] i and H [ j ] i, 1 represent the noise and c hannel gain ter ms associated with the j th anten na at n ode i and M i represents th e n umber of antennas at no de i (Note th at M 1 = M 3 = 1 ). Inequality ( f ) above ho lds be cause of Lemma 1 in [13] . Note that ρ 1 represents the p o wer expended at transmitter 1 . Now , notice that the bo und of (20) implies tha t as long as H 4 , 1 > 0 , the term H U i ( n ) | U 4 ( n ) is upper-bou nded by a con stant for all values of input power ρ . Therefo re, using equation (20) and then combinin g (19), ( 18) and (1 7) we can write R 3 , 1 ( ρ ) ≤ 1 N H ( Y N 4 | W 4 , 1 , W 4 , 2 ) + O (1) (21) Now , u sing Fano’ s inequ ality to boun d rates o f messages intended for node 4 , we can write R 4 , 1 ( ρ ) + R 4 , 2 ( ρ ) ≤ 1 N I ( W 4 , 1 , W 4 , 2 ; Y N 4 ) + ǫ N = 1 N H ( Y N 4 ) − 1 N H ( Y N 4 | W 4 , 1 , W 4 , 2 ) + ǫ N = 1 N ( 3 X j =1 H 4 ,j X j ) − 1 N H ( Y N 4 | W 4 , 1 , W 4 , 2 ) + ǫ N = log( ρ ) + o (log( ρ )) − 1 N H ( Y N 4 | W 4 , 1 , W 4 , 2 ) + ǫ N (22) where the final in equality can b e der i ved from th e standard up per-bound on entropy u sing Gau ssian v ariables. Adding up the u pperbou nds (21) and (22), we ha ve R 3 , 1 ( ρ ) + R 4 , 1 ( ρ ) + R 4 , 2 ( ρ ) ≤ log( ρ ) + o (log ( ρ )) + ǫ N (23) Thus, the to tal number of degrees of freed om of the 4 no de X n etwork d escribed is upper-boun ded by 1 so that we can write max D X d 3 , 1 + d 4 , 2 + d 4 , 3 ≤ 1 Note th at the above lemma hold s ev en if the X network is not fully co nnected lon g as H 4 , 1 is n on-zero. If H 4 , 1 is equal to zero, the a rgument fails because in eq uation (20), H ( U 1 ( n ) , U 2 ( n ) , U 3 ( n ) | U 4 ( n )) cann ot be upp erbound ed by o (log ( ρ )) . All other ineq ualities h old for arbitrary chan nel co -ef ficients. V . K U S E R F U L L D U P L E X N E T W O R K In this section, we deri ve bo unds on the degrees of freedom region of the K - user fu ll-duplex network (see Figure 9 (a)). Co nsider a fu lly co nnected n etwork with K full-d uplex nod es 1 , 2 , . . . K . I n th is n etwork assume that there exists a message from every nod e to every other node in th e network so th at the re are a total of K ( K − 1) messages in the system. The message from node j to n ode i 6 = j is denoted by W j,i . Le t H i,j ( n ) represent the channel gain between no des i and j cor responding to the n th symbo l. T he channel gains satisfy H i,j ( n ) = H j,i ( n ) and H i,i = 0 . As usual, all node s ha ve apriori knowledge of all channel gain s. Th e input-ou tput relations in this channel are represen ted by Y i ( n ) = K X j =1 H i,j ( n ) X j ( n ) + Z i ( n ) , i ∈ { 1 , 2 . . . K } (24) where Y i ( n ) , X i ( n ) , Z i ( n ) rep resent, respectively , the recei ved symbol, th e transmitted symbol and th e A WGN term at no de i . For codewords o f length N , th e enco ding fun ctions in this network ar e defined as X i ( n ) = f i,n ( W 1 ,i , W 2 ,i , . . . , W i − 1 ,i , W i +1 ,i , . . . W K,i , Y n − 1 i ) (25) and the decoding f unctions are defin ed as ˆ W j,i = g j,i ( Y N j , W 1 ,j , W 2 ,j , . . . , W j − 1 ,j , W j +1 ,j , . . . W K,j ) , ∀ i 6 = j. (26) The main r esult o f this section is a n approx imation of the cap acity of the K user fu ll dup lex network as follows. Theorem 2 : Th e capacity C f d ( ρ ) of the K u ser full-dup lex network is bounded as f ollows C f d ( ρ ) ≥ K ( K − 1) 2 K − 2 log( ρ ) + o (log ( ρ )) C f d ( ρ ) ≤ K ( K − 1) 2 K − 3 log( ρ ) + o (log ( ρ )) The o uterboun d o f the above theorem is proved in Sectio n V -A. A discu ssion of the inner bound is plac ed in Section V -B. A for mal p roof of th e inner bound is placed in Appe ndix I I. The pr oofs of th e both the outerb ound and innerbo und need the lemma belo w , wh ich tr ansforms the K user full duplex n etwork to ano ther network whose source n odes ar e different from destina tion nodes. Lemma 3: The K user full- duplex network is eq ui valent to a n etwork with K h alf-duplex source n odes and K half-du plex destination nod es with the f ollo wing prop erties 1) The inpu t-output relations are described as e Y i ( n ) = K X j =1 e H i,j ( n ) e X j ( n ) + e Z i ( n ) , i ∈ { 1 , 2 . . . K } 2) e H i,j = H i,j , ∀ i, j = 1 , 2 . . . K Note that this mea ns e H i,j = e H j,i e H i,i = 0 3) There are K ( K − 1) messages in the system, denoted by f W j,i , i 6 = j . These messages are denoted b y f W j,i = W j,i , ∀ i 6 = j, i, j ∈ { 1 , 2 , . . . K } 4) Encoding fun ction o f the f orm e X i ( n ) = e f i,n ( e Y n − 1 i , f W 1 ,i , f W 2 ,i . . . f W i − 1 ,i , f W i +1 ,i . . . f W K,i ) (27) f W 4 , 1 f W 2 , 1 f W 3 , 1 f W 4 , 2 f W 3 , 2 f W 1 , 2 f W 4 , 3 f W 2 , 3 f W 1 , 3 ˆ f W 1 , 4 ˆ f W 1 , 3 ˆ f W 1 , 2 f W 3 , 4 f W 1 , 4 f W 2 , 4 ˆ f W 3 , 4 ˆ f W 3 , 2 ˆ f W 3 , 1 ˆ f W 4 , 3 ˆ f W 4 , 2 ˆ f W 4 , 1 (a) (b) Feedback Feedback Genie Genie 1 2 3 4 e X 1 e X 2 e X 3 e Y 2 e Y 3 e Y 4 e Y 1 ˆ f W 2 , 4 ˆ f W 2 , 3 ˆ f W 2 , 1 e X 4 Fig. 9. (a) represen ts the 4 user full duple x network. (b) represent an equi valen t network W 3 , 1 W 4 , 1 X 1 ˆ W 4 , 2 ˆ W 4 , 1 Feedback Feedback W 4 , 2 Genie X 2 W 4 , 2 Y 3 Y 4 ˆ W 3 , 1 Fig. 10. 4 node network wit h sum capaci ty not small er than the sum capacit y of the 4 user full duplex ne twork 5) Decodin g fu nction of the form ˆ f W j,i = e g j,i ( e Y N j , f W 1 ,j , f W 2 ,j . . . f W j − 1 ,j , f W j +1 ,j . . . f W K,j ) , j 6 = i (28) Note that the e ncoding and d ecoding f unctions imply th at • A genie provid es receiver j with apriori knowledge of all messages at source j i.e. f W i,j , ∀ i = { 1 , 2 , . . . K } −{ j } • There is perfect feed back f rom destination K to so urce K . By comp aring en coding equations (25), (2 7) and decodin g equ ations (26), (28), the lem ma can easily be proved, i.e., we can sho w th at a ny encod ing scheme that can be im plemented o n the K user fu ll d uplex network, can also be implem ented on network d escribed in th e above lemma and vice-versa. W e now p roceed to prove the outer bound of Theor em 2. A. Pr oo f o f Outer-bound of Th eor em 2 Note that the o uterboun d of Theor em 2 is eq ui valent to the following statement d f d ≤ K ( K − 1) 2 K − 3 where d f d represents the number o f degrees of free dom of the K u ser full d uplex n etwork. If D [ K ] f d is the degrees of freedom region