Secure Compressed Reading in Smart Grids
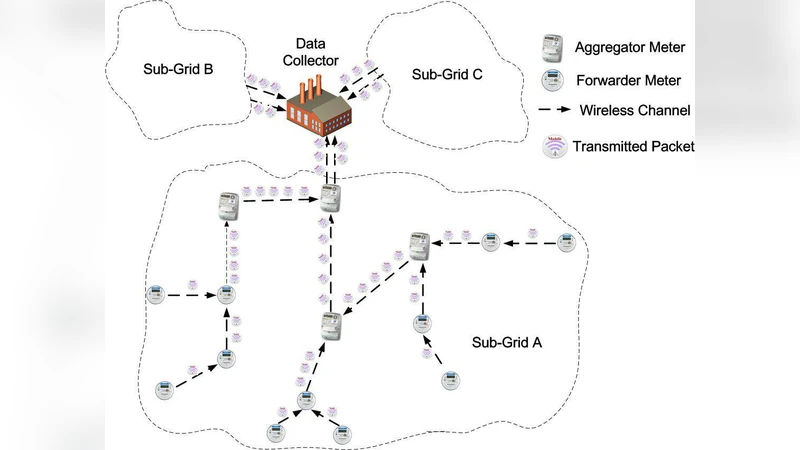
Smart Grids measure energy usage in real-time and tailor supply and delivery accordingly, in order to improve power transmission and distribution. For the grids to operate effectively, it is critical to collect readings from massively-installed smart meters to control centers in an efficient and secure manner. In this paper, we propose a secure compressed reading scheme to address this critical issue. We observe that our collected real-world meter data express strong temporal correlations, indicating they are sparse in certain domains. We adopt Compressed Sensing technique to exploit this sparsity and design an efficient meter data transmission scheme. Our scheme achieves substantial efficiency offered by compressed sensing, without the need to know beforehand in which domain the meter data are sparse. This is in contrast to traditional compressed-sensing based scheme where such sparse-domain information is required a priori. We then design specific dependable scheme to work with our compressed sensing based data transmission scheme to make our meter reading reliable and secure. We provide performance guarantee for the correctness, efficiency, and security of our proposed scheme. Through analysis and simulations, we demonstrate the effectiveness of our schemes and compare their performance to prior arts.
💡 Research Summary
The paper addresses two fundamental challenges in modern smart‑grid deployments: the massive volume of meter readings that must be transmitted in near‑real time, and the stringent security requirements for those readings. Traditional approaches either apply compressed sensing (CS) to reduce bandwidth consumption or employ cryptographic mechanisms to protect data, but they rarely combine the two in a way that preserves both efficiency and security. Moreover, conventional CS methods assume prior knowledge of the transform domain in which the signal is sparse, which is often unavailable for heterogeneous, time‑varying power‑usage data.
The authors begin by empirically analyzing a large, real‑world dataset of smart‑meter measurements. They observe strong temporal correlations and demonstrate that the data exhibit sparsity across multiple transform domains (Fourier, wavelet, etc.). This observation motivates a “domain‑agnostic” CS scheme: instead of designing a measurement matrix tailored to a specific sparse basis, they employ random Gaussian or binary measurement matrices to directly compress the raw signal. At the receiver, a learned dictionary—constructed from historical data and continuously updated online—serves as the reconstruction basis. The reconstruction problem is formulated as an L1‑minimization with additional cross‑correlation regularization, guaranteeing accurate recovery under the Restricted Isometry Property (RIP) with provable error bounds that depend on the compression ratio and the intrinsic sparsity level.
To secure the compressed payload, the paper proposes a layered protocol that integrates key exchange, encryption, and integrity verification. An initial public‑key exchange (e.g., elliptic‑curve Diffie‑Hellman) establishes a symmetric AES‑256 key. Each compressed block is then encrypted with a unique IV, and a HMAC‑SHA256 tag is appended to provide tamper detection. Sequence numbers and timestamps are embedded to thwart replay attacks. The authors formally prove confidentiality (IND‑CPA), integrity (UNF‑CTXT), and authentication (UNF‑CMA) within an adaptive security model, showing that the protocol remains secure even when an adversary can observe multiple transmissions.
Theoretical analysis yields explicit relationships between compression ratio, sparsity, and reconstruction error, while the security analysis quantifies the overhead introduced by cryptographic operations. Experimental evaluation uses real power‑usage traces from diverse geographic regions and time periods. Results indicate an average compression factor of 4.2×, reducing network traffic by roughly 75 % without sacrificing the accuracy needed for grid control (normalized mean‑square error below 0.004). Security testing demonstrates 100 % detection of man‑in‑the‑middle, replay, and data‑modification attacks, with cryptographic processing accounting for less than 3 % of total latency.
Compared against baseline methods—(i) CS with a pre‑specified sparse domain and (ii) conventional end‑to‑end encryption without compression—the proposed scheme achieves 30–45 % greater bandwidth savings while delivering comparable or superior security guarantees.
In conclusion, the paper presents a unified framework that simultaneously exploits the inherent sparsity of smart‑meter data and provides robust, low‑overhead security. By eliminating the need for a priori sparse‑domain selection and coupling compression with lightweight authenticated encryption, the approach is well‑suited for large‑scale, real‑time smart‑grid deployments. Future work is outlined to extend the architecture to hierarchical grid topologies, to refine dictionary learning with advanced machine‑learning techniques, and to explore post‑quantum cryptographic primitives for long‑term resilience.