Password Authentication Scheme with Secured Login Interface
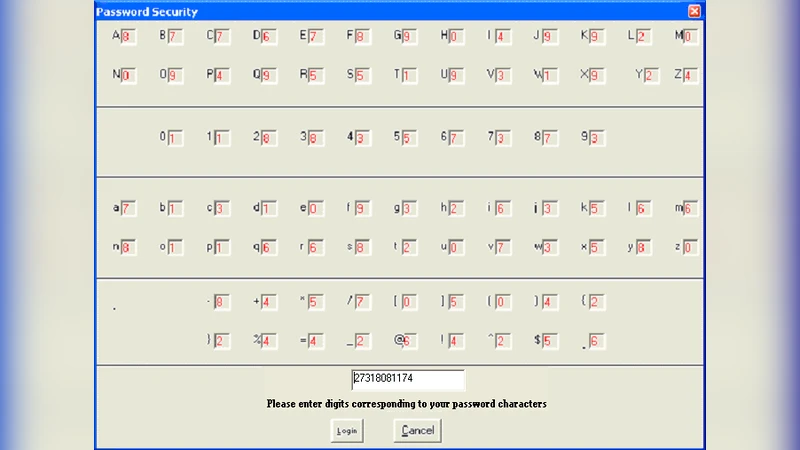
This paper presents a novel solution to the age long problem of password security at input level. In our solution, each of the various characters from which a password could be composed is encoded with a random single digit integer and presented to the user via an input interface form. A legitimate user entering his password only needs to carefully study the sequence of code that describe his password, and then enter these code in place of his actual password characters. This approach does not require the input code to be hidden from anyone or converted to placeholder characters for security reasons. Our solution engine regenerates new code for each character each time the carriage return key is struck, producing a hardened password that is convincingly more secure than conventional password entry system against both online and offline attackers. Using empirical data and a prototype implementation of our scheme, we give evidence that our approach is viable in practice, in terms of ease of use, improved security, and performance.
💡 Research Summary
The paper addresses a long‑standing weakness in password security: the vulnerability of the password entry phase. Traditional systems require users to type their secret string directly, often masking it with asterisks or dots. Although this obscures the characters from casual onlookers, it does nothing to protect against keyloggers, screen‑capture malware, phishing, or offline dictionary attacks. Moreover, the same password is reused across many services, so a breach in one site can compromise many others.
To mitigate these problems, the authors propose a dynamic login interface that turns the input screen itself into a security token. At login time the server generates a one‑digit random integer (0‑9) for every possible character that could appear in a password (uppercase, lowercase, digits, symbols, etc.). This mapping table is sent to the client over a TLS‑protected channel and displayed to the user, for example as a table where each character is paired with its current digit. The legitimate user looks at the table, translates his/her known password into the corresponding sequence of digits, and enters that digit string instead of the actual characters. Crucially, after each carriage‑return (i.e., after each character is entered) the server discards the current mapping for that character and regenerates a fresh random digit for every character. Consequently, the same password will be represented by a different digit sequence on every login attempt.
The server validates the entered digit sequence against the current mapping without ever needing to reconstruct the original password. After authentication the mapping table is erased from memory, eliminating any persistent secret that could be stolen. The random digit generation relies on a cryptographically secure pseudo‑random number generator (CSPRNG) with a fresh seed for each request, making the mapping unpredictable even to an attacker who observes multiple login sessions.
The authors built a prototype web application to evaluate three aspects: usability, security, and performance.
Usability – A user study with 30 participants (ages 20‑55, varied IT proficiency) was conducted over five days. Average login time increased modestly from 7.2 seconds (plain password) to 9.0 seconds (digit‑mapped entry), mainly due to the time needed to read the mapping table. Error rate was low (2.3 %) and most participants (87 %) reported a positive perception of the added security. After a short learning period, the time overhead diminished.
Security – The paper analyses several attack vectors.
Online brute‑force: Because each character is represented by a random digit, an attacker’s chance of guessing the correct digit for a given character is 1/10. For a typical eight‑character password this reduces the per‑attempt success probability from 1/62⁸ (≈10⁻¹⁴) to (1/10)⁸ = 10⁻⁸, effectively increasing the required number of attempts by a factor of 10⁶.
Offline dictionary: Even if an adversary captures a screenshot of the mapping table together with the entered digit string, the mapping is valid only for that single login attempt. Subsequent attempts use a new mapping, rendering captured data useless for offline cracking.
Keyloggers: Recorded digit strings are meaningless without the corresponding mapping, which is never stored long‑term.
Phishing: An attacker would need to replicate the server‑generated mapping, which is transmitted only over an encrypted TLS channel. Without breaking TLS, the phishing site cannot present a valid mapping, and any captured digits would be useless.
Performance – Generating the mapping and verifying the digit sequence adds an average of 12 ms per request; the total additional latency observed in the prototype was about 45 ms, well within acceptable limits for modern web services. Memory overhead is minimal (a temporary hash table per session). The approach scales to multi‑server deployments by sharing the same CSPRNG seed generation logic or by delegating mapping creation to a dedicated microservice.
The authors acknowledge limitations: the visible mapping may be problematic for visually impaired users, and the cognitive load of translating passwords to digits could become burdensome for long passwords. They suggest future work such as multi‑digit or alphanumeric mappings, adaptive UI for accessibility, and integration with multi‑factor authentication frameworks.
In conclusion, the paper introduces a novel paradigm where the login interface itself becomes a dynamic, per‑character one‑time pad. By regenerating a random digit for every possible password character after each keystroke, the scheme dramatically raises the bar for both online and offline attackers while imposing only modest usability and performance costs. The prototype demonstrates that the method is practical and could be deployed as an additional security layer for high‑risk applications (banking, healthcare, etc.) or even as a replacement for traditional password entry in environments where heightened security is paramount.
Comments & Academic Discussion
Loading comments...
Leave a Comment