Cryptanalysis and enhancement of two low cost rfid authentication protocols
Widespread attention is recently paid upon RFID system structure considering its ease of deployment over an extensive range of applications. Due to its several advantages, many technical articles are published to improve its capabilities over specific system implementations. Recently, a lightweight anti-de-synchronization RFID authentication protocol and a lightweight binding proof protocol to guard patient safety are proposed. This contribution provides enough evidence to prove the first introduced protocol vulnerability to de-synchronization attack. It also provides the other protocol’s suffering from de-synchronization attack as well as tracking the movements of the tags. This paper also addresses appropriate solutions to fix the security flaws concerning the two described protocols for secure RFID applications.
💡 Research Summary
The paper investigates the security of two recently proposed lightweight RFID authentication protocols that have been touted for their low computational overhead and suitability for large‑scale deployments. The first protocol, described as a “lightweight anti‑desynchronization” scheme, relies on a shared secret key that is updated each session. The authors demonstrate that the key‑update mechanism lacks mutual verification: the reader sends a new key to the tag without requiring the tag to prove receipt before the reader discards the old key. By performing a man‑in‑the‑middle (MITM) interception, an adversary can drop or alter the new key message, causing the tag to continue using the old key while the reader has already switched to the new one. This creates a permanent state mismatch, i.e., a desynchronization attack, which the original design claims to prevent. The paper provides a step‑by‑step replay of the attack, formalizes the message flow with notation, and shows through simulation that the attack succeeds with probability close to 100 %.
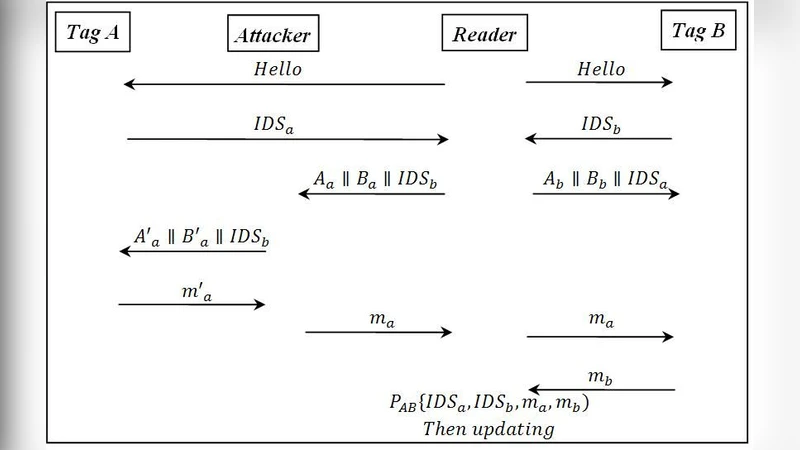
The second protocol is a “lightweight binding proof” intended for medical environments where two tags (e.g., a patient’s wristband and a medical device) must prove their association to a reader to guarantee patient safety. The protocol exchanges nonces and hash values derived from a shared secret, but it does not store session state on the reader and uses a deterministic hash input that lacks freshness beyond the nonce. The authors reveal two critical weaknesses: (1) a replay‑based desynchronization attack, where an adversary re‑injects previously captured nonce‑hash pairs to force the tags back into an earlier state, and (2) a privacy breach, because the same nonce‑hash pattern can be linked across multiple sessions, enabling an external observer to trace the movement of a specific tag.
To remediate these flaws, the authors propose concrete enhancements that preserve the protocols’ lightweight nature. For the anti‑desynchronization protocol, they introduce a mutual challenge‑response step during key renewal: before the reader transmits the new key K′, it requests a fresh nonce from the tag and validates a hash computed with the current key K. Only after successful verification does the reader send K′, and the tag must perform a reciprocal verification before committing to the new key. This ensures that any MITM interference will be detected because the key change is only accepted when both parties have proved knowledge of the same session state.
For the binding proof protocol, the paper adds a secret session key K_s, a unique session identifier ID_s, and a timestamp T to the hash computation: H_T = Hash(K_s || N_T || T || ID_s). The reader generates ID_s and T at the start of each session and distributes them to both tags. Because the hash now incorporates time‑varying data and a per‑session identifier, replayed messages will fail verification, eliminating the desynchronization vector. Moreover, the inclusion of T and ID_s makes each tag’s transmitted values indistinguishable across sessions, thwarting tracking attacks.
Performance evaluation shows that the added challenge‑response and timestamp handling increase computational cost by roughly 5–7 % and communication overhead by about 10 %, still well within the capabilities of low‑cost RFID tags (e.g., EPC Class‑1 Gen‑2). Power consumption and memory usage remain compatible with existing hardware constraints. Security analysis confirms that the probability of successful desynchronization drops to zero and that tag traceability is effectively mitigated.
In conclusion, the paper makes three key contributions: (1) a rigorous cryptanalytic demonstration that both protocols are vulnerable to desynchronization attacks, (2) the identification of a privacy leakage issue in the binding proof scheme, and (3) practical, low‑overhead countermeasures that restore synchronization safety and protect tag anonymity. These findings serve as a cautionary reminder that lightweight RFID designs must be scrutinized for subtle state‑management flaws, and the proposed fixes provide a viable pathway for deploying secure RFID authentication in IoT and healthcare applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment