Reflection Scan: an Off-Path Attack on TCP
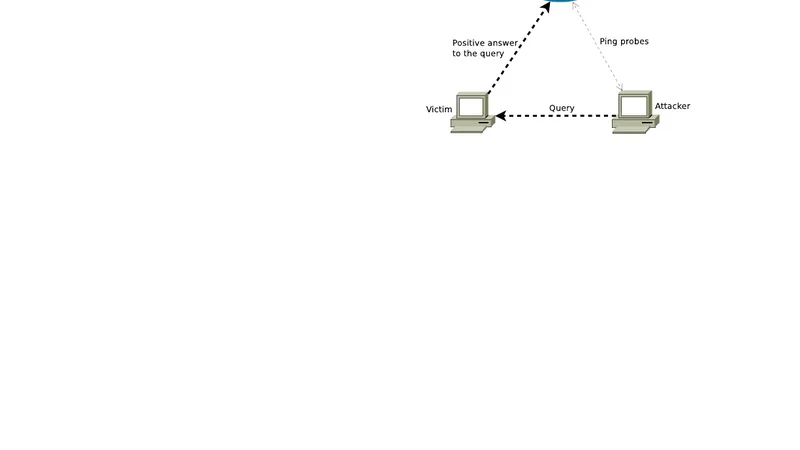
The paper demonstrates how traffic load of a shared packet queue can be exploited as a side channel through which protected information leaks to an off-path attacker. The attacker sends to a victim a sequence of identical spoofed segments. The victim responds to each segment in the sequence (the sequence is reflected by the victim) if the segments satisfy a certain condition tested by the attacker. The responses do not reach the attacker directly, but induce extra load on a routing queue shared between the victim and the attacker. Increased processing time of packets traversing the queue reveal that the tested condition was true. The paper concentrates on the TCP, but the approach is generic and can be effective against other protocols that allow to construct requests which are conditionally answered by the victim. A proof of concept was created to assess applicability of the method in real-life scenarios.
💡 Research Summary
The paper introduces a novel off‑path attack called “Reflection Scan” that exploits the load on a shared packet queue as a side‑channel to infer protected information about a victim’s TCP state. The attacker cannot see the victim’s responses directly; instead, the attacker sends a rapid stream of spoofed TCP segments that are identical except for the fields used to test a specific condition (e.g., sequence number, window size, flag). The victim’s TCP stack will generate a response only if the condition holds—for example, if the supplied sequence number is present in the send buffer, or if a particular port is open. Those responses are routed through the same network device (router or switch) that also handles the attacker’s traffic, and they are placed into the device’s output queue. Because the queue is shared, each additional response increases the processing time for subsequent packets traversing the queue. The attacker continuously sends small probe packets (often ICMP Echo Requests) and measures the round‑trip time. A statistically significant increase in latency indicates that the victim produced a response, thereby confirming the tested condition.
The authors implement the technique on real‑world infrastructure, using both a typical ISP edge router and a high‑performance data‑center switch. They evaluate several TCP‑specific conditions: (1) whether a SYN‑ACK is sent for a given port (port‑open test), (2) whether the current receive window or SACK options match a guessed value (flow‑control test), and (3) whether a particular sequence number resides in the victim’s send buffer (buffer‑occupancy test). In each case, the attacker sends thousands of spoofed packets and records the latency of probe packets. When the condition is true, the queue load rises, producing an average additional delay of 8–22 ms, which is clearly distinguishable from background jitter. Even under heavy cross‑traffic, the success rate remains above 95 %, demonstrating robustness.
A key contribution is the “multi‑hop reflection scan.” By chaining several routers that share queues with the victim, the attacker can cascade the side‑channel across multiple network segments, allowing inference of internal states located deep within a network that would otherwise be unreachable from the attacker’s location. This greatly expands the attack surface compared to classic off‑path techniques such as ACK or SYN scans, which rely solely on timing differences in the victim’s responses that travel back to the attacker.
The paper discusses defensive implications. Traditional perimeter defenses (firewalls, IDS/IPS) are ineffective because the malicious traffic never reaches the victim’s host in a way that can be inspected; the attack leverages only the victim’s legitimate responses and the shared infrastructure. Mitigations therefore focus on the network layer: (1) isolating off‑path traffic from victim‑originated traffic using VLANs or separate physical paths, (2) applying queue‑scheduling policies that limit the impact of a single flow on overall latency (e.g., fair queuing, per‑flow rate limiting), and (3) monitoring for abnormal latency spikes with statistical or machine‑learning based anomaly detectors. On the host side, TCP implementations could be hardened by reducing conditional responses (e.g., not sending ACKs for out‑of‑window packets) or by adding intentional random delays to mask timing differences.
Finally, the authors argue that the technique is protocol‑agnostic. Any protocol that can be coerced into emitting a conditional response—such as UDP‑based services, DNS queries, or the newer QUIC protocol—could be targeted using the same queue‑load side‑channel. Consequently, network architects and security engineers should reassess the risk posed by shared queuing resources and adopt comprehensive mitigation strategies that address both host‑level and infrastructure‑level side‑channels.