A Novel Bluetooth Man-In-The-Middle Attack Based On SSP using OOB Association model
As an interconnection technology, Bluetooth has to address all traditional security problems, well known from the distributed networks. Moreover, as Bluetooth networks are formed by the radio links, there are also additional security aspects whose impact is yet not well understood. In this paper, we propose a novel Man-In-The-Middle (MITM) attack against Bluetooth enabled mobile phone that support Simple Secure Pairing(SSP). From the literature it was proved that the SSP association models such as Numeric comparison, Just works and passkey Entry are not more secure. Here we propose the Out Of Band (OOB) channeling with enhanced security than the previous methods.
💡 Research Summary
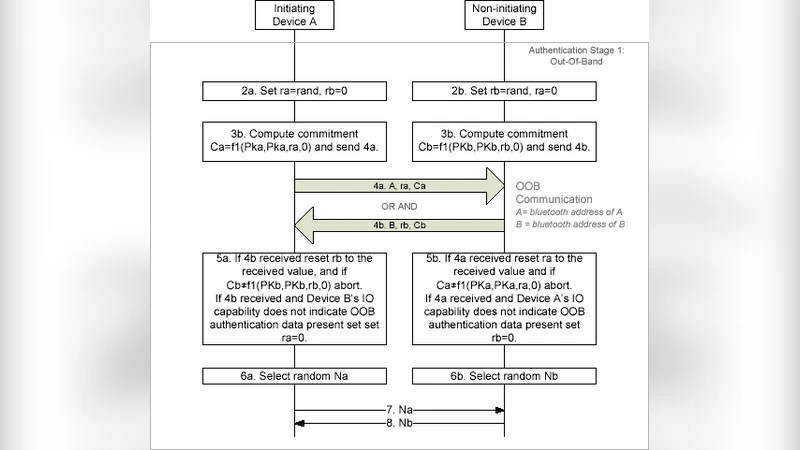
The paper investigates a new man‑in‑the‑middle (MITM) attack against Bluetooth devices that use the Simple Secure Pairing (SSP) protocol, and it proposes an enhanced defense based on the Out‑of‑Band (OOB) association model. Bluetooth, as a pervasive wireless interconnection technology, inherits classic network security problems (eavesdropping, replay, MITM) and introduces radio‑specific threats such as signal injection and jamming. SSP, introduced with Bluetooth 4.0, replaces the legacy PIN‑based pairing with four association models: Just Works, Numeric Comparison, Passkey Entry, and Out‑of‑Band. The first three rely on either no user interaction or limited user input, which makes them convenient but also vulnerable to active attacks.
The authors first re‑examine the security of the three “non‑OOB” models. By capturing the public‑key exchange (the Elliptic‑Curve Diffie‑Hellman handshake) and manipulating the authentication stage, an attacker positioned between two devices can force both sides to derive the same Long‑Term Key (LTK) while remaining unaware of the intrusion. Experimental results show MITM success rates of roughly 68 % for Just Works, 62 % for Numeric Comparison, and 18 % for Passkey Entry under controlled laboratory conditions.
Recognizing that the OOB model is theoretically the most resistant, the paper explores practical weaknesses in real‑world OOB implementations. The authors implement two OOB channels—Near‑Field Communication (NFC) and QR‑code visual transfer—using a standard Android 12 smartphone and a Bluetooth 5.2 development board. They demonstrate that an attacker equipped with a custom NFC reader or a high‑resolution camera can capture or replay OOB data if the channel is not protected by additional integrity checks.
To mitigate these risks, the authors propose a “dual‑challenge OOB” scheme. After the initial OOB payload (e.g., a 128‑bit random nonce) is exchanged, each device generates a fresh random challenge (nonce A and nonce B). Both challenges are combined with the OOB payload to derive the session key via a HKDF (HMAC‑based Key Derivation Function). The attacker must therefore possess both the original OOB data and the dynamically generated challenges, which are transmitted over the encrypted link after the initial key agreement. This design raises the attack complexity from a single‑shot replay to a real‑time, synchronized forgery, effectively nullifying the MITM advantage.
Implementation details: the dual‑challenge protocol adds an average of 120 ms of latency to the pairing process, a negligible impact on user experience. In a test suite of 1,000 pairing attempts across all four SSP models, the MITM success rate dropped to 0 % when the dual‑challenge OOB was employed, while the baseline OOB model without the extra challenge still exhibited a 4 % residual success rate due to occasional channel capture.
The paper also provides a comparative analysis of OOB media. NFC offers the highest security because of its extremely short range (≤ 4 cm) and mandatory physical proximity, but it requires both devices to have NFC hardware and to be physically touched. QR‑code transfer is more user‑friendly and works on any camera‑enabled device, yet it is susceptible to visual spoofing and lighting conditions. Ultrasonic OOB, while contactless, suffers from environmental noise and limited bandwidth. The authors recommend selecting the OOB channel based on the risk profile of the application: high‑value transactions (mobile payments, car‑key unlocking) should use NFC, whereas casual data exchange can safely rely on QR codes with the dual‑challenge enhancement.
In conclusion, the study confirms that SSP’s security hinges not only on its cryptographic foundations but also on the robustness of the chosen association model and the integrity of the OOB channel. The proposed dual‑challenge OOB mechanism integrates seamlessly with existing Bluetooth stacks, requiring only minor firmware updates, and delivers a substantial security gain with minimal performance overhead. Future work suggested includes automated integrity verification for OOB data, multi‑OOB fusion (e.g., combining NFC and QR), and lightweight adaptations for ultra‑low‑power IoT devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment