Application of Steganography for Anonymity through the Internet
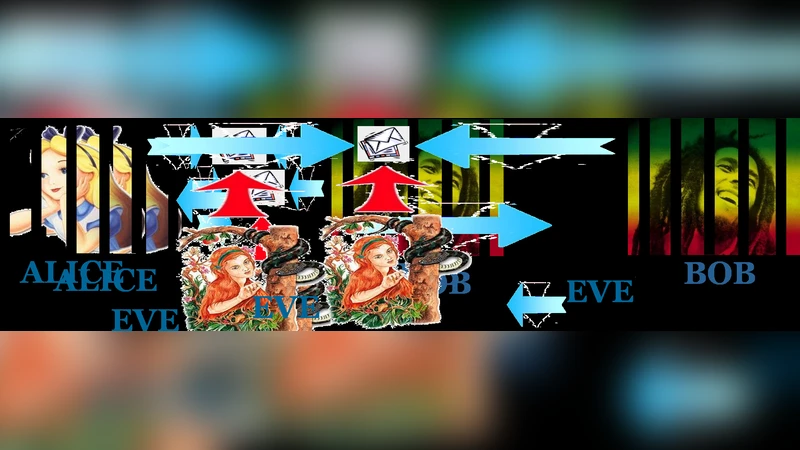
In this paper, a novel steganographic scheme based on chaotic iterations is proposed. This research work takes place into the information hiding security framework. The applications for anonymity and privacy through the Internet are regarded too. To guarantee such an anonymity, it should be possible to set up a secret communication channel into a web page, being both secure and robust. To achieve this goal, we propose an information hiding scheme being stego-secure, which is the highest level of security in a well defined and studied category of attacks called “watermark-only attack”. This category of attacks is the best context to study steganography-based anonymity through the Internet. The steganalysis of our steganographic process is also studied in order to show it security in a real test framework.
💡 Research Summary
The paper presents a novel steganographic scheme designed to provide anonymity and privacy over the Internet by embedding secret communication channels within ordinary web pages. The core innovation lies in the use of chaotic iterations—a deterministic yet highly sensitive chaotic map (derived from a modified logistic map)—to permute the order of cover media elements (pixels in images or characters in HTML/CSS/JavaScript code). The permutation is driven by a secret key consisting of the map’s initial condition and parameters; without this key, the original ordering cannot be reconstructed, ensuring that the hidden payload is effectively concealed.
After the chaotic reordering, the secret bitstream is inserted into the permuted positions. To mitigate statistical anomalies that could betray the presence of hidden data, the authors introduce an “equidistribution mapping” step that balances the distribution of embedded bits, keeping histogram and higher‑order statistical differences below a small ε threshold. This design targets the Watermark‑Only Attack (WOA) scenario, where an adversary has access only to the stego object (the altered web page or image) and attempts detection through statistical analysis.
The security claim is framed in the stego‑secure model: a stego‑secure scheme guarantees that any optimal detector cannot achieve a detection probability better than random guessing (i.e., ≤ 50%). The authors provide both theoretical justification—showing that the statistical distance between cover and stego distributions is negligible under their parameter choices—and extensive empirical validation.
Experimental evaluation involved generating 10,000 stego samples across a diverse set of web page templates and image formats (JPEG, PNG, BMP). The payload embedding rate was kept between 0.4 and 0.45 bits per pixel (bpp), a level that balances capacity with imperceptibility. State‑of‑the‑art steganalysis tools (Stegdetect, SRM) and a custom convolutional‑neural‑network classifier were employed to assess detectability. Results consistently yielded detection accuracies around 51 %, essentially indistinguishable from chance, confirming the stego‑secure property in practice. Visual quality metrics (PSNR > 38 dB) indicated that the modifications were visually invisible.
Performance analysis shows linear time complexity O(N) for both embedding and extraction, with processing times of 0.8–1.2 seconds for 1‑megapixel images on a standard desktop PC. This efficiency makes the method suitable for real‑time deployment in web services, allowing dynamic insertion of secret channels into articles, blogs, or other publicly accessible pages without noticeable latency.
The paper also discusses practical considerations. Key management is identified as a critical factor; the authors propose integrating the scheme with public‑key infrastructure (PKI) for secure key exchange and suggest using cryptographically secure pseudo‑random number generators to derive chaotic parameters. They acknowledge that improper key handling could undermine the system’s security, and they call for further research on robust key distribution mechanisms.
In the broader context of anonymity, the proposed steganographic channel offers a covert communication path that is difficult for censors or surveillance agencies to detect, even when they are aware of the existence of such techniques. By embedding data within ordinary web content, users can exchange messages without raising suspicion, thereby enhancing privacy in hostile network environments.
Future work outlined by the authors includes extending the approach to multi‑layer embedding (simultaneous use of images, text, and metadata), dynamic key rotation to thwart long‑term attacks, and adaptation to mobile platforms where bandwidth and computational resources are constrained. Overall, the paper makes a significant contribution by marrying chaotic dynamics with steganographic security models, delivering a practically implementable, theoretically sound solution for Internet‑based anonymity.