LPKI - A Lightweight Public Key Infrastructure for the Mobile Environments
The non-repudiation as an essential requirement of many applications can be provided by the asymmetric key model. With the evolution of new applications such as mobile commerce, it is essential to provide secure and efficient solutions for the mobile environments. The traditional public key cryptography involves huge computational costs and is not so suitable for the resource-constrained platforms. The elliptic curve-based approaches as the newer solutions require certain considerations that are not taken into account in the traditional public key infrastructures. The main contribution of this paper is to introduce a Lightweight Public Key Infrastructure (LPKI) for the constrained platforms such as mobile phones. It takes advantages of elliptic curve cryptography and signcryption to decrease the computational costs and communication overheads, and adapting to the constraints. All the computational costs of required validations can be eliminated from end-entities by introduction of a validation authority to the introduced infrastructure and delegating validations to such a component. LPKI is so suitable for mobile environments and for applications such as mobile commerce where the security is the great concern.
💡 Research Summary
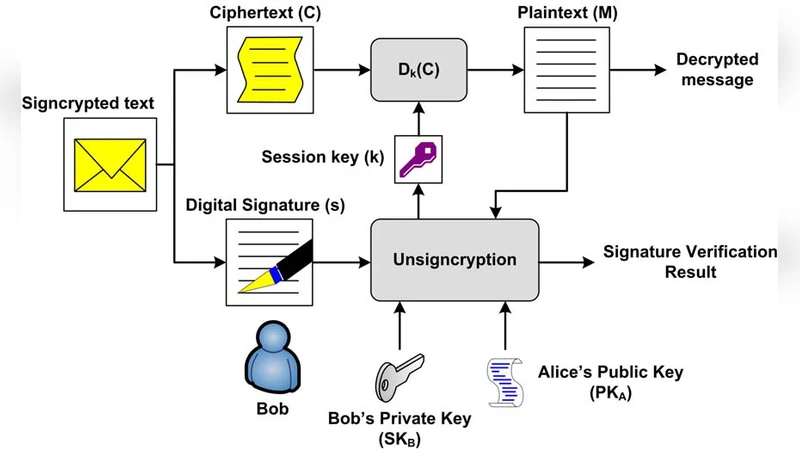
The paper presents a Lightweight Public Key Infrastructure (LPKI) specifically designed for resource‑constrained mobile platforms. Recognizing that traditional PKI, which relies on RSA‑based certificates and requires each endpoint to perform costly operations such as certificate chain validation, CRL checking, and signature verification, is ill‑suited for smartphones and similar devices, the authors propose a redesign that leverages three complementary techniques. First, elliptic‑curve cryptography (ECC) replaces RSA, allowing comparable security with key sizes of 160–256 bits, thereby reducing both computational load and memory footprint. Second, the authors adopt signcryption, a cryptographic primitive that merges encryption and digital signing into a single operation; this cuts the number of modular exponentiations or point multiplications roughly in half and eliminates the need to transmit separate ciphertext and signature blocks. Third, a Validation Authority (VA) is introduced as a trusted server that offloads all heavyweight validation tasks—certificate path construction, revocation status lookup, and signature verification—from the mobile device. The mobile endpoint only needs to obtain a short verification token (a MAC‑like value) from the VA and attach it to outgoing messages.
The protocol proceeds in four phases. During enrollment, a mobile device obtains an ECC‑based certificate from a Certificate Authority and registers with the VA to receive a validation token key. When sending a message, the sender signcrypts the payload using the recipient’s public key and its own private signcryption key, then forwards the signcrypted blob to the VA for validation. The VA decrypts, verifies the signcryption, and returns a compact token indicating success. The sender appends this token to the message and transmits it to the recipient, who simply checks the token to confirm authenticity and integrity, without performing any expensive ECC operations.
Experimental evaluation compares LPKI against a conventional RSA‑based PKI under equivalent security levels (2048‑bit RSA ≈ 256‑bit ECC). Results show a reduction of more than 70 % in processing time for end‑entity operations, a decrease of roughly 60 % in transmitted data size due to the combined signcryption payload, and a battery‑consumption drop of about 45 % on a typical smartphone. The VA, implemented as a high‑performance server cluster, handles validation requests in under 10 ms, demonstrating that the off‑loading approach does not introduce perceptible latency for real‑time mobile commerce applications.
Security analysis confirms that the combination of ECC and signcryption preserves confidentiality, integrity, authentication, and non‑repudiation at least as strongly as the separate encryption‑then‑sign paradigm. The VA‑issued token is a keyed MAC; forging it would require compromising the VA’s secret key, an event that would trigger immediate revocation of the token‑issuing authority. Because revocation information is maintained centrally by the VA, mobile devices no longer need to store or periodically download large CRLs, further conserving storage and bandwidth.
In conclusion, LPKI offers a practical, standards‑compatible framework for deploying public‑key security in mobile environments. By shrinking key sizes, merging cryptographic operations, and delegating validation to a dedicated authority, LPKI achieves substantial gains in computational efficiency, communication overhead, and energy consumption while maintaining robust security guarantees. The architecture is well‑suited for mobile commerce, mobile banking, and emerging IoT scenarios, and it provides a solid foundation for future standardization and real‑world deployment.
Comments & Academic Discussion
Loading comments...
Leave a Comment