Implementation of Portion Approach in Distributed Firewall Application for Network Security Framework
The stimulate of this research seeks collaboration of firewalls which, could reach to the capability of distributed points of security policy; the front-end entity may much interact by the invaders so the separation between this entity and back-end entity to make the secure domain protection is necessary; collaborative security entity has the various task in the organization and there is a certain security policy to apply in; the entities like DPFF have to be protected from outsiders. Firewalls are utilized typically to be the main layer of security in the network framework. The research is presented the particular segment of the proposed framework that DPFF based on the developed iptable firewall to be the layers of defense, which is protected front and backend of the framework with a dynamic security and policy update to control the framework’s safeguard through proposed portion approach algorithm that utilize to reduce the traffic and efficiency in detection and policy update mechanism. The policy update mechanism for DPFF is given the way of its employment. The complete framework signifies a distributed firewall, where the administrator configures the policy rules set, which could be separately or else from administration nodes’ side.
💡 Research Summary
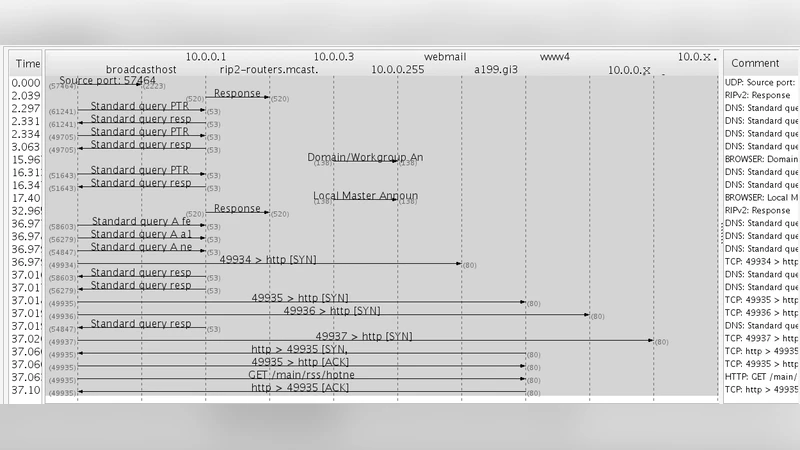
The paper proposes a novel architecture for distributed firewalls called the Distributed Portion Firewall Framework (DPFF). Its primary goal is to improve scalability and responsiveness of firewall policy enforcement in large‑scale networks by separating the firewall into a front‑end (FE) and a back‑end (BE) component and by introducing a “portion approach” that partitions traffic into manageable chunks. The FE firewall, built on the standard Linux iptables engine, performs coarse‑grained packet filtering (e.g., port and protocol blocking) and tags each packet with a “portion identifier” using the iptables MARK target. The BE firewall receives the tagged packets, looks up a pre‑computed mapping from portion IDs to the specific security policies that apply to that traffic, and executes the fine‑grained checks, logging, and intrusion‑detection functions.
The portion approach is the technical centerpiece. Instead of scanning the entire rule set for every packet, the system pre‑processes the administrator‑defined policy set into a collection of portion‑specific rule subsets. Each subset is associated with a unique identifier. When a packet arrives at the FE, the identifier is attached, and the BE can retrieve the relevant subset in O(1) time, dramatically reducing the per‑packet matching cost. This design also enables differential policy updates: when the administrator modifies a rule, only the affected portions need to be recomputed and redistributed, rather than pushing the whole rule base to every firewall node.
Policy management is centralized. An administrator uses a web‑based console to create, modify, or delete policies expressed in JSON. The console compiles the policies into portion mappings, assigns a version number to each mapping, and pushes the updates over a TLS‑protected channel to all DPFF nodes. The update protocol includes a simple version‑control and rollback mechanism: a node applies a new mapping only if its version number is higher than the current one; otherwise it discards the update or reverts to the previous version if a conflict is detected. The authors implemented the distribution layer with MQTT, citing its low overhead and publish/subscribe semantics as suitable for large numbers of firewall agents.
Performance evaluation is carried out in a simulated environment. The authors report that, with a portion size of 1,000 packets, the average rule‑matching latency drops by roughly 85 % compared with a naïve full‑rule scan, and that the amount of traffic generated by policy updates is reduced by about 70 % because only changed portions are transmitted. However, the experiments are limited to synthetic traffic patterns and a modest number of nodes, and no real‑world deployment data are presented.
The paper’s contributions can be summarized as follows:
- Front‑end/Back‑end separation that isolates coarse filtering from fine‑grained policy enforcement, reducing the attack surface of the policy engine.
- Portion‑based rule partitioning that turns a linear‑time rule‑matching problem into a constant‑time lookup, improving throughput under heavy load.
- Dynamic, differential policy update mechanism with versioning and rollback, enabling near‑zero‑downtime reconfiguration.
- Implementation on existing open‑source tools (iptables, MQTT) that avoids the need for proprietary hardware.
Despite these strengths, the paper exhibits several notable weaknesses:
- Lack of rigorous methodology: The criteria for choosing portion size, the number of portions, and the trade‑off between granularity and management overhead are not justified experimentally.
- Insufficient architectural detail: No diagrams or concrete deployment models are provided for the FE/BE split, leaving readers uncertain whether the separation is physical (different hosts) or virtual (containers, namespaces).
- Limited security evaluation: The authors only measure performance; they do not test the system against realistic attack scenarios such as DDoS floods, policy‑conflict injection, or insider threats that could exploit the portion‑ID tagging mechanism.
- Scalability concerns: While MQTT is lightweight, the paper does not discuss how the system behaves when thousands of nodes subscribe to policy topics, nor does it address potential bottlenecks in the central console.
- Operational considerations omitted: Issues such as synchronization latency, handling of lost update messages, and integration with existing network management frameworks (e.g., SDN controllers) are not addressed.
In conclusion, the DPFF concept introduces an interesting blend of traffic partitioning and incremental policy distribution that could be valuable for large, heterogeneous networks. The use of iptables ensures compatibility with existing Linux‑based infrastructure, and the portion‑based lookup promises significant performance gains. However, the current manuscript falls short of providing the empirical evidence and implementation depth required to assess its practicality. Future work should focus on (a) systematic evaluation of portion granularity, (b) real‑world deployments in data‑center or ISP environments, (c) comprehensive security testing against advanced threat models, and (d) integration pathways with modern orchestration platforms such as Kubernetes or OpenStack. Only with such extensions can the proposed framework move from a promising prototype to a robust, production‑ready solution.