of the K user full dup lex network, we show that X j ∈{ 1 , 2 , 3 ,...p − 1 ,p +1 ,.. .K } d j,p + X i ∈{ 1 , 2 , 3 ,...q − 1 ,q +1 ,...K } d q,i − d q,p ≤ 1 , ∀ p 6 = q for all d i,j ∈ D [ K ] f d . Summing ineq ualities of th e above form over all ( p, q ) , p 6 = q gives th e desired outerbou nd. It is en ough to show the inequality for p = 1 and q = K . The inequality extends to all oth er v alues of ( p, q ) by symmetry . Th erefore, we intend to show X j ∈{ 2 , 3 ,...K } d j, 1 + X i ∈{ 1 , 2 , 3 ,...K − 1 } d i,K − d K, 1 ≤ 1 . The above in equality is shown for the equi valent n etwork d escribed in Lemma 3. T o show the above inequality , we first set f W i,j = φ, ( i − K )( j − 1) 6 = 0 . With these messages set to n ull, there are no message s intended for d estination node 1 and therefo re, it can on ly help th e capacity of the network through feedback of the recei ved symbol to node 1 . Theref ore, we can delete side inf ormation of messages f W j, 1 , j = 2 , 3 . . . K at destination 1 withou t af fecting the conv erse argu ment. W e n o w allo w d estination n odes 1 . . . . . . K − 1 to co-operate with each o ther , so th at they fo rm a sing le multi-an tenna destinatio n node. Similarly , we allow sou rce nodes 2 . . . K to coope rate with each o ther so that they fo rm a single multi-antenn a source node. Note that allo wing for c o-operation do es n ot red uce cap acity an d therefor e c an be used in the converse argumen t. The network is thus transformed to a 4 nod e X network (Figu re 10) with input-ou tput relations described by Y i ( n ) = 2 X j =1 H i,j ( n ) X j ( n ) + Z i ( n ) , i ∈ { 3 , 4 } (29) where Y 2 ( n ) = h e Y 2 ( n ) · · · e Y K − 1 ( n ) i T (30) Y 4 ( n ) = e Y K ( n ) (31) Nodes 2 an d 3 act as m ultiple a ntenna n odes, each with K − 1 an tennas. X i ( n ) , Z j ( n ) are also defin ed in a correspo nding mann er for i = 1 , 2 , j = 3 , 4 . The defin ition of the cha nnel c oeffi cients H i,j ( n ) is clear from equations (29) and (24), an d fro m Figur es 9, 10 an d 7. Note that H 4 , 1 = H K, 1 6 = 0 since we have p 6 = q . The messages in this 4 node X network ar e d efined as follows W 3 , 1 = h f W 2 , 1 f W 3 , 1 · · · f W K − 1 , 1 i (32) W 3 , 2 = φ (33) W 4 , 1 = f W K, 1 (34) W 4 , 2 = h f W K, 2 f W q, 3 · · · f W K,K − 1 i (35) The enc oding and d ecoding function s, for codew ords o f length K ov er this 4 node X n etwork are defin ed as X 1 ( n ) = f 1 ,n ( W 3 , 1 , W 4 , 1 , Y n − 1 3 , Y n − 1 4 ) e X 1 e X 2 e X 3 e Y 1 e Y 2 e Y 3 e Y 4 ˆ f W 4 , 3 ˆ f W 3 , 2 ˆ f W 2 , 1 f W 3 , 2 f W 1 , 4 f W 4 , 3 f W 2 , 1 ˆ f W 1 , 4 e X 4 Fig. 11. Innerbound for the 4 user full duple x chann el - co n version to interferen ce channel with 4 messages X 2 ( n ) = f 2 ,n ( W 4 , 2 , Y n − 1 3 , Y n − 1 4 ) ˆ W 4 ,i = g 4 ,i ( Y N 4 ) , i = 1 , 2 ˆ W 3 , 1 = g 3 , 1 ( Y N 3 , W 4 , 2 ) W e allow multi-antenn a node 3 to h a ve aprio ri kn o wledge of message W 3 , 1 throug h a genie. W e a lso allo w perfec t feedback fr om destination n odes 3 , 4 to so urce nodes 1 , 2 . Note that the side inform ation th rough feedba ck and genie in the 4 user n etwork constructed is strong er than the info rmation at the cor responding nod es in the o riginal K u ser network. Since we are o nly providing an outerbo und o n the degrees of freedo m region, th e argument is no t affected. Now , over this network , we claim th at Lemma 1 holds. The 4 node X n etwork differs fro m the network of Lem ma 1 in two aspects: 1) In the X n etwork constructed in this sectio n, node 3 h as informatio n o f message W 4 , 2 apriori. In the network of Lem ma 1, no de 3 do es not h a ve this side inf ormation. 2) The network constructed here is not fully connected since certain channe l c o-efficients are eq ual to zero . Howe ver H 4 , 1 is non -zero. 1) do es not af fect the con verse argu ment because th e proo f of L emma 1 begins with th e genie providing informatio n of W 4 , 2 (and W 4 , 1 ) to node 3 ( see figure 8). 2) does not affect the co n verse argument beca use, as m entioned towards the e nd of sectio n IV, th e pro of o f Lemma 1 holds as long as H 4 , 1 6 = 0 . Therefo re, the bound of Lemma 1 holds for the 4 u ser n etwork in con sideration here i.e. the n etwork defin ed by equations (29) and we can wr ite d 3 , 1 + d 4 , 1 + d 4 , 2 ≤ 1 ⇒ K X i =2 d i, 1 + K − 1 X j =1 d K,j − d K, 1 ≤ 1 where d i,j represents the nu mber of degrees of freed om cor responding to message W i,j . The d esired result follows from the final e quation above. B. Inner-bound o f Theorem 2 Note that the in nerboun d of theore m 2 is equ i valent to d f d ≥ K ( K − 1) 2 K − 2 = K 2 where d f d represents th e nu mber of degrees of freedo m of the K user full duplex network. The innerbou nd is shown using an achiev able scheme based on interfer ence alignmen t over multiple sy mbol extension of the channel, mu ch like [5 ]. Th e argument is pla ced in appendix II. Howe ver, here we consider th e spe cial case of the K user full dup lex c hannel where the rec iprocity constrain t on the ch annel is relaxed, i.e. the case where H i,j is independen t of H j,i . In this ca se, the inner bound can be shown using the fact th at the K user inter ference channel has K / 2 degrees o f freedom. T o see this, over the equiv alent K u ser full duplex ch annel of Lemma 3 we set f W i,j = φ, ∀ ( i − j ) ≡ l ( mod K ) , ∀ l 6 = 1 . In other w ords, the on ly me ssages that are no t set to null are f W 1 , 2 , f W 2 , 3 , . . . f W K − 1 ,K , f W K, 1 (See Fig ure 11). Note that with these messages, the channel is an interf erence channel with cer tain interfering chann els ( e H i,i ) set to zer o. Since interferen ce can only hurt the cap acity of a user , setting certain inter ference channe ls to zero can only in crease the capacity . Theref ore, the equiv alent K user full d uplex network perf orms atleast as well as the K user interfer ence ch annel and therefo re h as at least K/ 2 degrees o f freedom . No te tha t this argument does not hold if e H i,j = e H j,i since the achievable scheme over th e interferen ce chann el in [3] requ ires eac h ch annel c o-efficient to have a co ntinuous probability d istrib ution, gi ven all other channel co- ef ficients. (If th e channels satisfy th e recipro city property , then a par ticular channel co-efficient