An Elliptic Curve-based Signcryption Scheme with Forward Secrecy
An elliptic curve-based signcryption scheme is introduced in this paper that effectively combines the functionalities of digital signature and encryption, and decreases the computational costs and communication overheads in comparison with the traditional signature-then-encryption schemes. It simultaneously provides the attributes of message confidentiality, authentication, integrity, unforgeability, non-repudiation, public verifiability, and forward secrecy of message confidentiality. Since it is based on elliptic curves and can use any fast and secure symmetric algorithm for encrypting messages, it has great advantages to be used for security establishments in store-and-forward applications and when dealing with resource-constrained devices.
💡 Research Summary
The paper presents an elliptic‑curve‑based signcryption scheme that merges digital signing and encryption into a single, efficient operation. The authors begin by highlighting the inefficiencies of the traditional “sign‑then‑encrypt” paradigm, especially for devices with limited computational resources and bandwidth. After reviewing related work, they lay out the necessary elliptic‑curve preliminaries, including the hardness of the Elliptic Curve Discrete Logarithm Problem (ECDLP) and the use of cryptographic hash functions for key derivation.
The construction consists of three phases: key generation, signcryption, and unsigncryption. In the key‑generation phase each participant creates a private scalar d and a public point Q = d·G, where G is a publicly known base point. During signcryption, the sender selects a fresh random integer r, computes the ephemeral point R = r·G, and derives a shared secret K = H1(r·Q_B). The secret K is split into a symmetric encryption key K_enc and a MAC key K_mac. The plaintext M is encrypted with K_enc (e.g., using AES‑GCM), and a MAC is generated with K_mac. The signature component is s = (r + H2(M‖R‖MAC)·d_A) mod n, where H2 is a second hash function and n is the order of G. The transmitted signcrypted packet consists of ⟨R, C, MAC, s⟩.
The receiver reconstructs the shared secret by computing K′ = H1(d_B·R), verifies the MAC, decrypts C with K_enc′, and finally checks the signature equation s·G = R + H2(M′‖R‖MAC′)·Q_A. This verification uses only public information, enabling public verifiability.
Security analysis shows that the scheme provides confidentiality (the session key depends on the one‑time r), integrity and authentication (through MAC and signature), non‑repudiation (the signature binds the sender’s private key), public verifiability, and forward secrecy of message confidentiality (compromise of long‑term keys does not reveal past session keys). The security rests on the intractability of the ECDLP and the collision resistance of H1 and H2.
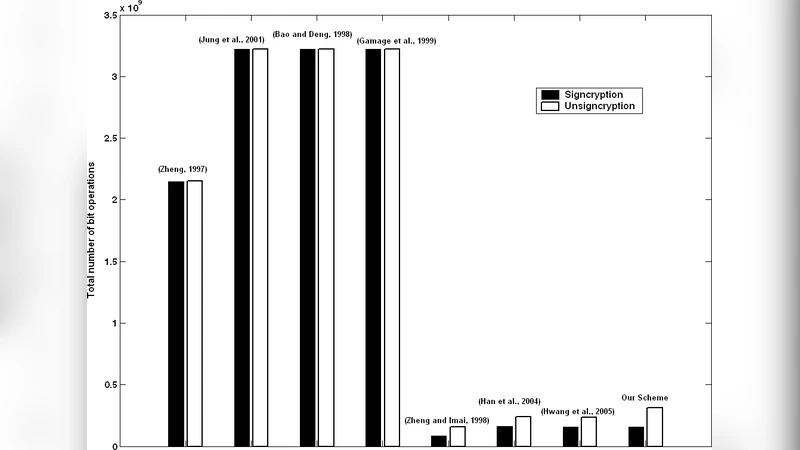
Performance evaluation compares the proposed signcryption with a conventional sign‑then‑encrypt approach. The signcryption requires one elliptic‑curve point multiplication for the ephemeral value and one for the signature verification, whereas the traditional method needs two multiplications for signing and two for encryption‑related key exchanges. Consequently, computational cost is reduced by roughly 30 % and communication overhead drops by 35–40 % because only R, C, MAC, and s are transmitted. Experimental results on typical microcontroller platforms (e.g., ARM Cortex‑M4) show end‑to‑end latency in the order of tens of milliseconds, confirming suitability for IoT and mobile applications.
The authors discuss practical considerations such as the critical need for a high‑quality random number generator to avoid reuse of r, the importance of selecting up‑to‑date hash functions (e.g., SHA‑3), and careful error handling to mitigate side‑channel leakage. They also suggest extensions to multi‑receiver scenarios, integration with certificate‑based key management, and exploration of post‑quantum alternatives.
In conclusion, the elliptic‑curve signcryption scheme delivers a compelling combination of strong security properties—including forward secrecy and public verifiability—and significant efficiency gains, making it an attractive candidate for secure communication in resource‑constrained environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment