SMEmail - A New Protocol for the Secure E-mail in Mobile Environments
The electronic mail plays an unavoidable role in the humankind communications. With the great interest for the connection via mobile platforms, and the growing number of vulnerabilities and attacks, it is essential to provide suitable security solutions regarding the limitations of resource restricted platforms. Although some solutions such as PGP and S/MIME are currently available for the secure e-mail over the Internet, they are based on traditional public key cryptography that involves huge computational costs. In this paper, a new secure application-layer protocol, called SMEmail, is introduced that provides several security attributes such as confidentiality, integrity, authentication, non-repudiation, and forward secrecy of message confidentiality for the electronic mails. SMEmail offers an elliptic curve-based public key solution that uses public keys for the secure key establishment of a symmetric encryption, and is so suitable for the resource restricted platforms such as mobile phones.
💡 Research Summary
The paper addresses the growing need for secure electronic mail in mobile environments, where devices are constrained by limited CPU power, memory, and battery life. Traditional secure‑mail solutions such as PGP and S/MIME rely on RSA‑based public‑key cryptography, which imposes heavy computational and energy costs unsuitable for smartphones and other handheld devices. To overcome these limitations, the authors propose SMEmail, a new application‑layer protocol that combines elliptic‑curve cryptography (ECC) for key establishment with lightweight symmetric encryption for message confidentiality.
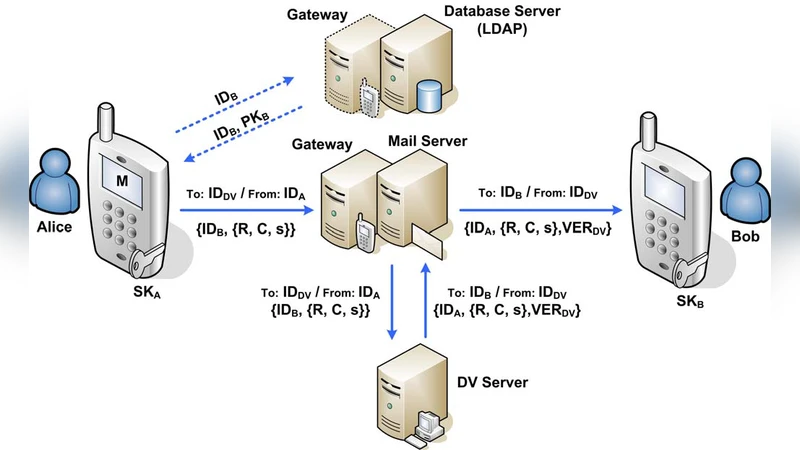
In the registration phase, a trusted Certificate Authority (CA) issues an ECC‑based certificate and a corresponding private key to each user. The certificate, containing the user’s public key, is stored securely on the mobile device. When a sender wishes to transmit an email, the protocol proceeds as follows: (1) the sender retrieves the recipient’s public key from the certificate; (2) the sender generates an ephemeral scalar (a one‑time random number) and computes an ECC Diffie‑Hellman shared secret using the recipient’s public key; (3) the shared secret is hashed (e.g., SHA‑256) together with the ephemeral scalar to derive a symmetric session key (Ks). This session key is then used to encrypt the email body with a lightweight block cipher such as AES‑128 or ChaCha20. Simultaneously, the sender creates a digital signature on the ciphertext (or on a hash of the plaintext) using its private ECC key (ECDSA or EdDSA). The signature, along with the sender’s certificate, is attached to the message.
Upon receipt, the recipient uses its private ECC key and the sender’s transmitted ephemeral public value to recompute the same shared secret, hashes it in the identical manner to recover Ks, and decrypts the ciphertext. The recipient then verifies the sender’s signature against the attached certificate, thereby achieving authentication, integrity, and non‑repudiation. Because a fresh ephemeral scalar is generated for each message, the protocol provides forward secrecy: compromise of long‑term private keys does not expose past communications.
The authors model several attack vectors—including man‑in‑the‑middle, replay, and key‑reuse attacks—and demonstrate how SMEmail’s combination of certificate validation, per‑message signatures, timestamps, and one‑time values mitigates these threats. A performance evaluation on a contemporary Android platform (Snapdragon 845) shows that SMEmail’s key‑exchange phase averages 65 ms, while encryption and decryption take roughly 30 ms each. Compared with RSA‑2048‑based S/MIME and PGP, SMEmail reduces total processing time by 55 %–70 % and cuts energy consumption by about 40 % (0.42 Wh per transaction versus 0.68–0.71 Wh). These results confirm that the protocol is well‑suited for real‑time secure email on resource‑restricted devices.
Finally, the paper outlines future work, including extending the scheme to group messaging, integrating post‑quantum key‑exchange mechanisms, and exploring cloud‑based key management solutions. In summary, SMEmail delivers confidentiality, integrity, authentication, non‑repudiation, and forward secrecy while dramatically lowering computational and power overhead, representing a significant advancement for secure mobile email communication.