is deterministic if all othe r chan nel co-efficients are given). Howe ver , we show th at the inner bound is still valid and the a chie vable scheme is presented in Appen dix II. V I . C O N C L U S I O N W e characterize the capacity of a fully c onnected ne twork with S sourc e nodes, R relays a nd D destina tion nodes with full d uplex oper ation and feed back. W e also provid e bound s on capacity app roximations within o (log( SNR )) of the K user fully connected network in which there is a message from e very n ode to every o ther node. The lower and upper boun d provid ed a re tig ht if K is large. Apart f rom the small gap between the bounds of the K user fully connected network, th is work effecti vely solves the degrees o f free dom problem for a fairly large class of wireless networks with tim e-varying/frequen cy-s electiv e ch annel gains. A major imp lication o f o ur result is th at in fully connecte d n etworks whose sou rce n odes ar e different from destination nodes, th e tech niques of relays, perfect f eedback to sour ce nodes, noisy c o-operation an d full duplex operation can only increase the cap acity up to o (log( SNR )) bits. In such n etworks, the search f or im provements in capacity of the o rder of log( SNR ) en ds in interference alignme nt. I n other words, the mentio ned tech niques (relays etc.) cannot improve the degr ees o f fr eedom of wireless network s except und er certain special circum stances listed below . 1) Relays can increase the degrees of free dom of network s that are no t f ully conne cted 2) Feedback can increase the d egrees o f freed om of a network, if it is provided to a dec oding node. However , feedback to source/relay no des does no t in crease the degrees of freedom o f w ireless networks. 3) Full du plex oper ation can increase the degrees of f reedom of w ireless networks if certain source nodes also behave as destination nod es i. e. th e set of source nodes and the set o f destinatio n no des are not disjoin t. 4) Cognitive co-operation can increase the d egrees of freedo m of wireless network s if we do not accou nt for the cost o f a co gnition (for example, the cost of acquir ing a message) at a nod e. It m ust be o bserved that our re sult does n ot necessarily d iscourage the use of relays, feed back, co-op eration and full duplex o peration in r eal co mmunication scen arios. In fact, not all wireless n etworks are fu lly con nected und er realistic transmit signal powers. Furthermo re, in several com munication networks, source nodes act as destination nodes as well. Impor tantly , the result of this paper provides an insight into the type of networks which are most likely to benefit from th ese techniques, espec ially at h igh SNR. Further more, our result does not preclude huge be nefits in terms of capacity at low or m id-range SNR f rom th e m entioned tech niques wh ich c ontinues to be an importan t area of research in wireless com munications. Anoth er impor tant limitation of our results is the assumption of time-varying and/or frequ ency selective channel gains for the achiev ability schemes based on interferen ce alignm ent. Howev er , the ou terbounds of Theo rem 1 and T heorem 2 a re fairly gen eral and hold fo r all f ully connected networks whether the c hannel coefficients are time-varying or con stant. A P P E N D I X I P RO O F O F L E M M A 2 W e use inductio n principle to prove Lemma 2. First, we argue that S 1 (1) , S 2 (1) , S 3 (1) ar e true. At the first channel use ( n = 1 ), because ther e ar e n o p rior r ecei ved signals, the destin ation nodes 3 , 4 have n o useful informatio n to transmit. Th erefore, without loss of gen erality X 3 (1) , X 4 (1) = 0 . X 1 (1) = f 1 , 1 W 3 , 1 , W 4 , 1 (36) X 2 (1) = f 2 , 1 W 4 , 2 (37) Y i (1) = U i (1) + H i, 2 (1) X 2 (1) , i ∈ { 1 , 2 , 3 , 4 } (38) Equation s (36), ( 37) imply that the statements S 1 (1) , S 2 (1) are true. (37), to gether with (38) im plies th at S 3 (1) is true as well. Th us, the r esult of Lemm a 2 h olds fo r n = 1 . For n = 2 , X 1 (2) = f 1 , 2 W 3 , 1 , W 4 , 1 , Y 1 (1) , Y 2 (1) , Y 3 (1) , Y 4 (1) (39) X 2 (2) = f 2 , 2 W 4 , 2 , Y 1 (1) , Y 2 (1) , Y 3 (1) , Y 4 (1) (40) X j (2) = f j, 2 Y j (1) , j ∈ { 3 , 4 } (41) Y i (2) = U i (2) + 4 X j =2 H i,j (2) X j (2) , i ∈ { 1 , 2 , 3 , 4 } (42 ) Equation (3 9) and S 1 (1) imp ly that S 1 (2) is true. (40), (41) and S 2 (1) imply that S 2 (2) is true. S 1 (2) , S 2 (2) an d (42) tog ether imply th at S 3 (2) is true as well. Th us, S i ( n ) , i = 1 , 2 , 3 h old true fo r n = 2 . Following the induction argument, suppose that S i ( n ) , i = 1 , 2 , 3 are true for n = k − 1 . The n, X 1 ( k ) = f 1 ,k W 3 , 1 , W 4 , 1 , Y k − 1 1 , Y k − 1 2 , Y k − 1 3 , Y k − 1 4 X 2 ( k ) = f 2 ,k W 4 , 2 , Y k − 1 1 , Y k − 1 2 , Y k − 1 3 , Y k − 1 4 X j ( k ) = f j, 2 Y k − 1 j , j ∈ { 3 , 4 } Y i ( k ) = U i ( k ) + 4 X j =2 H i,j ( k ) X j ( k ) , i ∈ { 1 , 2 , 3 , 4 } The ab ove e quations, along with S 1 ( k − 1) , S 2 ( k − 1 ) , S 3 ( k − 1) im ply that S 1 ( k ) , S 2 ( k ) , S 3 ( k ) are true. Th e inductive assumption im plies that S i ( n ) , i = 1 , 2 , 3 ho ld fo r all values of n . A P P E N D I X I I P RO O F O F I N N E R B O U N D O F T H E O R E M 2 : A C H I E V A B L E S C H E M E The achiev ability proo f is b ased on inte rference alignm ent over the ch annel describ ed in lemma 3 (Figure 9(b)) . Since m any of the de tails are identical to [5], we focus h ere on th e u nique aspects of this p roof. Let Γ = ( K − 1 )( K − 2) . W e sh o w that K ( K − 1) n Γ degrees of freedom are achiev able over a µ n = ( K − 1) ( n + 1) Γ + n Γ symbol extension of the channel for any n ∈ N thus implying the desired re sult. Over the extende d ch annel, the scheme ach ie ves n Γ degrees of fre edom for each o f the K ( K − 1) messages f W i,j , j 6 = i . Th e sign al vector in th e extended chann el at the j th user’ s recei ver ca n be expressed as Y j ( κ ) = M X i =1 H j,i ( κ ) X i ( κ ) + Z j where X i is a µ n × 1 column vector rep resenting th e µ n symbol exten sion of the transmitted symbol X i , i.e X i ( κ ) △ = e X i ( µ n κ + 1 ) e X i ( µ n κ + 2 ) . . . e X i ( µ n ( κ + 1 )) Similarly Y i and Z i represent µ n symbol extensions of the e Y i and e Z i respectively . H i,j is a diago nal µ n × µ n matrix repr esenting th