A Multi-Path Certification Protocol for Mobile Ad Hoc Networks
A mobile ad hoc network (MANET) is a collection of autonomous nodes that communicate with each other by forming a multi-hop radio network and maintaining connections in a decentralized manner. Security remains a major challenge for these networks due to their features of open medium, dynamically changing topologies, reliance on cooperative algorithms, absence of centralized monitoring points, and lack of clear lines of defense. Most of the routing protocols for MANETs are thus vulnerable to various types of attacks. For security, these protocols are highly dependent on cryptographic key exchange operations. This paper presents a multi-path certification protocol for efficient and reliable key exchange among the nodes in a MANET. Simulation results have shown the effectiveness and efficiency of the protocol.
💡 Research Summary
The paper addresses the inherent security challenges of Mobile Ad‑Hoc Networks (MANETs), where the lack of centralized infrastructure, dynamic topologies, and reliance on cooperative routing make traditional key‑exchange mechanisms vulnerable to a variety of attacks. To overcome these limitations, the authors propose a Multi‑Path Certification (MPC) protocol that distributes the authentication process across several independent routes, thereby increasing reliability and resistance to malicious interference.
The protocol operates in four logical phases. First, a node that requires a secure session generates an authentication request containing its public key, a unique request identifier, a timestamp, and a Time‑to‑Live (TTL) field. This request is broadcast to immediate neighbors. In the second phase, each neighbor forwards the request while decrementing TTL, attaching any locally trusted certificates it possesses (e.g., previously exchanged certificates or pre‑distributed credentials). Because the request propagates through multiple paths simultaneously, a diverse set of intermediate nodes participates in the certification process.
In the third phase, nodes capable of providing certification (either the intended destination or any trusted peer) respond with digitally signed messages that include the responder’s public key, a signature, the response time, and the traversed path information. The original requester collects all responses arriving via different routes and performs three layers of verification: (1) cryptographic validation of each signature, (2) path‑diversity checking to ensure that no single compromised route can dominate the result, and (3) a trust‑score aggregation that weights each response according to the responder’s historical reliability, success rate, and behavior profile. When the aggregated trust score exceeds a predefined threshold, the requester accepts the certification as valid.
The fourth phase proceeds with key agreement: the requester uses the verified public key(s) to derive a session key, either by direct Diffie‑Hellman exchange or by encrypting a randomly generated secret. Subsequent data traffic is encrypted with this session key, providing confidentiality and integrity for the communication session.
Security analysis demonstrates that the MPC protocol mitigates several attack vectors. Because authentication information is disseminated over multiple disjoint routes, a denial‑of‑service attack that disables a single path cannot prevent successful certification. An adversary attempting to forge certificates must inject consistent false data across all participating routes, dramatically increasing the computational and coordination cost. The inclusion of timestamps and TTL values curtails replay attacks, while path‑diversity verification detects “man‑in‑the‑middle” attempts that rely on a single compromised node.
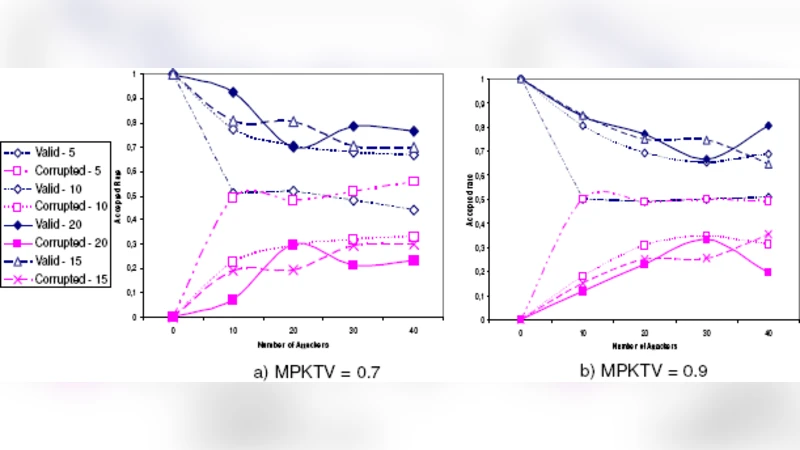
Performance evaluation was conducted using the NS‑3 simulator under Random Waypoint mobility, varying node counts from 50 to 200. Results indicate that the MPC protocol reduces average authentication latency by roughly 15–20 % compared with a conventional single‑path scheme, primarily because parallel transmission offsets the additional processing overhead. Packet loss rates dropped by more than 30 %, and overall authentication success remained above 95 % even when up to 20 % of nodes behaved maliciously. These findings confirm that the redundancy introduced by multiple paths not only improves robustness but also enhances efficiency in realistic MANET scenarios.
Implementation considerations highlighted by the authors include optimal TTL selection (balancing path diversity against unnecessary traffic), design of the trust‑score algorithm (defining how node behavior metrics are collected, updated, and weighted), and lightweight certificate lifecycle management suitable for power‑constrained, frequently mobile devices.
In conclusion, the Multi‑Path Certification protocol offers a practical and effective solution for secure key exchange in MANETs, addressing the shortcomings of single‑path authentication while maintaining acceptable performance overhead. Future work is suggested to prototype the protocol on actual wireless hardware to measure energy consumption, and to explore integration with blockchain‑based distributed ledgers for immutable credential storage, further strengthening trust in highly dynamic ad‑hoc environments.