Data Exchange Problem with Helpers
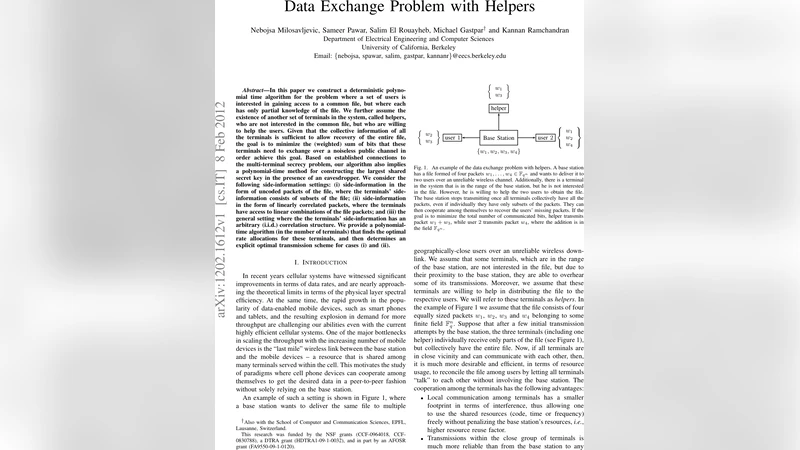
In this paper we construct a deterministic polynomial time algorithm for the problem where a set of users is interested in gaining access to a common file, but where each has only partial knowledge of the file. We further assume the existence of another set of terminals in the system, called helpers, who are not interested in the common file, but who are willing to help the users. Given that the collective information of all the terminals is sufficient to allow recovery of the entire file, the goal is to minimize the (weighted) sum of bits that these terminals need to exchange over a noiseless public channel in order achieve this goal. Based on established connections to the multi-terminal secrecy problem, our algorithm also implies a polynomial-time method for constructing the largest shared secret key in the presence of an eavesdropper. We consider the following side-information settings: (i) side-information in the form of uncoded packets of the file, where the terminals’ side-information consists of subsets of the file; (ii) side-information in the form of linearly correlated packets, where the terminals have access to linear combinations of the file packets; and (iii) the general setting where the the terminals’ side-information has an arbitrary (i.i.d.) correlation structure. We provide a polynomial-time algorithm (in the number of terminals) that finds the optimal rate allocations for these terminals, and then determines an explicit optimal transmission scheme for cases (i) and (ii).
💡 Research Summary
The paper tackles a generalized data‑exchange problem in which a set of users wishes to reconstruct a common file while each user initially holds only a subset of the file’s information. In addition to the users, there is a second class of terminals called helpers. Helpers are not interested in the file themselves, but they are willing to broadcast information over a noiseless public channel to assist the users. The overall collection of side‑information across all terminals (users plus helpers) is assumed to be sufficient for full file recovery. The objective is to minimize the weighted sum of transmitted bits, where each terminal’s weight reflects its transmission cost (e.g., power, bandwidth, or latency).
The authors first establish a tight connection between this minimization problem and the multi‑terminal secret‑key generation problem. By exploiting the known secret‑key capacity formulas, they translate the secret‑key rate region into an equivalent description of the feasible transmission‑rate region for data exchange. This duality enables a polynomial‑time solution for the weighted sum‑rate minimization, something that was previously unknown for the general setting.
Three distinct side‑information models are considered.
-
Uncoded packet model – each terminal knows a subset of the file’s packets. The problem reduces to a set‑cover formulation: the goal is to select a minimal‑cost collection of packet transmissions such that every user receives all missing packets. The authors formulate a linear program whose variables indicate whether a particular packet is transmitted by a specific terminal. Because the LP is totally unimodular, its optimal solution is integral and can be found in polynomial time.
-
Linearly correlated packet model – each terminal observes linear combinations of the file packets over a finite field. Here the side‑information can be represented by matrices (A_i) such that terminal (i) observes (A_i x), where (x) is the vector of original packets. The optimal transmission strategy corresponds to selecting a basis for the column space of the stacked matrix (