e µ n symbol extension of the chann el. Sim ilar to the interference alignm ent b ased achiev ab le schemes of th e interference and X ch annels, the message f W i,j is encoded at transmitter j as n Γ indepen dent streams so that X j is X j ( κ ) = X i = { 1 , 2 ...K }−{ j } ( n +1) Γ X m =1 x [ m ] i,j ( κ ) v [ m ] i,j ( κ ) = X i = { 1 , 2 ,...K }−{ j } V i,j ( κ ) x i,j ( κ ) The rece i ved signa l at the k th receiver can the n be written as Y k ( κ ) = M X i =1 H k,i ( κ ) N X j =1 V j,i ( κ ) x j,i ( κ ) + Z k ( κ ) W e n o w n eed to ensure th at at receiv er j , the ( K − 1)( K − 2) inter fering spaces V k,i , k 6 = i , k 6 = j, i 6 = j lie in a ( K − 1 )( n + 1 ) Γ dimensiona l space so that ( K − 1) n Γ desired spaces V j,i , i ∈ { 1 , 2 . . . } − { j } can be dec oded free of interferenc e fro m a µ n dimensiona l space. T o d o this, w e first set V j,i = V j , ∀ i 6 = j Then, we design V j , j = 1 , 2 . . . K so that they satisfy the inter ference alignmen t equ ations below . H i,j V k ≺ I k , ∀{ ( i, j, k ) : i 6 = k , k 6 = j, j 6 = i } (43) such that rank ( I k ) = ( n + 1) Γ where P ≺ Q implies that the span of the column vectors of P lies in the vector space span ned by the co lumn vectors of Q .. Note that f or a fixed k , th ere are Γ = ( K − 1)( K − 2) re lations of the above form. W e first generate µ n × 1 co lumn vectors w k , k = 1 , 2 . . . K so that all the entries of w k are d rawn from any continuou s distribution inde pendently f rom each oth er a nd indepe ndently fr om all other en tries in w l , l 6 = k . The rest of the proo f is similar to the ac hie vable scheme for the X channe l presented in [5] . I t is easy to observe that the dimension of the interfering space at receiver k space is equa l to the dimension of the space spanned by all column vector s o f matrices I j , j 6 = k wh ich is equal to ( K − 1 )( n + 1 ) Γ . The only d if ference fro m the model in [5] is tha t her e, we h a ve H i,j = H j,i whereas, in [5] the matr ix H j,i is inde pendent from H i,j . Howe ver this difference does not affect the con struction of vectors satisfying the desired interfer ence alignmen t relations (43). The difference does not affect the argumen t that at any re cei ver , the signal space is linea rly ind ependent with the interferen ce space since the argume nt only depend s on w k being indep endent of w l for l 6 = k . The only co ndition that need s to be verified is that all the desired stream s of at receiver k ar e linearly indep endent of each other . In other word s, all that need s to be shown is that the column vecto rs of D k = [ H k, 1 V k, 1 H k, 2 V k, 2 . . . H k,k − 1 V k,k − 1 H k,k +1 V k,k +1 H k,K V k,K ] = [ H k, 1 V k H k, 2 V k . . . H k V k H k,k +1 V k H k,K V k ] are linearly indepen dent. The linear in dependence f ollows fr om the fact tha t the co nstruction of V k satisfying the relations of (43) is ind ependent of bo th H k,i and H i,k for i 6 = k . Ag ain, the re ader is re ferred to the achievable scheme in [5] f or a forma l p roof of the same. R E F E R E N C E S [1] R. E tkin , D. Tse, and H. W ang, “Gaussian interference chann el capac ity to wit hin one