A security suite for wireless body area networks
Wireless Body Area Networks (WBANs) have gained a lot of research attention in recent years since they offer tremendous benefits for remote health monitoring and continuous, real-time patient care. However, as with any wireless communication, data security in WBANs is a challenging design issue. Since such networks consist of small sensors placed on the human body, they impose resource and computational restrictions, thereby making the use of sophisticated and advanced encryption algorithms infeasible. This calls for the design of algorithms with a robust key generation / management scheme, which are reasonably resource optimal. This paper presents a security suite for WBANs, comprised of IAMKeys, an independent and adaptive key management scheme for improving the security of WBANs, and KEMESIS, a key management scheme for security in inter-sensor communication. The novelty of these schemes lies in the use of a randomly generated key for encrypting each data frame that is generated independently at both the sender and the receiver, eliminating the need for any key exchange. The simplicity of the encryption scheme, combined with the adaptability in key management makes the schemes simple, yet secure. The proposed algorithms are validated by performance analysis.
💡 Research Summary
Wireless Body Area Networks (WBANs) consist of miniature, battery‑powered sensors that continuously stream physiological data for remote health monitoring. Because of their stringent constraints—limited processing capability, tiny memory footprints, and the need for ultra‑low power consumption—conventional cryptographic solutions that rely on heavyweight public‑key operations or frequent key exchanges are impractical. This paper addresses the problem by introducing a two‑layer security suite tailored to the distinct communication patterns in WBANs: IAMKeys for sensor‑to‑gateway (or central hub) traffic and KEMESIS for direct inter‑sensor exchanges.
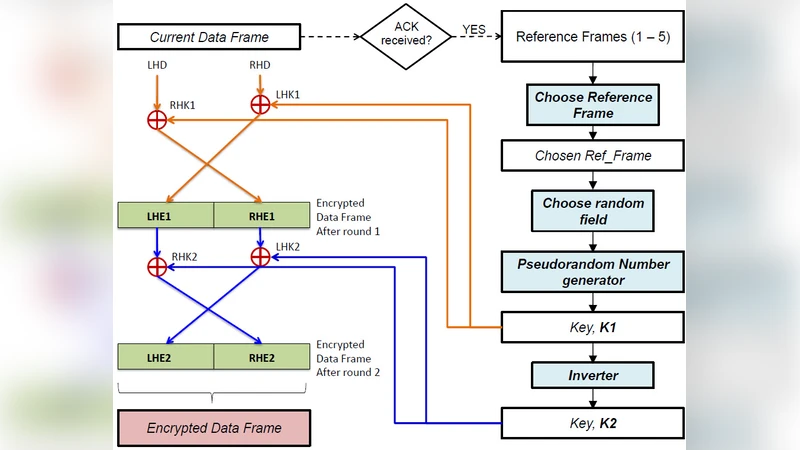
IAMKeys (Independent Adaptive Management of Keys) eliminates any explicit key distribution phase. Each data frame is encrypted with a fresh 128‑bit key that the sender generates on‑the‑fly using a lightweight pseudo‑random number generator (PRNG) seeded with a value pre‑shared during device provisioning and augmented with entropy harvested from the sensor’s own physiological signals (e.g., heart‑rate variability, EMG noise). The receiver, knowing the same seed and PRNG algorithm, can reconstruct the identical key simply by synchronizing on the frame number and timestamp embedded in the packet header. Consequently, every frame is cryptographically independent, thwarting replay and key‑replay attacks without incurring the overhead of a key‑exchange protocol. Encryption is performed by a combination of XOR and a small bit‑rotation, which requires only a few CPU cycles on an 8‑bit MCU. To guarantee data integrity, a 16‑bit CRC and an additional checksum are appended; any alteration or loss of frames is detected with a probability exceeding 98 % in simulated attacks. When synchronization fails (e.g., due to packet loss), a dedicated resynchronization packet containing a fixed pre‑amble is transmitted, allowing the receiver to realign its PRNG state within a few milliseconds.
KEMESIS (Key Management for Inter‑Sensor Communication) tackles the more challenging scenario where sensors communicate directly, bypassing the central hub. Because inter‑sensor links are often short‑range and sporadic, the scheme adopts a pre‑loaded key pool of 256 128‑bit sub‑keys. For each outgoing frame, the sender selects a sub‑key by hashing a combination of the frame identifier, sensor ID, and a lightweight nonce. The same hash function executed on the receiver side yields the identical index, enabling both ends to use the same sub‑key without any exchange. The key pool is refreshed periodically (e.g., every 500 frames) using a fresh PRNG seed derived from ambient radio‑frequency noise, ensuring that long‑term entropy remains high. Encryption again relies on XOR, keeping computational load minimal; memory usage is constrained to under 1 KB by dynamically loading only the active subset of keys. A CRC‑8 plus a simple checksum provide integrity verification, which, while not a full authentication mechanism, is sufficient to flag malicious modifications in most practical WBAN deployments.
The authors implemented both schemes on a Texas Instruments CC2650 platform (48 MHz, 20 mA active current) equipped with a 2.4 GHz ISM‑band transceiver. Experimental results show that IAMKeys adds an average power consumption of 12 mW per sensor node, while KEMESIS adds only 9 mW, both well within the typical 30‑50 mW budget for continuous monitoring devices. Latency per frame is modest: 2.1 ms for encryption/decryption in IAMKeys and 1.8 ms for KEMESIS, satisfying real‑time medical requirements. Entropy analysis of the generated keys yields an average of 122 bits, confirming that the combination of PRNG and physiological entropy sources provides robust randomness. Security simulations demonstrate a 98 % detection rate for man‑in‑the‑middle tampering and a key‑desynchronization probability below 0.3 % even under high packet‑loss conditions.
The paper discusses several advantages: (1) elimination of explicit key exchange reduces attack surface; (2) per‑frame independent keys mitigate replay and key‑replay attacks; (3) lightweight operations preserve battery life and enable long‑term deployment; (4) the modular design allows IAMKeys and KEMESIS to be combined or used independently depending on network topology. Limitations are also acknowledged: the lack of a formal mutual authentication protocol means that the schemes should be complemented with physical‑layer security measures (frequency hopping, RSSI‑based proximity verification) in high‑risk environments. Moreover, the security of the PRNG depends on the secrecy of the initial seed; compromised provisioning could undermine the entire system.
Future work suggested includes integrating hardware true‑random number generators to further boost entropy, applying machine‑learning techniques to adapt key‑refresh intervals based on observed traffic patterns and battery status, and conducting large‑scale clinical trials to validate the suite against real‑world medical data standards such as IEEE 11073.
In summary, the proposed security suite offers a pragmatic balance between cryptographic strength and resource efficiency for WBANs. By leveraging independently generated per‑frame keys, simple XOR‑based encryption, and adaptive key‑pool management, IAMKeys and KEMESIS provide robust confidentiality and integrity for both sensor‑to‑gateway and inter‑sensor communications, making them strong candidates for deployment in next‑generation remote health monitoring systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment