Solutions to the GSM Security Weaknesses
Recently, the mobile industry has experienced an extreme increment in number of its users. The GSM network with the greatest worldwide number of users succumbs to several security vulnerabilities. Although some of its security problems are addressed in its upper generations, there are still many operators using 2G systems. This paper briefly presents the most important security flaws of the GSM network and its transport channels. It also provides some practical solutions to improve the security of currently available 2G systems.
💡 Research Summary
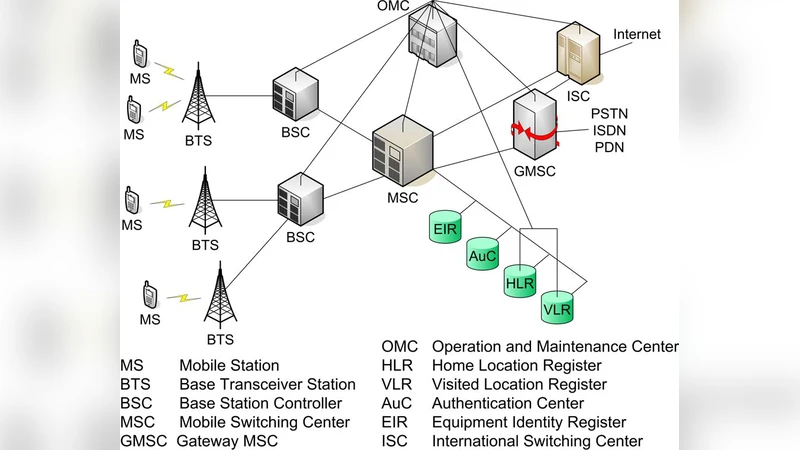
The paper provides a concise yet thorough examination of the security shortcomings inherent in the second‑generation Global System for Mobile Communications (GSM) and proposes practical countermeasures that can be deployed on existing 2G networks. It begins by outlining the architecture of GSM, distinguishing between control channels (BCCH, CCCH, SDCCH) that are typically transmitted in clear text and traffic channels (TCH, BCC) that may be encrypted. The authors then dissect the authentication and key‑exchange process, emphasizing that the widely used A3/A8 algorithms—particularly the legacy COMP128‑1 implementation—truncate the 64‑bit session key, reducing the effective key space to roughly 2^54. This weakness, combined with the fact that the secret subscriber key (Ki) resides on the SIM card, makes SIM cloning feasible through physical attacks such as voltage injection or micro‑probing.
Next, the paper evaluates the encryption algorithms employed on the radio link. A5/1, although stronger than its predecessor, is vulnerable to key‑stream prediction and rainbow‑table attacks; A5/2 is deliberately weakened and can be broken within seconds using off‑the‑shelf software‑defined radio equipment. Consequently, an adversary equipped with a modest SDR can eavesdrop on voice calls and intercept data in real time.
The authors also highlight vulnerabilities in the roaming and Temporary Mobile Subscriber Identity (TMSI) reallocation procedures. Because TMSI updates are infrequent and the mapping between TMSI and the permanent IMSI is not adequately protected across base stations, traffic‑analysis attacks can reveal user movement patterns and enable targeted surveillance.
To mitigate these threats, the paper proposes a multi‑layered defense strategy. At the authentication layer, it recommends abandoning COMP128‑1 entirely and migrating to public‑key‑based mechanisms such as EAP‑SIM or EAP‑AKA, which render the exposure of Ki ineffective for forging new sessions. For encryption, the authors advocate replacing A5/1 and A5/2 with the stronger A5/3 (or a 128‑bit KASUMI variant) and ensuring that the update is rolled out via base‑station firmware patches. They further suggest encapsulating all over‑the‑air traffic in an additional encryption tunnel—e.g., IPsec or TLS—between the handset and the network gateway, thereby protecting even the traditionally unencrypted control channels.
On the SIM side, the paper advises hardening the card against physical extraction by storing Ki in an encrypted, tamper‑detecting memory region and integrating voltage‑monitoring circuitry that disables the card under abnormal conditions.
From an operator perspective, the authors stress the importance of continuous security monitoring. Deploying intrusion detection systems that flag abnormal RAND retransmissions, excessive authentication failures, or suspicious roaming requests can preempt SIM‑cloning and man‑in‑the‑middle attempts. Regular firmware updates, combined with user notifications encouraging handset upgrades, are essential to maintain a resilient security posture.
Finally, while acknowledging the long‑term industry trend toward LTE and 5G—both of which incorporate robust mutual authentication, integrity protection, and end‑to‑end encryption—the paper recognizes that many operators must continue to support 2G for legacy devices and coverage in remote areas. Therefore, the proposed enhancements—algorithm upgrades, key‑management reforms, additional tunneling, and hardened SIM designs—offer a realistic pathway to substantially improve the security of currently deployed 2G networks without requiring a wholesale migration.
Comments & Academic Discussion
Loading comments...
Leave a Comment