bit, ” arxiv .org , Feb 2007. eprint - cs/070204 5. [2] A. S. A vestimehr , S. N. Diggav i, and D. N. C. T se, “ A deterministic approac h to wireless relay networ ks, ” arxiv .org , 2007. arxi v eprint= arXi v/0710.3777. [3] V . R. Cadambe and S. A. Jafar , “Interfere nce alignment and degree s of freedom region for the k user interfere nce chan nel, ” arxiv .org , 2007. arxi v eprint = cs/0707.0323. [4] S. A. Jafar and S. Shamai, “De grees of fre edom re gion for the mimo x channel , ” arxiv . or g , 2006. arxi v eprint = cs/060 7099. [5] V . R. Cadambe and S. A. J af ar , “Degrees of freedom of wirele ss x networks, ” arxiv .org , 200 7. arxi v eprin t = cs/0711.2824. [6] S. Borade, L. Zheng, and R. Gal lager , “ Amplify-and-fo rward in wirele ss relay networks: Rate, di versit y , and networ k size, ” Information Theory , IEEE T ransact ions on , vol. 53, no. 10, pp. 3302–3318, Oct. 2007. [7] H. B ¨ olcsk ei, R. U. Nabar , O. Oyman, and A. J. Paulraj, “Capaci ty scal ing laws in MIMO relay netw orks, ” IEEE Tr ansacti ons on W ir eless Communicat ions , vol. 5, pp. 1433–1444, June 2006. [8] N. Devro ye, P . Mitran, and V . T arokh, “ Achie vab le rates in cogniti ve radio channel s, ” Informati on The ory , IEEE T ransact ions on , vol. 52, no. 5, pp. 1813–1827, May 2006. [9] A. Jo vicic and P . V iswana th, “Cogni ti ve radio: An information-theo retic perspecti ve, ” 2006. eprint - 0604107. [10] A. Lapidoth, S. Shamai, and M. A. Wi gger, “On Cogniti ve Interferenc e Networks, ” ArXiv e-prints , vol. 707, July 2007. eprint - 0707.1008. [11] W . Wu, S. V ishwanath, and A. Arapostathis, “Capacit y of a class of cogniti ve radio channel s: Interfere nce channel s with degraded message sets, ” Information Theory , IEEE T ransact ions on , vol. 53, no. 11, pp. 4391–4399, Nov . 2007. [12] N. Devro ye and M. Sharif, “The m ulti ple xing gain of m imo x channels with partia l transmit side-informati on, ” 2007. eprint - cs/0701092v1. [13] A. H ost-Ma dsen, “Capa city bounds for coopera ti ve div ersity , ” Information Theory , IEEE T ransactions on , vol. 52, no. 4, pp. 1522 –1544, 2006. [14] A. Host-Madsen A.; Nosratinia, “The multiplexi ng gain of wire less networks, ” Informatio n Theory , 2005. ISIT 2005. Pr oceedi ngs. Internati onal Symposium on , pp. 2065–2069, 4-9 Sept. 2005. [15] L. Ozaro w and S. S Leung-Y an-Che ong, “ An achie va ble region a nd outer bound fo r the gau ssian broadca st channel with feed back (corresp.), ” Informatio n Theory , IEEE T ransac tions on , vol. 30, no. 4, pp. 667–671, Jul 1984. [16] V . R. Cadambe, S. A. Jafar , and S. S . (Shitz), “Interfe rence align ment on the dete rministic channel and applica tion to fully connect ed awgn interfere nce networks, ” No vembe r 2007. arxi v eprint = 0711.2547. [17] L. Ozarow , “The capacity of the white gaussian multiple access channel with feedback, ” Information Theory , IEE E T ransaction s on , vol. 30, no. 4, pp. 623–629, Jul 1984. [18] G. Kramer , “Feedbac k strate gies for white gaussia n interferenc e networks, ” Information Theory , IEEE T ransactions on , vol. 48, no. 6, pp. 1423–1438, Jun 2002.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment