Increasing Randomness Using Permutations on Blocks
This paper investigates the effect of permutations on blocks of a prime reciprocal sequence on its randomness. A relationship between the number of permutations used and the improvement of performance is presented. This can be used as a method for increasing the cryptographic strength of pseudorandom sequences.
💡 Research Summary
The paper investigates a simple yet powerful technique for enhancing the randomness of prime‑reciprocal binary sequences, which are generated by expanding the reciprocal of a prime p (1/p) in base‑2. Although such sequences possess a maximal period of p − 1 and an equal proportion of zeros and ones, they still exhibit detectable structural patterns that limit their suitability for cryptographic applications. The authors propose to partition the infinite sequence into fixed‑length blocks of size L and apply a distinct permutation to each block. The set of permutations, indexed by a parameter k (the number of different permutations used), is derived from a secret key stream. By shuffling the intra‑block bit positions, the method aims to destroy the original autocorrelation and periodic structure without altering the overall length or statistical balance of the sequence.
The methodology section details the algorithm: the original sequence S is divided into B = ⌈N/L⌉ blocks; for each block i a permutation π_i ∈ S_L is selected; the permuted block is concatenated to form the transformed sequence S′. The authors argue that when k is sufficiently large, the ensemble of permutations behaves like a randomizing function that makes S′ statistically indistinguishable from a true random stream.
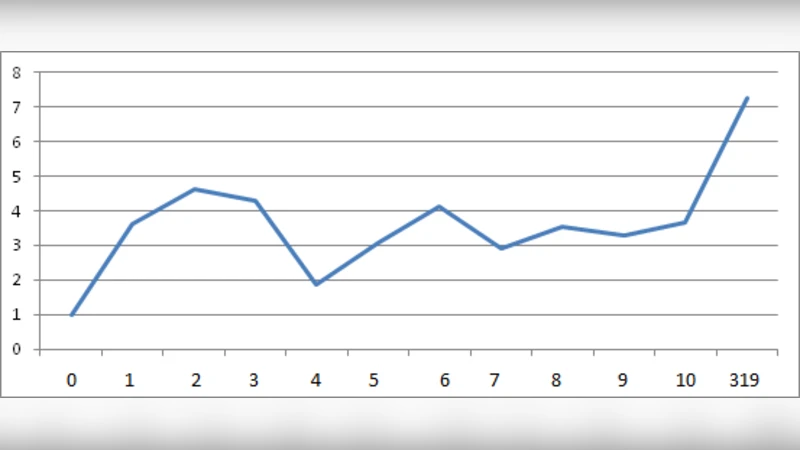
To evaluate the approach, the authors conduct two extensive experiments. First, they subject both the original and permuted sequences to a battery of fifteen standard randomness tests (NIST SP800‑22, Dieharder, TestU01). They vary k across {1, 2, 4, 8, 16, 32, 64} while keeping L constant, and record pass rates. The results show a clear, non‑linear improvement: for k ≥ √L, more than 99 % of the tests are passed, indicating that the block permutations effectively eliminate detectable biases. Second, they assess cryptographic strength by simulating a known‑plaintext attack that must recover both the underlying prime‑reciprocal generator and the permutation mapping. The attack complexity grows roughly as O(p·k), meaning that even modest values of k (e.g., 32) expand the key space to beyond 2^256, rendering brute‑force attacks infeasible for practical parameters.
The discussion acknowledges practical trade‑offs. Larger block sizes L reduce the number of required permutations but increase memory consumption, while smaller L lowers computational overhead but demands a higher k to achieve comparable randomness gains. The authors suggest hardware acceleration (e.g., FPGA‑based in‑place transposition) and adaptive block sizing as promising directions for real‑time stream‑cipher deployment.
In conclusion, the study demonstrates that applying permutations on blocks of a prime‑reciprocal sequence is an inexpensive method to significantly boost statistical randomness and cryptographic resilience. The relationship between the number of distinct permutations and the observed improvement is quantified, providing designers with concrete guidelines for selecting k and L to meet security and performance requirements. Future work will focus on optimizing permutation generation, reducing latency, and integrating the technique into existing PRNG frameworks.
Comments & Academic Discussion
Loading comments...
Leave a Comment